Darktrace analysed a sophisticated DDoS-for-hire campaign dubbed ShadowV2 that uses a Python-based C2 hosted via GitHub Codespaces, a Python spreader with multi-stage Docker deployment for initial access, and a Go-based RAT implementing RESTful registration and polling. The platform includes an OpenAPI/FastAPI backend, a full operator UI, Cloudflare UAM bypass and HTTP/2 rapid reset capabilities enabling large-scale HTTP floods. #ShadowV2 #shadow.aurozacloud.xyz
Keypoints
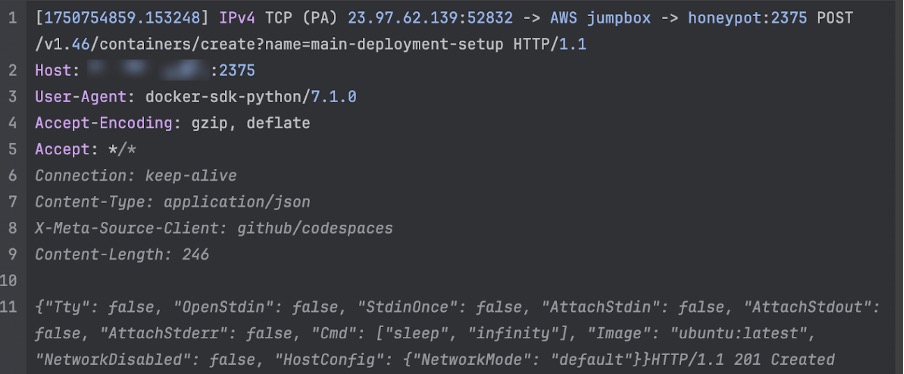
- Initial access is achieved by exploiting exposed Docker daemons (observed on AWS EC2) using a Python spreader executed from GitHub Codespaces (User-Agent: docker-sdk-python/7.1.0, X-Meta-Source-Client: github/codespaces).
- Attackers build tools inside a temporary “setup” container on the victim host, snapshot that container as an image, then deploy the malware with configuration via environment variables to avoid uploading pre-built images.
- The dropped payload is an unstripped Go ELF binary that registers with a Cloudflare-protected C2 (shadow.aurozacloud[.]xyz), derives a VPS_ID, sends heartbeats every second and polls for commands every 5 seconds.
- The Go RAT executes configurable HTTP flood attacks using Valyala’s fasthttp library and supports advanced options: random query strings, spoofed forwarding headers, Cloudflare UAM bypass via headless Chrome, and HTTP/2 rapid reset attacks.
- The C2/API is Python-based (Pydantic/FastAPI) with an exposed OpenAPI/Swagger UI revealing multi-tenant DDoS-for-hire features: authentication, admin/user roles, attack launch endpoints requiring zombie lists, and blacklist management.
- Darktrace observed a real attack command issuing a 120-thread HTTP/2 rapid reset against chache08[.]werkecdn[.]me and confirmed related malware samples (two older submissions) and multiple SHA256 hashes tied to the campaign.
- Defensive implications include the need for deep visibility into containerized/cloud workloads, monitoring anomalous API usage and container orchestration patterns, and hardening Docker daemon exposures.
MITRE Techniques
- [T1505 ] Server Software Component – Use of exposed Docker daemon on AWS EC2 to build and deploy malicious containers on victim hosts (“attacker creates a blank container from an Ubuntu image” / build-on-victim approach).
- [T1071.001 ] Application Layer Protocol: Web Protocols – C2 and API communication over HTTP(S) with POST/GET endpoints for heartbeat and polling (“sends the VPS_ID to hxxps://shadow.aurozacloud[.]xyz/api/vps/heartbeat via POST” and “retrieves hxxps://shadow.aurozacloud[.]xyz/api/vps/poll/ via a GET request”).
- [T1584.006 ] Establish Accounts: Web Services – Use of a multi-tenant DDoS-for-hire platform with authentication, admin/user roles, and user management exposed via the API (“the platform features authentication, distinctions between privilege level (admin vs user) … admin-only user create endpoint”).
- [T1499.001 ] Endpoint Denial of Service: Network Flooding – Execution of large-scale HTTP floods and HTTP/2 rapid reset attacks using fasthttp clients and configurable thread counts (“initiating an attack … using a 120 thread HTTP2 rapid reset attack” and “uses these clients to perform an HTTP flood attack against the target”).
- [T1204.002 ] User Execution: Malicious File – Deployment of a Go ELF binary inside a Docker container dropped to /app/deployment and executed as the implant (“the Docker container acts as a wrapper around a single binary, dropped in /app/deployment”).
- [T1112 ] Modify Registry/Modify Runtime Image – Building tools inside a setup container and then imaging that container to deploy avoids uploading pre-built images and alters the runtime image on the victim (“spawns a generic ‘setup’ container and installs a number of tools within it … this container is then imaged and deployed”).
- [T1027.004 ] Obfuscated Files or Information: Binary Padding/Obfuscation – Inclusion of an unstripped Go binary and use of Cloudflare fronting to obscure C2 hosting and hinder analysis (“the binary is unstripped” and “the server is behind Cloudflare, which obscures its hosting location”).
- [T1203 ] Exploitation for Client Execution – Use of headless Chrome (ChromeDP) to solve Cloudflare UAM JavaScript challenges to obtain clearance cookies for bypassing protections (“the malware will attempt to use a bundled ChromeDP binary to solve the Cloudflare JavaScript challenge … the clearance cookie obtained is then included in subsequent requests”).
Indicators of Compromise
- [Domain ] C2/API domain – shadow.aurozacloud[.]xyz (used for registration, heartbeat, polling, and API endpoints).
- [IP Address ] Spreader origin / GitHub Codespaces attribution – 23.97.62[.]139, 23.97.62[.]136 (Microsoft IPs observed in connections from Codespaces).
- [SHA256 Hash ] Malware samples – 2462467c89b4a62619d0b2957b21876dc4871db41b5d5fe230aa7ad107504c99, 1b552d19a3083572bc433714dfbc2b75eb6930a644696dedd600f9bd755042f6 (and 1f70c78c018175a3e4fa2b3822f1a3bd48a3b923d1fbdeaa5446960ca8133e9c).)
- [Hostname/Target ] Observed attack target – chache08[.]werkecdn[.]me (target of a 120-thread HTTP/2 rapid reset observed during analysis).
- [YARA rule ] Detection signature – Yara rule named ShadowV2 with strings like “shadow-go”, “shadow.aurozacloud.xyz”, and symbols such as “main.registerWithMaster” (provided in article to detect implant).
Read more: https://www.darktrace.com/blog/shadowv2-an-emerging-ddos-for-hire-botnet