JSCEAL, an information stealer targeting cryptocurrency application users, evolved in August 2025 to adopt a hardened C2 architecture with single-word domains, standardized .faro and .api subdomains, strict User‑Agent filtering and staged PDF gating to increase stealth. Cato observed the active campaign, noted a refactored PowerShell loader and modified build.zip stages, and reports that the Cato SASE Cloud Platform blocks JSCEAL C2 communication and prevents payload execution #JSCEAL #CatoSASE
Keypoints
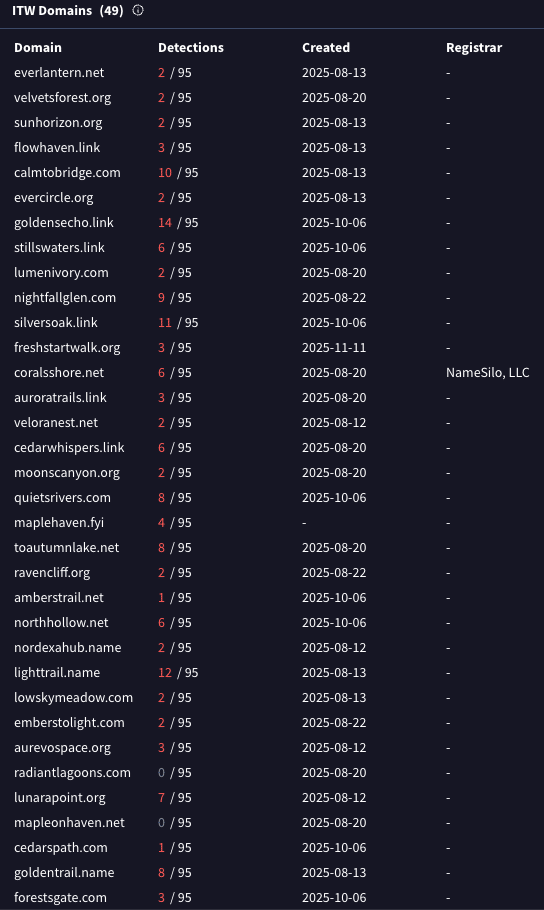
- August 2025 campaign replaced hyphenated multi-word C2 domains with single-word domains (e.g., emberstolight[.]com) and expanded TLD usage (.org, .link, .net, etc.).
- Every new C2 domain exposes two standardized subdomains (.faro and .api), indicating automated, scalable provisioning and a predictable infrastructure pattern.
- Operators implemented strict access controls: servers return HTTP 404 unless the request presents a PowerShell User‑Agent and then respond with a fake PDF to gate further payload retrieval.
- Payload delivery is multi-stage: initial PDF verification followed by a request to the /script endpoint that returns the operational payload and then a modified build.zip containing Node files and native components.
- The PowerShell loader was refactored to use a COM object for Windows Task Scheduler persistence, support multiple payload content types (bytes, JSON, MIME), and reference a single hard-coded domain to reduce fingerprinting.
- Cato telemetry confirmed the infrastructure transition in August 2025 and shows Cato SASE Cloud (NGAM, IPS, XOps) automatically blocking C2 communications and PowerShell-based traffic before payload execution.
MITRE Techniques
- [T1189 ] Drive-by Compromise – Initial access via malicious advertisements that redirected victims to crafted landing pages delivering MSI installers (‘malicious advertisements that redirected victims to crafted landing pages, ultimately delivering MSI installers used to launch the malware’).
- [T1059.001 ] PowerShell – Loader and C2 communication implemented in PowerShell with refactored scripts and hard-coded API domain (‘$API = https://goldensecho.link’).
- [T1071.001 ] Application Layer Protocol: Web Protocols – C2 communications over HTTP/S with strict User‑Agent checks to filter requests (‘Any HTTP request that does not present a PowerShell User-Agent receives an immediate HTTP 404 response’).
- [T1053.005 ] Scheduled Task/Job: Scheduled Task – Persistence via interaction with Windows Task Scheduler using a COM object (‘$TaskService = New-Object -ComObject “Schedule.Service”$TaskService.Connect()’).
- [T1105 ] Ingress Tool Transfer – Multi-stage payload retrieval and download of next-stage archive (build.zip) and components (‘build.zip containing: App.js Preload.js Winpty.dll winpty-agent.exe’).
- [T1027 ] Obfuscated Files or Information – Refactoring and flexible payload handling to reduce static fingerprinting and hinder analysis (‘These changes make the loader more flexible and harder to fingerprint using simple static indicators’).
Indicators of Compromise
- [Domains ] C2 infrastructure and examples of newly observed domains – emberstolight[.]com, goldensecho[.]link, and other 50+ domains listed in the report.
- [Subdomains ] Standardized C2 subdomains used across domains – .faro, .api (consistent exposure across all new C2 domains).
- [File Names ] Next-stage archive and internal files observed in build.zip – build.zip (container), App.js, winpty-agent.exe, and other Node/native files.
- [Hashes ] Notable file hashes associated with observed stages – build.zip: 9615f60ea3cc1c65eb8fe6d77bb85fe6b455503193eab02310a873fccadd332e; PowerShell script: 72af070240c149cda4ad6b6ebb581af4285402d1e2d1ae77dbdb8db41cce3828 (and 2 more script hashes).
Read more: https://www.catonetworks.com/blog/cato-ctrl-deep-dive-into-new-jsceal-infostealer-campaign/