Seqrite Labs APT-Team uncovered a campaign by a threat group dubbed Noisy Bear targeting KazMunaiGas employees in Kazakhstan using spear-phishing emails with a ZIP attachment that dropped a malicious LNK downloader, BATCH scripts, PowerShell “DOWNSHELL” loaders, and a reflective DLL implant to achieve remote shell access. The actor hosted tools (including Metasploit components) on sanctioned hosting (Aeza Group LLC) and used Russian-language artefacts and infrastructure patterns suggesting possible Russian origin. #NoisyBear #KazMunaiGas
Keypoints
- Campaign timeline: tracked since April 2025 and observed targeting KazMunaiGas (KMG) employees in May 2025 via spear-phishing with a compromised business email.
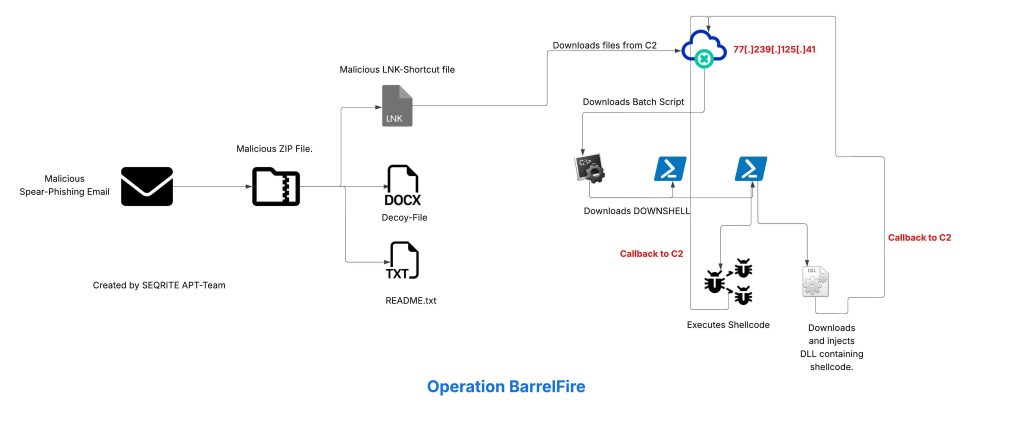
- Delivery: emails contained a ZIP (Schedule.zip) with a decoy document and a malicious shortcut График зарплат.lnk (Salary Schedule.lnk) that invoked powershell.exe to download payloads.
- Multi-stage infection chain: LNK → downloads 123.bat/it.bat → BATCH scripts download PowerShell loaders (support.ps1, a.ps1) → DOWNSHELL uses AMSI bypass and reflective/memory techniques → DLL implant injected via process hollowing/thread-context hijack to spawn a reverse shell.
- Technical capabilities: AMSI tampering via reflection, dynamic API resolution, in-memory delegate creation, CreateRemoteThread and reflective injection, thread context hijacking via rundll32.exe with RWX allocation.
- Infrastructure: payloads and open-source red-team tools (Metasploit/PowerSploit) hosted on servers including 77[.]239[.]125[.]41 and domains like wellfitplan[.]ru; hosting linked to Aeza Group LLC.
- Attribution indicators: Russian-language comments, use of sanctioned Russian-hosting provider, and TTP overlap with Russian actors suggest probable Russian origin for Noisy Bear.
- IOCs provided: multiple SHA-256 hashes for Outlook, ZIP, LNK, batch, PowerShell, and DLL files along with IPs/domains for hunting and detection.
MITRE Techniques
- [T1589.002 ] Gather Victim Identity Information: Email Addresses – attacker used a compromised business email of a KMG finance employee to send spear-phishing messages (‘a compromised business email was used to deliver a malicious ZIP file’).
- [T1204.002 ] User Execution: Malicious File – targets were instructed to open a ZIP and execute the LNK file График зарплат which launched the infection chain (‘open a file known as График зарплат which translates to Salary Schedule’).
- [T1078.002 ] Valid Accounts: Domain Accounts – the campaign leveraged a compromised internal business email account to send malicious messages (‘the threat actor used a compromised business email of an individual working in Finance Department of KazMunaiGas’).
- [T1059.001 ] Command and Scripting Interpreter: PowerShell – multiple PowerShell loaders (support.ps1, a.ps1) were used to execute and load payloads and perform AMSI bypass and in-memory operations (‘downloaded PowerShell loaders, which we have dubbed as DOWNSHELL’).
