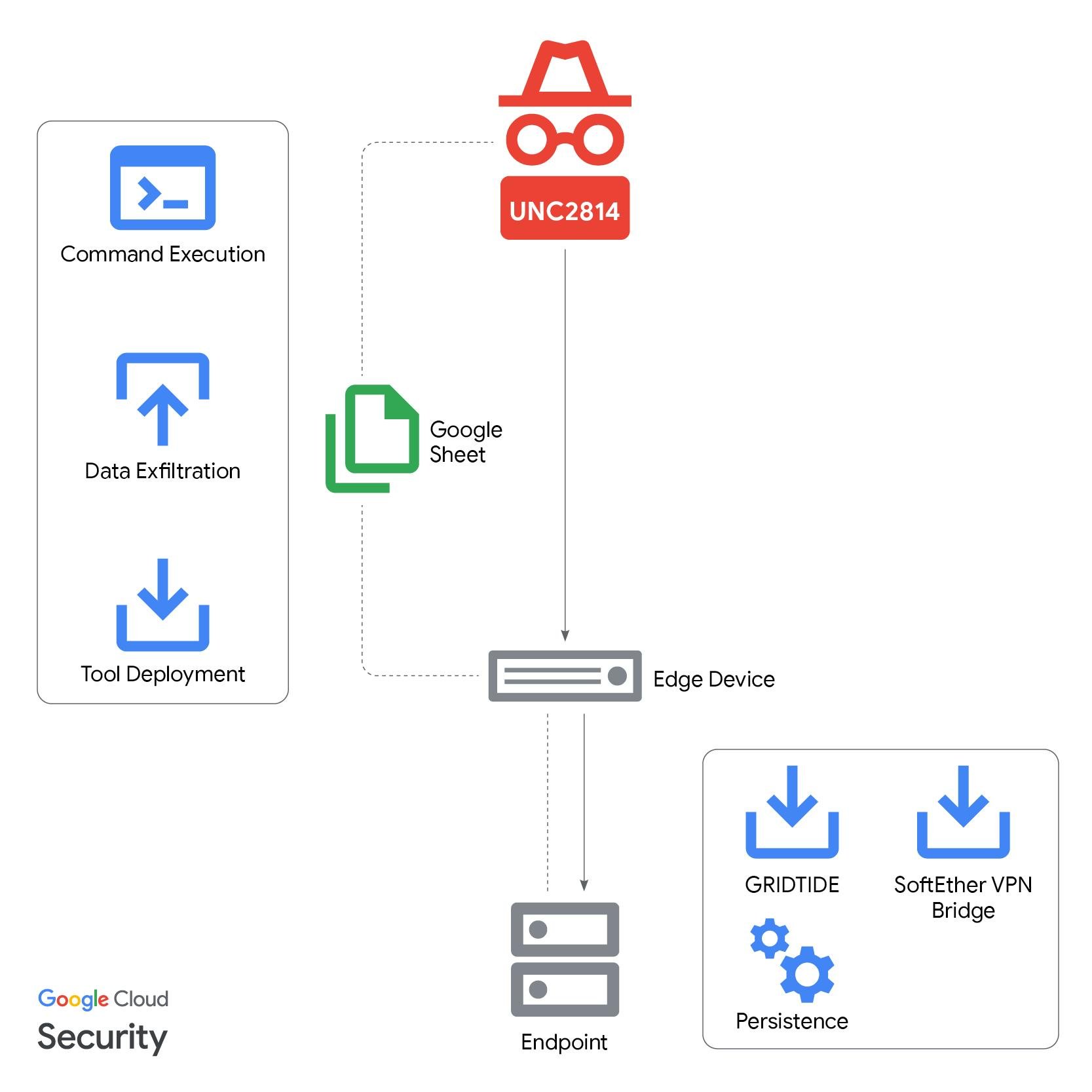
GTIG, Mandiant, and partners disrupted UNC2814’s global espionage campaign that used a novel GRIDTIDE backdoor and abused the Google Sheets API as a covert C2 channel to target telecommunications and government organizations across dozens of countries. The operation terminated attacker-controlled Google Cloud Projects, disabled attacker accounts and infrastructure, and published IOCs to help defenders identify related activity. #UNC2814 #GRIDTIDE
Keypoints
- GTIG, Mandiant, and partners disrupted a long-running PRC-nexus espionage campaign by UNC2814 that had confirmed intrusions in 42 countries and suspected activity in at least 20 more.
