DanaBot, originally identified as a banking trojan in 2018, has evolved into a multifunction malware-as-a-service used by various cybercrime groups and recently resurfaced in 2024 with targeted campaigns in logistics and hospitality sectors. Law enforcement disrupted DanaBot’s infrastructure in May 2025 as part of Operation Endgame, highlighting the malware’s intersection with espionage and cybercrime. #DanaBot #OperationEndgame
Keypoints
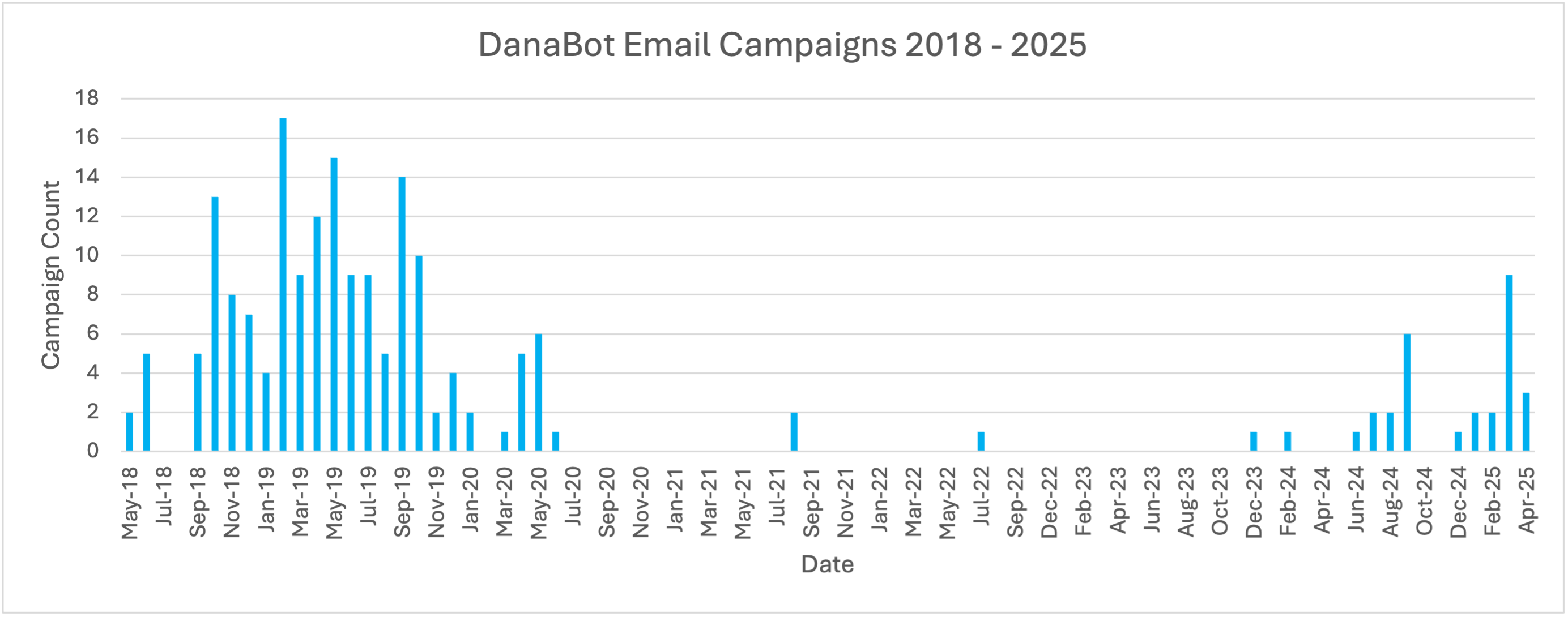
- DanaBot was first identified by Proofpoint in May 2018 as a banking trojan and evolved into a malware loader and information stealer used by multiple cybercriminal groups.
- After declining from mid-2020 to late 2023, DanaBot reemerged in email campaigns in 2024, mainly targeting logistics, transportation, hotel, travel, and hospitality industries.
- Two distinct campaign clusters use DanaBot with different delivery methods: brand impersonation with PowerShell and Peaklight loader in logistics, and reCAPTCHA ClickFix technique in reservation-themed campaigns.
- Espionage campaigns using DanaBot were observed in 2019-2020, targeting government and defense sectors with customized lures mimicking OSCE and Kazakhstani entities, likely aligned with Russian state objectives.
- International law enforcement disrupted DanaBot infrastructure and arrested suspects connected to its development and distribution in May 2025 as part of Operation Endgame.
- Operation Endgame has significantly reduced email campaigns linked to initial access brokers, though threat actors using DanaBot may pivot to other malware payloads amid continued disruptions.
- The blurred line between cybercrime and espionage is illustrated by DanaBot’s dual use in criminal and state-sponsored intelligence gathering operations.
MITRE Techniques
- [T1059] Command and Scripting Interpreter – Utilized PowerShell scripts executed via malicious LNK files and phishing URLs to download and run DanaBot payloads (‘messages contained URLs which resolved to a website with a search:query link that pointed to a Microsoft Shortcut (LNK) file…used PowerShell to download and run an executable’).
- [T1566] Phishing – Employed email campaigns impersonating transportation companies, travel booking firms, OSCE, and government entities to lure victims into executing malware (‘phishing email impersonating a transport company’; ‘messages impersonated the Organization for Security and Co-operation in Europe’).
- [T1140] Deobfuscate/Decode Files or Information – Used password-protected zipped VBS attachments and encoded multi-stage payloads to evade detection and deliver DanaBot (‘messages included password-protected, zipped VBS attachments…that ultimately installed DanaBot’).
- [T1204] User Execution – Relied on victim interaction to run malicious files or scripts, including executing LNK files or copying PowerShell commands, enabling sophisticated social engineering (‘If executed, the LNK file…’; ‘If the user copied and pasted the PowerShell script as instructed’).
- [T1071] Application Layer Protocol – Malicious URLs and web pages used HTTP/S communications to deliver payloads and interaction instructions (‘messages contained URLs that…presented a web page with a Booking themed lure’).
Indicators of Compromise
- [Email Addresses/Senders] Used in campaigns impersonating transport companies, travel firms, and government entities – e.g., Gmail senders in March 2025 reservation campaigns.
- [File Names] Malicious files include Microsoft Shortcut (LNK) files deploying PowerShell scripts, zipped password-protected VBS attachments delivering DanaBot and associated loaders (e.g., Peaklight/Emmenthal Loader).
- [URLs/Domains] URLs leading to phishing landing pages with search:query redirectors and reCAPTCHA ClickFix web pages mimicking Booking sites.
- [Affiliates IDs] Multiple DanaBot affiliate IDs tracked, such as Affid 5, Affid 6 (TA547), Affid 11 (TA564), and Affid 25 associated with espionage campaigns.
- [Payloads] Associated malware includes DanaBot binaries, Peaklight/Emmenthal Loader, Lumma Stealer, StealC, NetSupport, Latrodectus, XWorm, Amadey, DOILoader, and zgRAT.