- [T1059.000 ] Command and Scripting Interpreter (other) – batch scripts (123.bat, it.bat) were used to orchestrate downloading and execution of PowerShell loaders (‘downloading PowerShell Loaders … once they are downloaded, it then sleeps’).
- [T1562 ] Impair Defenses – AMSI tampering via reflection was employed to flip an internal AMSI initialization flag preventing scanning (‘resolves the internal type System.Management.Automation.AmsiUtils … changing or flipping this flag convinces PowerShell that the AMSI has failed to initialize’).
- [T1027.007 ] Dynamic API Resolution – script dynamically retrieved function addresses from loaded modules using unsafe native methods to call WinAPI without Add-Type/DllImport (‘LookUpFunc dynamically retrieves the memory address of any exported function … without using traditional DllImport or Add-Type’).
- [T1027.013 ] Encrypted/Encoded File – payloads and scripts used obfuscation/concatenation techniques to evade static detection (‘uses a little operand shenanigan to avoid static signature detection, but concatenation of the string literals’).
- [T1055.003 ] Thread Execution Hijacking – DLL implant performed thread-context hijacking on a suspended rundll32.exe primary thread to execute injected shellcode (‘calls GetThreadContext … SetThreadContext, and finally calls ResumeThread so execution continues at the injected shellcode’).
- [T1620 ] Reflective Code Loading – PowerShell-based reflective loading techniques and commented reflective DLL injection (PowerSploit) were observed to load code into target processes without touching disk (‘some part of this is commented, which performs Reflective DLL injection into remote process … using PowerSploit’).
- [T1218.011 ] System Binary Proxy Execution: Rundll32 – the implant spawned rundll32.exe in suspended mode as the host for code injection and execution (‘it spawns a rundll32.exe process in a suspended manner’).
- [T1105 ] Ingress Tool Transfer – initial downloader stages retrieved batch and PowerShell scripts and additional tooling from remote servers (e.g., 77[.]239[.]125[.]41) (‘it downloads a malicious batch script known as 123.bat, from a remote-server … support.ps1 and a.ps1’).
- [T1567.002 ] Exfiltration to Cloud Storage – exfiltration technique listed in report’s MITRE mapping (no detailed steps in text but included in campaign mapping) (‘Exfiltration to Cloud Storage’).
Indicators of Compromise
- [IP ] C2/download host – 77[.]239[.]125[.]41 (used to host/download 123.bat and other payloads).
- [Domain ] malicious/hosting domains – wellfitplan[.]ru (hosting related web apps and tooling), and other hosted apps on Aeza Group LLC infrastructure.
- [File Hash – Outlook ] spear-phish Outlook file – 5168a1e22ee969db7cea0d3e9eb64db4a0c648eee43da8bacf4c7126f58f0386.
- [File Hash – ZIP ] malicous ZIP archives – 021b3d53fe113d014a9700488e31a6fb5e16cb02227de5309f6f93affa4515a6, f5e7dc5149c453b98d05b73cad7ac1c42b381f72b6f7203546c789f4e750eb26.
- [File Hash – LNK ] shortcut droppers – a40e7eb0cb176d2278c4ab02c4657f9034573ac83cee4cde38096028f243119c, 26f009351f4c645ad4df3c1708f74ae2e5f8d22f3b0bbb4568347a2a72651bee.
- [File Hash – Scripts ] batch/PowerShell loaders – batch: d48aeb6afcc5a3834b3e4ca9e0672b61f9d945dd41046c9aaf782382a6044f97, 1eecfc1c607be3891e955846c7da70b0109db9f9fdf01de45916d3727bff96e0; PowerShell: da98b0cbcd784879ba38503946898d747ade08ace1d4f38d0fb966703e078bbf, 6d6006eb2baa75712bfe867bf5e4f09288a7d860a4623a4176338993b9ddfb4b, fb0f7c35a58a02473f26aabea4f682e2e483db84b606db2eca36aa6c7e7d9cf8.
- [File Hash – DLL ] implant binary – 1bfe65acbb9e509f80efcfe04b23daf31381e8b95a98112b81c9a080bdd65a2d.
Read more: https://www.seqrite.com/blog/operation-barrelfire-noisybear-kazakhstan-oil-gas-sector/