Synacktiv CSIRT analyzed a multi-stage compromise on AWS where a malicious Docker image (kvlnt/vv) led to deployment of vGet (a Rust downloader) and LinkPro, an eBPF-based Linux rootkit that hides via eBPF and ld.so.preload and activates on a specific “magic packet”. The report details LinkPro’s components (Hide and Knock eBPF modules, LD_PRELOAD library, embedded kernel object), communication modes (passive reverse with port-knocking and active forward), IOCs, YARA rules, and MITRE technique mappings. #LinkPro #vShell
Keypoints
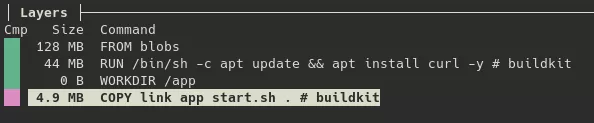
- Initial access was gained through a publicly exposed Jenkins server vulnerable to CVE-2024-23897, which was used to deploy a malicious Docker image (kvlnt/vv) into Kubernetes clusters.
- The kvlnt/vv image contained a VPN/proxy component (vnt) and a Rust downloader named vGet that fetched and executed vShell 4.9.3 in memory from an S3 URL, enabling C2 via WebSocket and DNS tunneling.
- LinkPro is a Golang-developed Linux rootkit embedding multiple ELF modules: an LD_PRELOAD shared library, two eBPF modules (Hide and Knock), and an unused kernel module (arp_diag.ko); it supports passive (reverse) and active (forward) C2 modes.
- In passive mode LinkPro installs XDP (xdp_ingress) and TC (tc_egress) eBPF programs to implement a port-knock “magic packet” (TCP SYN with window 54321) that redirects arbitrary front-end ports to an internal listening port (2233) for one hour.
- The Hide module uses eBPF tracepoint and kretprobe programs to hook getdents and sys_bpf to conceal files, processes, and its own eBPF programs; if unavailable, LinkPro falls back to LD_PRELOAD (libld.so) to hide artifacts in user space.
- LinkPro provides extensive operator functionality (interactive shell, file management, upload/download, reverse SOCKS proxy, reverse HTTP listener) and persistence via a systemd service masquerading as systemd-resolved.
- YARA rules and multiple IOCs (IPs, file paths, embedded hashes, C2 endpoints, URLs) were produced to aid detection; detection may be challenging due to kernel-dependent eBPF behaviors and user-space fallback techniques.
MITRE Techniques
- [T1059.004 ] Command and Scripting Interpreter: Unix Shell – LinkPro executes commands via /bin/sh -c and provides an interactive bash terminal (“…Executes /bin/bash in a pseudo-terminal…”).
- [T1543.002 ] Create or Modify System Process: Systemd Service – LinkPro creates a systemd unit (/etc/systemd/system/systemd-resolveld.service) to persist (“…Enabling the systemd-resolveld service to start when the system boots…”).
- [T1574.006 ] Hijack Execution Flow: Dynamic Linker Hijacking – Uses /etc/ld.so.preload and installs /etc/libld.so to hook libc functions as a fallback concealment mechanism (“…replaces the content of the /etc/ld.so.preload file with /etc/libld.so”).
- [T1036.005 ] Masquerading: Match Legitimate Name or Location – Masquerades as systemd-resolved using /usr/lib/.system/.tmp~data.resolveld and systemd-resolveld.service (“…disguises itself as the systemd-resolved service…”).
- [T1070.006 ] Indicator Removal: Timestomp – Modifies timestamps of persistence files to match /etc/passwd (“…Timestomping the modification date of /usr/lib/.system/.tmp~data.resolveld and /etc/systemd/system/systemd-resolveld.service to that of the /etc/passwd file…”).
- [T1014 ] Rootkit – Uses eBPF hooks on getdents and sys_bpf to hide artifacts at kernel level (“…eBPF programs of the tracepoint and kretprobe types to intercept the getdents… and sys_bpf…”).
- [T1027 ] Obfuscated Files or Information – Data exfiltration uses Base64 and C2 traffic is XOR-encrypted (“…files are Base64-encoded… C2 traffic is XOR-encrypted.”).
- [T1562.007 ] Impair Defenses: Modify System Firewall – XDP processes packets before the regular stack to bypass local firewall rules (“…XDP program bypasses local firewall filters by processing packets before the main network stack.”).
- [T1071 ] Application Layer Protocol – Uses HTTP and DNS (including DNS tunneling) and other protocols for C2 (“…Five communication protocols… HTTP, WebSocket, UDP (raw), TCP (raw), DNS…”).
- [T1205.002 ] Traffic Signaling: Port Knocking – Implements a magic packet (TCP SYN with window 54321) to activate passive C2 (“…magic packet must be a TCP SYN with window size 54321…”).
- [T1090.002 ] Proxy: External Proxy – reverse_connect command sets up a SOCKS5 proxy to relay traffic (“…Sets up a relay to serve as a SOCKS5 proxy tunnel.”).
- [T1105 ] Ingress Tool Transfer – upload_file command downloads tools via HTTP to the host (“…upload_file command allows downloading a file from a server to the infected host…”).
- [T1041 ] Exfiltration Over C2 Channel – download_manage exfiltrates files via the C2 with chunking and Base64 (“…download_manage uses the C2 channel to exfiltrate files… split into 1MB chunks… Base64-encoded…”).
- [T1083 ] File and Directory Discovery – file_manage subcommands are used to explore filesystem and list files (“…file_manage command and its subcommands (list_files, get_current_dir) are used to explore the victim’s filesystem.”).
Indicators of Compromise
- [IP Address ] LinkPro forward-mode C2 – 18.199.101.111 (destination IP for active sample), 56.155.98.37 (vShell C2 observed).
- [URL / Domain ] Downloader and C2 endpoints – https://fixupcount.s3.dualstack.ap-northeast-1.amazonaws[.]com/wehn/rich.png (vGet payload URL), vnt.wherewego.top:29872 (vnt relay), /reverse/handshake ; /reverse/heartbeat ; /reverse/operation (LinkPro reverse URLs).
- [File Path ] Persistence and binaries – /etc/systemd/system/systemd-resolveld.service (malicious service), /usr/lib/.system/.tmp~data.resolveld and /root/.tmp~data.ok (observed LinkPro filenames).
- [File Hash ] LinkPro samples – d5b2202b7308b25bda8e106552dafb8b6e739ca62287ee33ec77abe4016e698b (passive), 1368f3a8a8254feea14af7dc928af6847cab8fcceec4f21e0166843a75e81964 (active).
- [eBPF / Host Artifacts ] BPF maps and keys – conf_map (stores internal port), knock_map (authorized IPs), main_ebpf_progs (programs to hide), pids_to_hide_map (PIDs to hide) — used by Hide/Knock modules to manage state.
Read more: https://www.synacktiv.com/en/publications/linkpro-ebpf-rootkit-analysis