Sysdig TRT discovered a new Go-based remote access trojan named ZynorRAT that uses a Telegram bot as its command-and-control channel to perform file exfiltration, system enumeration, screenshots, persistence via systemd, process control, and arbitrary shell execution on Linux (with an incomplete Windows build). Analysis of binaries, Telegram chats, VirusTotal submissions, and network telemetry suggests the developer is Turkish, actively refining the RAT, and likely preparing it for sale on underground markets. #ZynorRAT #lraterrorsbot
Keypoints
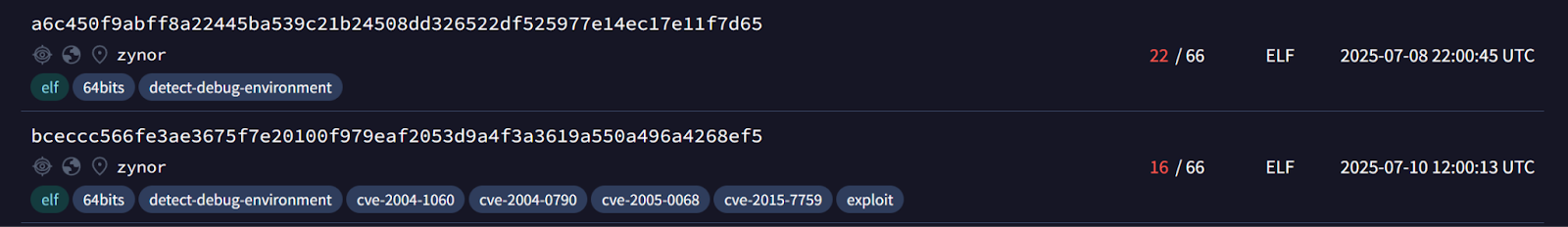
- ZynorRAT is a novel Go-compiled RAT first seen on VirusTotal on July 8, 2025, with samples showing decreasing detection rates after reuploads, indicating active development to evade detection.
- The malware uses a Telegram bot (notably user “lraterrorsbot” / bot named “lrat”) as its primary C2 channel to receive commands and exfiltrate data, including files and screenshots.
- The Linux build contains cleartext symbols and functions for directory listing, process enumeration, file exfiltration, screenshot capture (using kbinani/screenshot), persistence via systemd user services, process killing, and arbitrary shell execution (bash -c).
- Windows builds were compiled with Go but retain Linux-only persistence logic and path usage, suggesting the Windows version is incomplete or in testing.
- Telemetry from Telegram chats and extracted messages revealed many IP addresses (including cloud provider IPs), distribution via Dosya.co, and developer artifacts such as the name “halil” in code and screenshots, supporting Turkish-origin attribution.
- Sysdig released detections including a YARA rule (MAL_ZYNOR) and runtime rules to detect DNS lookups and suspicious domain queries to protect customers from ZynorRAT activity.
- The author appears to be actively testing on cloud instances and may offer ZynorRAT for sale in underground markets once development matures.
MITRE Techniques
- [T1041] Exfiltration Over C2 Channel – ZynorRAT sends files and screenshots to the attacker’s Telegram bot using HTTP multipart requests (“…mime/multipart.(*Writer).CreateFormFile(this,”document”,…)” and “main.sendDocument” to upload documents to Telegram).
- [T1071] Application Layer Protocol – The malware uses the Telegram Bot API over HTTPS as its command-and-control channel (“…’https://api.telegram.org/bot%s/sendMessage?chat_id=%d&text=%s’…’https://api.telegram.org/bot%s/sendDocument’…”).
- [T1016] System Network Configuration Discovery – The handleMetrics function queries an external IP service to determine the victim’s public IP (“…net/http.(*Client).Get(…,”https://api.ipify.org”…)”).
- [T1083] File and Directory Discovery – The /fs_list command triggers handleListDirectory to enumerate directory contents and return them to the C2 (“…handleListDirectory, invoked by the /fs_list command … enumerating directories … concatenated with a newline”).
- [T1105] Ingress Tool Transfer – The attacker distributes executables via a file-sharing service (Dosya.co) where the “zynor” executable was hosted (“…executables are distributed by the attacker using Dosya.co, the executable zynor is still hosted on the website”).
- [T1543] Create or Modify System Process – The malware establishes persistence by creating a systemd user service file at ~/.config/systemd/user/system-audio-manager.service and running “systemctl –user daemon-reload” to load it (“…creates a service file … systemctl –user daemon-reload”).
- [T1059] Command and Scripting Interpreter – Fallback behavior executes arbitrary commands received from the C2 using bash -c, enabling remote code execution (“…if input does not match commands … executed by default with bash -c “).
- [T1036] Masquerading (Service names/paths) – The persistence service uses a benign-sounding unit name and executable path (System Audio Core Service, /home/user/.local/bin/audio) to blend in (“[Unit] Description=System Audio Core Service … ExecStart=/home/user/.local/bin/audio”).
Indicators of Compromise
- [File Hash – Linux] analyzed ELF sample and other Linux builds – bceccc566fe3ae3675f7e20100f979eaf2053d9a4f3a3619a550a496a4268ef5, and 6 other Linux hashes (e.g., 237a40e5…), and 2 more hashes.
- [File Hash – Windows] Windows executable hash examples – 037e5fe028a60604523b840794d06c8f70a9c523a832a97ecaaccd9f419e364a47338da…, (Windows sample listed in IoCs).
- [Domain] C2 / API endpoints – api.telegram.org used for bot communication and document uploads (“https://api.telegram.org/bot…/sendMessage”, “https://api.telegram.org/bot…/sendDocument”).
- [File name / Distribution] distributed filename and host – “zynor” executable hosted on Dosya.co (file-sharing distribution observed).
- [Paths] Persistence artifact path – systemd user service file at ~/.config/systemd/user/system-audio-manager.service and launcher path /home/user/.local/bin/audio.
- [IP Addresses] IP addresses observed in Telegram messages – examples include 34.139.81.65 (Google LLC), 176.88.126.219 (Superonline), 176.238.224.71 (Turkcell); many other cloud and Turkish IPs were reported (dozens listed in article).