The article describes a PowerShell-based loader that allocates executable memory, copies two shellcode payloads from dropped files, and invokes them via CallWindowProcA instead of creating a new thread to evade EDR detection. The initial dropper is a Windows executable with SHA256 ec8ec8b3234ceeefbf74b2dc4914d5d6f7685655f6f33f2226e2a1d80e7ad488 and it loads payloads from files under %APPDATA%Cafeterias108butikscenters. #ec8ec8b3234ceeefbf74b2dc4914d5d6f7685655f6f33f2226e2a1d80e7ad488 #CallWindowProcA
Keypoints
- The Windows executable (SHA256 ec8ec8b3…) drops a PowerShell script and two obfuscated data files under %APPDATA%Cafeterias108butikscenters.
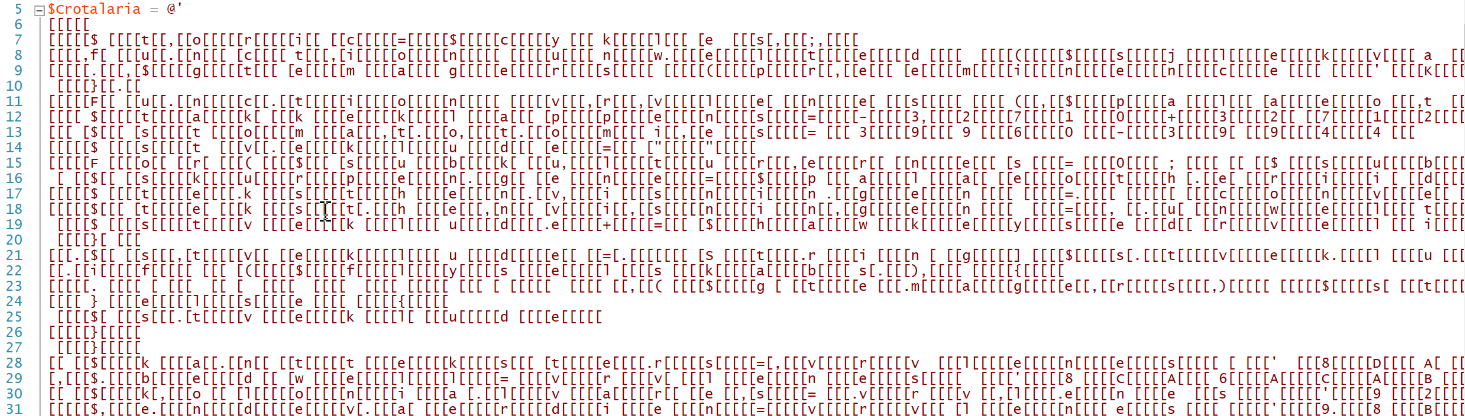
- The PowerShell script reads the second dropped file and extracts a short IEX token, then deobfuscates strings and resolves native APIs such as VirtualAlloc via delegates.
- The script allocates two executable memory regions, copies two shellcode payloads from the dumped file at specific offsets (offset 2048, size 7119 for the first), and prepares them for execution.
- Instead of CreateThread/NtCreateThreadEx, the script obtains a function pointer and invokes CallWindowProcA through a delegate to execute the shellcode in the current GUI thread.
- Using CallWindowProcA avoids creating a new thread and blends with benign GUI behavior, making detection by EDRs that monitor thread creation more difficult.
- Debugger analysis confirmed memory allocation addresses and that the shellcode is invoked at the function-pointer argument of CallWindowProcA, though the sample crashed during testing.
- The technique demonstrates attackers leveraging “exotic” legitimate APIs to run shellcode and evade common behavioral detections.
MITRE Techniques
- [T1055 ] Process Injection – The script allocates executable memory, copies shellcode into the current process memory and executes it via CallWindowProcA, effectively injecting and executing code in-process. Quote: ‘The shell code is extracted at offset 2048 (size 7119 bytes) and copied to the address returned by the first call to VirtualAlloc()’
- [T1106 ] Native API – The PowerShell resolves and invokes native Win32 APIs (VirtualAlloc, CallWindowProcA) through delegates to perform memory allocation and transfer execution. Quote: ‘$global:integrity = $geparders.Invoke(0, 7119, $heterographical, $direktrstolene)’
- [T1059.001 ] PowerShell – The loader uses obfuscated PowerShell with Invoke-Expression (IEX) to deobfuscate and execute the loader logic and API-resolution code. Quote: ‘IEX (or “Invoke-Expression”) is never good news in PowerShell scripts!’
- [T1204.002 ] User Execution: Malicious File – A user-executed Windows executable drops the PowerShell script and data files into AppData to trigger the PowerShell loader. Quote: ‘The PowerShell script is dropped by a Windows executable (SHA256:ec8ec8b3…)’
Indicators of Compromise
- [File Hash ] dropper executable – ec8ec8b3234ceeefbf74b2dc4914d5d6f7685655f6f33f2226e2a1d80e7ad488
- [File Path ] dropped PowerShell and data files – C:UsersREMAppDataRoamingCafeterias108butikscentersSkydeprammenesBogskrivninger70.Mde, C:UsersREMAppDataRoamingCafeterias108butikscentersNonrepentancemenneskevrdige.Paa
- [API / Function ] techniques observed – CallWindowProcA used to execute shellcode, VirtualAlloc used to allocate executable memory
- [Bytes/Offsets ] shellcode extraction – first shellcode at offset 2048 size 7119, second payload located at offset 2048+7119 (and other payload sizes)
Read more: https://isc.sans.edu/diary/Interesting+Technique+to+Launch+a+Shellcode/32238