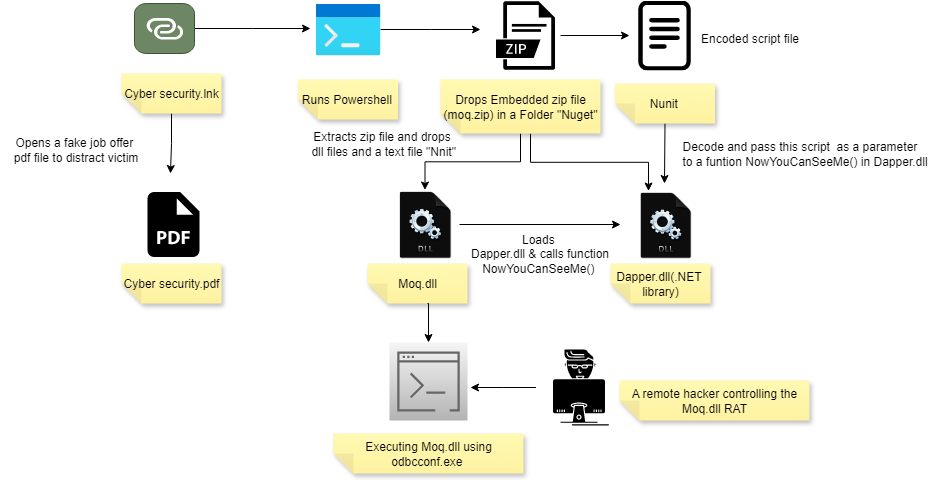
A Windows shortcut (.LNK) distributed via Discord drops a ZIP containing a malicious DLL (Moq.dll) that is executed using the legitimate binary odbcconf.exe, enabling a multi-functional RAT to run stealthily. The RAT disables AMSI and ETW, collects system and antivirus info, captures screenshots, persists via Winlogon Shell modification, and communicates with C2 servers such as hotchichenfly.info. #Moq.dll #odbcconf.exe
Keypoints
- .LNK file delivered via Discord opens a decoy PDF and silently runs a PowerShell payload that extracts and executes a ZIP-contained DLL.
- Moq.dll is a COM DLL that loads supporting .NET libraries (Dapper.dll, Newtonsoft.dll) and executes an obfuscated, AES-encrypted PowerShell script via CLR hosting.
- Attackers abuse the LOLBin odbcconf.exe to register and execute Moq.dll (odbcconf.exe /a {regsvr “C:UsersPublicNugetmoq.dll”}) to evade detection.
- Moq.dll implements AMSI bypass by patching AmsiScanBuffer and disables ETW by patching EtwEventWrite, both via WriteProcessMemory.
- The RAT collects security product info, system details, screenshots, and supports file exfiltration (Dropbox upload) and a C2 command loop with fallback addresses and unique machine IDs.
- Persistence is achieved by appending a PowerShell command to HKCUSOFTWAREMicrosoftWindows NTCurrentVersionWinlogonShell to run at user logon.
- IOCs include multiple file hashes and a hardcoded C2 domain (hotchichenfly.info); supporting artifacts include filenames like Cyber security.lnk, Cyber security.pdf, Moq.dll, and Nuget folder under Public.
MITRE Techniques
- [T1195] Supply Chain Compromise – LNK delivered via Discord with embedded PDF and ZIP payload to trick users and deliver Moq.dll (“when the user clicks the .LNK file named “cyber security.lnk” downloaded from discord,it opens a fake job offer decoy PDF titled “Cyber Security.pdf” and silently executes a PowerShell command”).
- [T1204.002] User Execution: Malicious Link – Shortcut (.LNK) triggers hidden PowerShell and launches conhost.exe in headless mode to avoid user visibility (“it starts a conhost.exe in headless (without console window) mode so that the user can’t see any command prompt window when the link is clicked”).
- [T1218] Signed Binary Proxy Execution (aka LOLBins) – Abuses odbcconf.exe to register and execute Moq.dll (“odbcconf.exe /a {regsvr “C:UsersPublicNugetmoq.dll”}”).
- [T1055] Process Injection – Moq.dll loads Dapper.dll and invokes CLR to run .NET code and inject a decoded script into PowerShell (“Moq.dll invokes CLRCreateInstance … allows native applications to call and run .NET code … Dapper.dll … injects the script in PowerShell command”).
- [T1112] Modify Registry – Persistence by modifying HKCU Winlogon Shell to append the PowerShell command so it runs at user logon (“The script achieves persistence by modifying the registry HKCUSOFTWAREMicrosoftWindows NTCurrentVersionWinlogonShell”).
- [T1056] Input Capture / Screen Capture – Uses Get-MultiPic() to take screenshots, encode to base64 and exfiltrate (“Get-MultiPic () function takes screenshots … converts each screenshot to base64 encoded and sends it to a remote server”).
- [T1027] Obfuscated Files or Information – PowerShell script is heavily obfuscated and AES-encrypted, decrypted at runtime into $decdata (“After deobfuscating the dumped PowerShell script, the content seems encrypted using Advanced Encryption Standard (AES) … the script automatically decrypts the payload and stores the decrypted data in a variable named $decdata”).
- [T1071.001] Web Protocols – C2 communication via hardcoded URLs and fallback addresses (hotchichenfly.info used as C2) (“Defines a unique Bot Id and reads host address … hard coded default C2 URL … Hotchichenfly.info”).
- [T1113] Screen Capture – Captures screenshots and persists failed captures locally for later upload (“Failed captures are saved locally for later sending”).
- [T1562.001] Impair Defenses: Disable or Modify Tools – Patches AmsiScanBuffer to force failure to bypass AMSI (“patches the first 6 bytes of the function with the bytes … forcing the function AmsiScanBuffer to always quit”) and patches EtwEventWrite to disable ETW (“disables Windows Event Tracing (ETW) logging by targeting the EtwEventWrite function … patches the beginning … using WriteProcessMemory”).
Indicators of Compromise
- [File Hash] Malicious DLL hashes – 7391C3D895246DBD5D26BF70F1D8CBAD, 2956ec73ec77757271e612b81ca122c4 (additional hashes listed in article: 5a1d0e02…, 92fc7724…)
- [Domain] C2 domain – hotchichenfly.info (hardcoded C2 URL and shown as main server)
- [File Name / Path] Dropped filenames and folders – C:UsersPublicNugetmoq.dll, Cyber security.lnk, Cyber security.pdf (Nuget folder under Public used to hide payloads)
- [File Artifact] Supporting DLLs and files – Dapper.dll, Newtonsoft.dll, Nunit (Nunit file ~645KB containing encoded strings used as script input)
- [Registry] Persistence registry key – HKCUSOFTWAREMicrosoftWindows NTCurrentVersionWinlogonShell (PowerShell command appended to Shell value)