Infostealers, including the newly identified AgeoStealer, have become a significant threat, responsible for a large portion of credential theft and data breaches. AgeoStealer employs unique tactics, leveraging gaming platforms for distribution and evading detection through advanced obfuscation techniques. Its ability to extract sensitive information highlights the urgent need for organizations to bolster their defenses against these types of cyber threats. Affected: organizations, gaming platforms, users
Keypoints :
- Infostealers stole 2.1 billion credentials in 2024, contributing to account takeovers and ransomware.
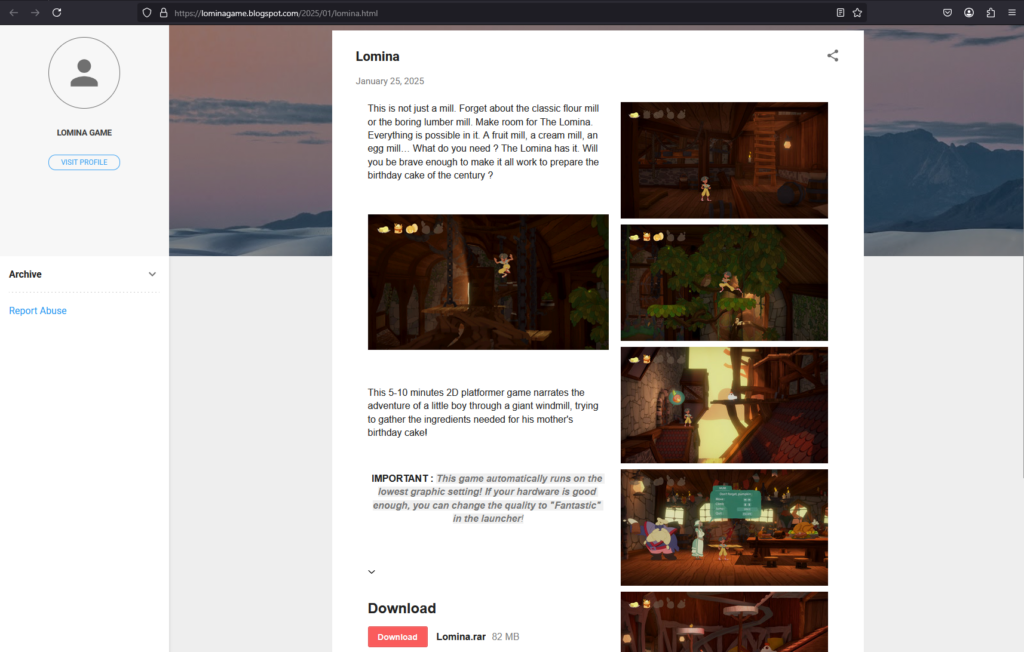
- AgeoStealer is a new strain that targets gamers, using social engineering tactics to engage victims.
- It employs a unique delivery method, utilizing gaming communication platforms to distribute a password-protected ‘game’ containing malware.
- Upon execution, AgeoStealer uses obfuscation techniques to avoid detection.
- The malware scans for sensitive credentials in various browsers, collecting user data for exploitation.
- AgeoStealer exfiltrates stolen data using GoFile.io, ensuring stealthy data transfer without triggering alarms.
- The increasing prevalence of infostealers signifies a rising threat landscape that organizations must prepare for.
MITRE Techniques :
- T1547: Boot or Logon Autostart Execution – Places a shortcut in the startup directory to maintain persistence.
- T1027: Obfuscated Files or Information – Uses obfuscated JavaScript to mask operations and evade detection.
- T1497: Virtualization/Sandbox Evasion – Executes PowerShell commands to terminate processes related to debugging and security tools.
- T1057: Process Discovery – Identifies active browser processes that store sensitive user information for targeted data collection.
- T1560: Archive Collected Data – Gathers sensitive data from various sources, including browser-stored credentials.
- T1567: Exfiltration Over Web Service – Uploads stolen files to GoFile.io using an HTTP POST request for remote access.
Indicator of Compromise :
- [Domain] GoFile.io
Full Story: https://flashpoint.io/blog/ageostealer-how-social-engineering-targets-gamers/