- The attacker deployed a novel C-based backdoor called GRIDTIDE that uses Google Sheets API calls as a cell-based C2 channel, hiding commands and data inside spreadsheet cells.
- Operators established persistence via a systemd service (/etc/systemd/system/xapt.service), executed commands with nohup, and used SoftEther VPN Bridge for outbound encrypted connectivity.
- Mandiant detected initial activity on a CentOS host where /var/tmp/xapt spawned a shell and executed ‘sh -c id 2>&1’, indicating privilege escalation to root.
- GRIDTIDE requires a local 16-byte key file (xapt.cfg) to decrypt Google Drive configuration data containing a Google service account and Spreadsheet ID used for C2.
- GTIG’s disruption actions included terminating attacker Google Cloud projects, disabling attacker Google Workspace accounts and Sheets API access, sinkholing domains, issuing victim notifications, and releasing IOCs and detection signatures.
MITRE Techniques
- [T1059.003 ] Command and Scripting Interpreter – GRIDTIDE executed shell commands and used Bash to run actions on the host (e.g., ‘sh -c id 2>&1’).
- [T1021.004 ] Remote Services: SSH – The actor moved laterally using a service account over SSH (‘the threat actor used a service account to move laterally within the environment via SSH’).
- [T1543 ] Create or Modify System Process – The threat actor created a systemd service for persistence at /etc/systemd/system/xapt.service (‘created a service for the malware at /etc/systemd/system/xapt.service’).
- [T1078 ] Valid Accounts – GRIDTIDE relied on a Google service account and associated private key stored in the Drive configuration for API authentication (‘The Google Drive configuration data contains the service account associated with UNC2814’s Google Sheets document’).
- [T1102 ] Web Service – The attacker used Google Sheets API as a high-availability C2 platform to send and receive commands via spreadsheet cells (‘leverages Google Sheets as a high-availability C2 platform’).
- [T1041 ] Exfiltration Over C2 Channel – Host metadata and command output were exfiltrated to spreadsheet cells (e.g., ‘This information is then exfiltrated and stored in cell V1’).
- [T1027 ] Obfuscated Files or Information – GRIDTIDE encoded all data sent and received using a URL-safe Base64 variant to evade detection (‘GRIDTIDE employs a URL-safe Base64 encoding scheme for all data sent and received.’).
- [T1036 ] Masquerading – The payload name ‘xapt’ was used to resemble a legitimate legacy tool to avoid suspicion (‘The payload was likely named xapt to masquerade as the legacy tool used in Debian-based systems.’).
Indicators of Compromise
- [File Hash ] Host artifacts – xapt (ce36a5fc44cbd7de947130b67be9e732a7b4086fb1df98a5afd724087c973b47), xapt.cfg (01fc3bd5a78cd59255a867ffb3dfdd6e0b7713ee90098ea96cc01c640c6495eb), and other hashes (e.g., xapt.service, hamcore.se2).
- [File Name ] Malicious filenames observed on hosts – xapt, xapt.cfg, xapt.service, hamcore.se2, vpn_bridge.config (used for persistence and VPN components).
- [IP Address ] C2 and download hosts – 130[.]94[.]6[.]228 (hosted apt.tar.gz, update.tar.gz, amp.tar.gz), 38[.]60[.]194[.]21 (SoftEtherVPN server), and numerous additional attacker IPs listed.
- [Domain ] C2 domains – 1cv2f3d5s6a9w.ddnsfree.com, admina.freeddns.org, and dozens of other dynamic/abusive domains associated with UNC2814 infrastructure.
- [URL ] Download and API endpoints – http://130[.]94[.]6[.]228/apt.tar.gz (archive containing GRIDTIDE), and Google Sheets API endpoints used for C2 such as https://sheets[.]googleapis[.]com:443/v4/spreadsheets//values/A1?valueRenderOption=FORMULA.
- [User-Agent ] HTTP client strings – Directory API Google-API-Java-Client/2.0.0 Google-HTTP-Java-Client/1.42.3 (gzip) (identified as GRIDTIDE User-Agent).
- [SSL Certificate Hash ] Self-signed certificate – X.509 SHA256 d25024ccea8eac85a9522289cfb709f2ed4e20176dd37855bacc2cd75c995606 (associated with attacker infrastructure).