Attackers used a fake AnyDesk installer that leverages a Cloudflare Turnstile lure, the Windows search-ms protocol, and an SMB-hosted LNK disguised as a PDF to deliver an MSI that installs MetaStealer. The campaign collects victim hostnames via %COMPUTERNAME% subdomains and uses a Private EXE Protector-protected dropper (ls26.exe) connecting to multiple C2 domains and an IP. #MetaStealer #anydeesk[.]ink
Keypoints
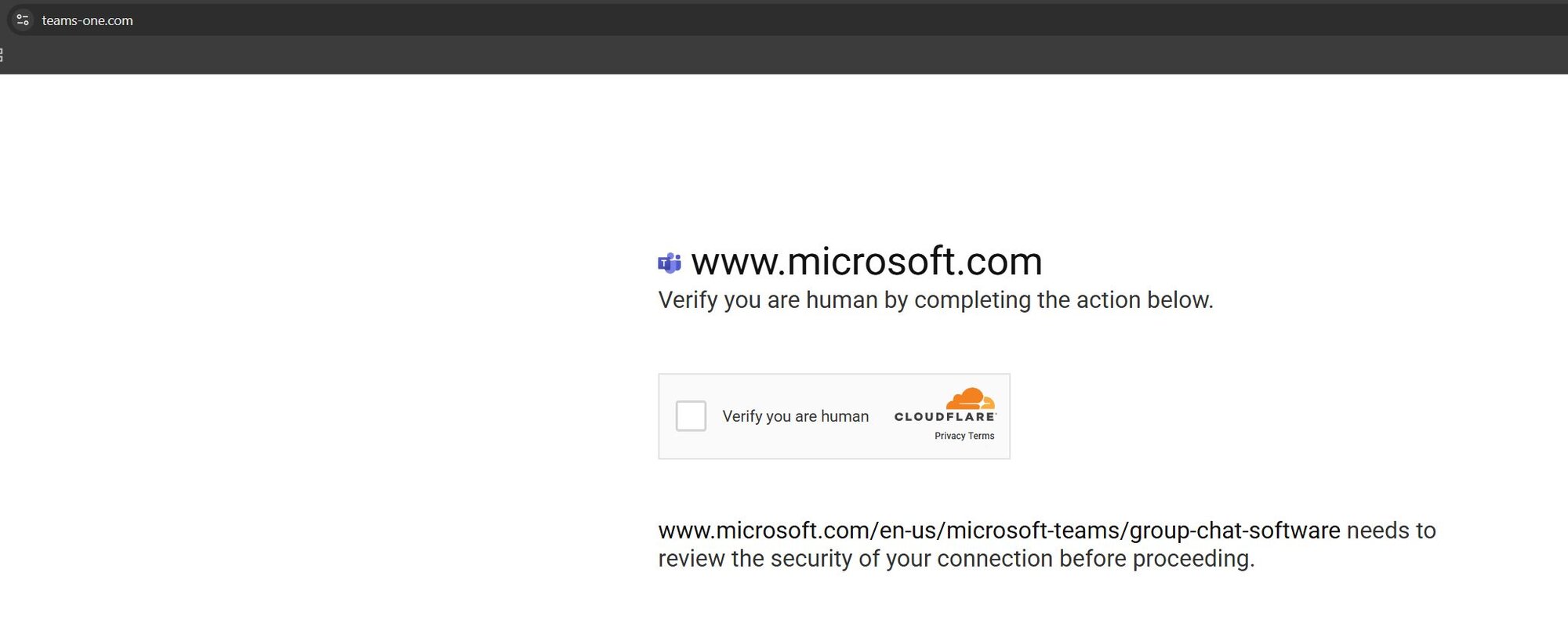
- Attackers hosted a fake AnyDesk download page that displays a Cloudflare Turnstile to socially engineer victims into initiating the chain.
- The landing page’s obfuscated JavaScript redirects to a search-ms URI, causing Windows File Explorer to open a remote SMB share.
- Victims see a .LNK file disguised as “Readme Anydesk.pdf” which, when opened, triggers cmd.exe to download a legitimate AnyDesk installer and a malicious MSI.
- The MSI contains a CustomActionDLL and a CAB (Binary.bz.WrappedSetupProgram) holding 1.js (cleanup) and ls26.exe, the MetaStealer dropper.
- The fake “PDF” captures the victim hostname by using the %COMPUTERNAME% environment variable as a subdomain to exfiltrate identifying info.
- MetaStealer (ls26.exe) is a large, Private EXE Protector-protected binary with behavior consistent with credential and crypto-wallet theft.
- Campaign infrastructure includes multiple C2 domains and an IP address; variants of ClickFix/FileFix indicate evolving attacker techniques beyond classic Run-dialog paste prompts.
MITRE Techniques
- [T1204 ] User Execution – Victim is tricked into opening a disguised LNK file (“Readme Anydesk.pdf”) that executes cmd.exe and initiates downloads (‘…victims are presented with a Windows shortcut LNK file; however, this LNK file is disguised as a PDF file called Readme Anydesk.pdf.’).
- [T1218 ] System Binary Proxy Execution – The attack uses msiexec to install an MSI package masquerading as a PDF (‘…The fake PDF is then installed by msiexec (revealing that it’s actually an MSI package) …’).
- [T1105 ] Ingress Tool Transfer – The chain downloads multiple components (AnyDesk installer, MSI, DLL, CAB, ls26.exe) from attacker-controlled hosts such as chat1[.]store (‘…it also begins a download for another purported “PDF,” which is downloaded from chat1[.]store and dropped into the temporary directory.’).
- [T1021 ] Remote Services (SMB) – The search-ms redirect points Windows File Explorer to an attacker-controlled SMB share hosting the malicious LNK (‘…Windows File Explorer then directs the victim to an attacker-controlled SMB share …’).
- [T1082 ] System Information Discovery – The malicious MSI/installer captures the %COMPUTERNAME% environment variable and uses it as a subdomain to collect the victim hostname (‘…this fake PDF is configured to grab the %COMPUTERNAME% environment variable as a subdomain.’).
- [T1055 ] Process Injection / Obfuscation (Packaging/Protection) – The MetaStealer dropper is protected with Private EXE Protector to hinder analysis (‘…ls26.exe is a very large binary and is protected with Private EXE Protector.’).
Indicators of Compromise
- [Domain ] fake Cloudflare Turnstile landing page – anydeesk[.]ink/download/anydesk[.]html
- [Domain ] MSI/dropper hosting and C2 – chat1[.]store (hosting MSI contents), macawiwmaacckuow[.]xyz, yeosyyyaewokgioa[.]xyz, cmqsqomiwwksmcsw[.]xyz
- [IP Address ] MetaStealer C2 – 38[.]134[.]148[.]74
- [File ] MetaStealer dropper – ls26.exe (SHA256: 0fc76b7f06aa80a43abafc1e9b88348734e327feb306d700c877c6a210fbd5e7)
- [File ] MSI package components – CustomActionDLL (SHA256: fd622cf73ea951a6de631063aba856487d77745dd1500adca61902b8dde56fe1), Binary.bz.WrappedSetupProgram CAB (SHA256: 513992d7076984d5c5a42affc12b6a00eef820f3254af75c9958ef3310190317)
Read more: https://www.huntress.com/blog/fake-anydesk-clickfix-metastealer-malware