TAG-150 is a growing Malware-as-a-Service operator active since March 2025 that uses two custom families, CastleLoader (a loader) and CastleRAT (a RAT), to run large-scale, modular, multi-stage campaigns primarily targeting the United States. Darktrace observed and contained an early-stage CastleLoader infection that connected to C2 infrastructure at 173.44.141[.]89 by using Autonomous Response to block external connections and enforce a group pattern of life. #TAG-150 #CastleLoader
Keypoints
- TAG-150 has operated since March 2025 as a MaaS operator using two bespoke malware families: CastleLoader (loader) and CastleRAT (RAT), with CastleLoader reported to have infected 469 devices as of May 2025.
- CastleLoader functions as an initial delivery/staging tool that delivers payloads as PEs with embedded shellcode and uses code obfuscation (dead-code insertion, packing) to evade analysis and EDRs.
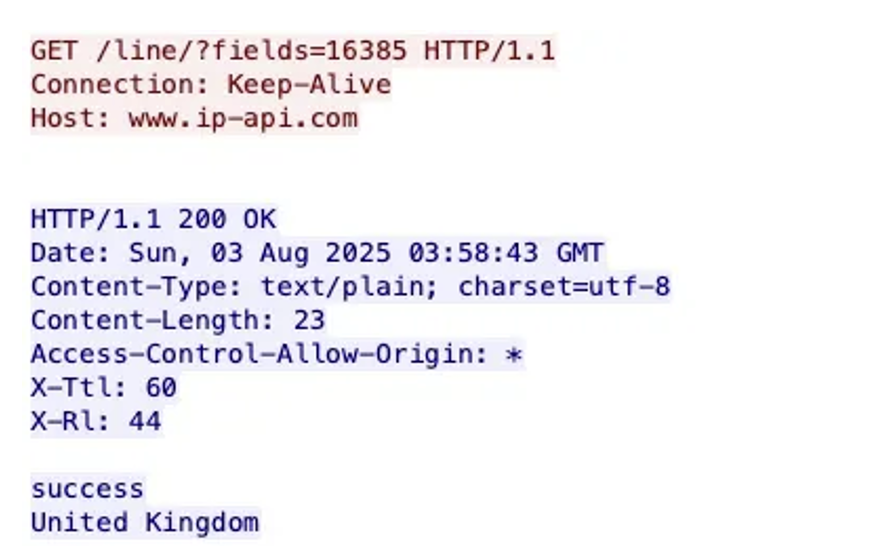
- CastleRAT (including a Python variant “PyNightShade”) is the main payload offering keylogging, screen capture, remote shell, and stealthy communications (PyNightShade showed minimal AV detection and queried ip-api[.]com).
- Attackers employ the “ClickFix” social-engineering technique using spoofed verification or update pages and fake GitHub repositories to trick users into executing PowerShell commands and downloading malware.
- Observed infrastructure includes victim-facing C2 servers, IPs, domains, and malicious URIs (e.g., 173.44.141[.]89 and related download endpoints) used to serve scripts and ZIP payloads containing embedded shellcode.
- Darktrace detected anomalous behavior (rare external IP, unusual user agents, script and ZIP downloads, extensive internal scanning) and used Autonomous Response to block the malicious endpoint and restrict the infected device’s behavior.
- TAG-150’s modular, evolving infrastructure and distribution methods (deceptive domains, fake repos, embedded shellcode) increase intrusion-prevention challenges and enable tailored multi-stage compromises.
MITRE Techniques
- [T15588.001 ] Resource Development – Use of Malware-as-a-Service infrastructure and custom malware families to support operations (‘TAG-150, a relatively new Malware-as-a-Service (MaaS) operator’).
- [TG1599 ] Defence Evasion – Network Boundary Bridging – Use of code obfuscation and packing to hinder analysis and bypass defenses (‘code-obfuscation methods such as dead-code insertion and packing’).
- [T1046 ] Discovery – Network Service Scanning – Post-compromise activity showing extensive internal connections indicative of scanning and reconnaissance (‘high volume of internal connections to a broad range of endpoints, indicating potential scanning activity’).
- [T1189 ] Initial Access – Social-engineering via ClickFix and spoofed verification/update pages to trick victims into executing PowerShell commands and initiating downloads (‘impersonating legitimate software distribution platforms … trick victims into copying and executing PowerShell commands’).
Indicators of Compromise
- [IP ] C2 infrastructure – 173.44.141[.]89 (known CastleLoader/CastleRAT endpoint associated with observed infections).
- [URI ] Malicious download endpoints – 173.44.141[.]89/service/download/data_5x.bin, 173.44.141[.]89/service/download/data_6x.bin (scripts linked to CastleLoader activity).
- [File name ] Payload archive – wsc.zip (observed as a possible payload delivered alongside malicious scripts).
- [Domain / API ] External service used in communications – ip-api[.]com (geolocation API queried by PyNightShade), and spoofed distribution domains using paths like /s.php?an=0 (used in ClickFix distribution flows).
Read more: https://www.darktrace.com/blog/castleloader-castlerat-behind-tag150s-modular-malware-delivery-system