Rapid7’s MDR detected a ClickFix phishing campaign that used mshta to deliver an HTA embedded in an MSIX-like archive, which executed multi-stage obfuscated PowerShell leading to AMSI bypass and process injection. The report details detection and response actions, the multi-step payload chain, and mitigation advice to monitor RunMRU and contain infected hosts. #ClickFix #Claude
Keypoints
- Rapid7 detected mshta execution via the Windows Run utility (RunMRU), triggering an alert from the rule “Attacker Technique – Remote Payload Execution via Run Utility (shell32.dll)”.
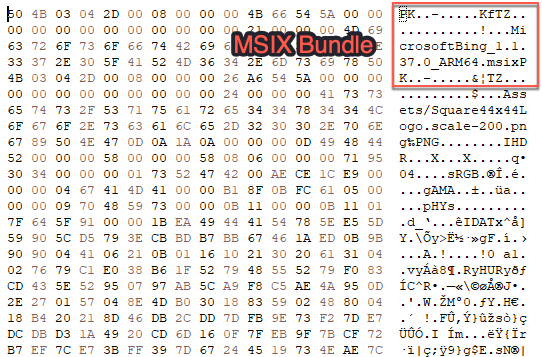
- The malicious payload masqueraded as an MSIX bundle named claude.msixbundle served from a suspicious domain, impersonating the Claude AI installer.
- The MSIX-like archive contained an HTA with obfuscated VBScript that deobfuscated and launched an encoded PowerShell command through cmd and the SysWOW64 PowerShell path.
- The staged PowerShell generated an MD5-based identifier to fetch a larger script, performed string deobfuscation, and used .NET Marshal WriteInt32 to overwrite amsiContext for AMSI bypass.
- Final-stage code performed process injection: XOR-decoded encrypted shellcode was injected using NT API calls (NtAllocateVirtualMemory, NtProtectVirtualMemory, NtCreateThreadEx, etc.).
- Rapid7’s detection engineering and SOC workflows enabled quick detection, containment, retroactive hunts, and development of additional detections; recommended mitigations include monitoring RunMRU, containing unexpected activity, reviewing browsing history, and resetting credentials if infected.
MITRE Techniques
- [T1218.005 ] System Binary Proxy Execution: Mshta – mshta was used via the Windows run utility to execute a remote payload observed in RunMRU; quote: (‘mshta executed on a customer asset using the Windows run utility.’)
- [T1027.013 ] Obfuscated Files or Information: Encrypted/Encoded File – The MSIX-like archive contained an HTA with embedded obfuscated VBScript and encoded PowerShell payloads; quote: (‘Looking at the payload, it does initially appear to be an MSIX bundle… Exploring the payload deeper, however, reveals an HTML Application (HTA) embedded within the ZIP archive’)
- [T1027.010 ] Obfuscated Files or Information: Command Obfuscation – VBScript and PowerShell used string deobfuscation routines and encoded commands to hide execution logic; quote: (‘The Visual Basic script within the HTA file contains a series of obfuscated strings that are deobfuscated with the following VBS function’)
- [T1059.001 ] Command and Scripting Interpreter: PowerShell – Multiple staged PowerShell scripts were downloaded, deobfuscated, and executed, including base64 and custom deobfuscation routines; quote: (‘The encoded PowerShell acts as a staging payload… the script will then call the deobfuscation routine to craft a call to WriteInt32’)
- [T1055 ] Process Injection – The final ScriptBlock performed process injection by allocating memory, changing protections, and creating remote threads to execute XOR-decrypted shellcode via NT APIs; quote: (‘This ScriptBlock culminates in a process injection routine using the .NET interoperability library… the script then obtains handles to the following Windows API calls: NtAllocateVirtualMemory…’)
Indicators of Compromise
- [File name ] Malicious payload and embedded artifact – claude.msixbundle, MicrosoftBing_1.1.37.0_ARM64.msix (string reference inside archive)
- [Domain/URL ] Hosting and download locations – download-version[.]1-5-8[.]com/claude.msixbundle (URL used as mshta argument)
- [Registry key ] Persistence / detection context – RunMRU registry key entries showing mshta commands and Run utility history
- [Embedded artifact ] Script/HTA content – HTA file containing obfuscated VBScript that spawns encoded PowerShell (payload retrieved from the MSIX-like archive)
Read more: https://www.rapid7.com/blog/post/ve-clickfix-phishing-campaign-fake-claude-installer