Threat actors increasingly abuse VPS providers (e.g., Hyonix, Host Universal, Mevspace, Hivelocity) to conduct SaaS-targeted campaigns—enabling stealthy logins, inbox rule manipulation, email deletion, and phishing while evading geolocation and IP-reputation defenses. Darktrace observed coordinated compromises across customers involving rare VPS IP logins, MFA bypasses or token claims, obfuscated email rules, and domain fluxing leading to spam/outbound phishing. #Hyonix #HostUniversal
Keypoints
- VPS providers (notably Hyonix, Host Universal, Mevspace, Hivelocity) are being used as low-cost, anonymous infrastructure to mimic legitimate local traffic and evade defenses.
- Darktrace detected a March–May 2025 spike in anomalous activity from ASN AS931 (Hyonix) including brute-force attempts, anomalous logins, and inbox-rule related phishing.
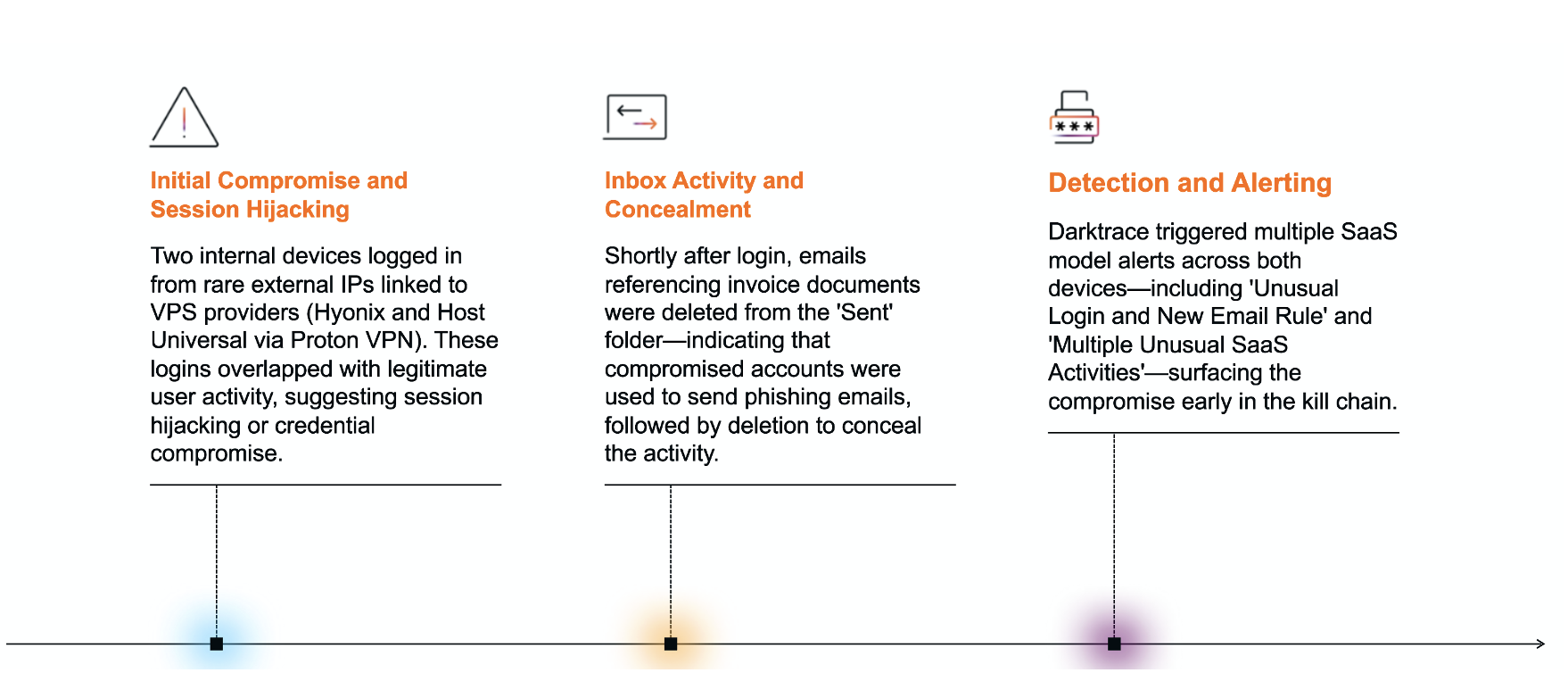
- Case 1: simultaneous logins from rare VPS IPs and legitimate user activity indicated session hijacking, followed by deletion of sent phishing emails.
- Case 2: coordinated logins from multiple VPS providers, MFA satisfied via token claims, creation of obfuscated inbox rules, and attempts to modify account recovery settings.
- Attack persistence tactics included vague inbox rule names, targeted deletion of emails (e.g., invoice-related), and mirrored rule creation across users suggesting shared infrastructure.
- Network indicators included domain fluxing and a suspicious file write (‘SplashtopStreamer.exe’) to a domain controller, implying potential remote access or lateral movement.
- Autonomous Response was not enabled in affected environments; had it been active, Darktrace could have automatically blocked unusual VPS endpoints to halt escalation.
MITRE Techniques
- [T1566 ] Phishing – Initial access likely via phishing/spearphishing attachments as noted (“Initial access in this case was likely achieved through a similar phishing or account hijacking method”).
- [T1078 ] Valid Accounts – Execution by using hijacked/valid accounts to log in from rare VPS endpoints (“logins from rare external IPs associated with VPS providers”).
- [T1098 ] Account Manipulation – Persistence through creating/modifying account settings and inbox rules (“creation of inbox rules with obfuscated names” and “User registered security info”).
- [T1098.002 ] Exchange Email Rules – Persistence specifically via Exchange/email rule creation to delete or redirect messages (“new inbox rules…automatically deleted” targeting VIP-shared document emails).
- [T1071 ] Application Layer Protocol – C2 via web protocols and DNS domain fluxing to maintain infrastructure (“DNS requests…to a suspicious domain” and “domain fluxing”).
- [T1071.001 ] Web Protocols – Use of web protocols for command-and-control and malicious communications (“DNS requests from a device to a suspicious domain”).
- [T1036 ] Masquerading – Defense evasion by blending activity with legitimate behavior and using clean/new VPS infrastructure (“mimicking local traffic, evade IP reputation checks with clean, newly provisioned infrastructure”).
- [T1562 ] Impair Defenses – Disabling or modifying defensive tools/visibility implied by deleting emails and obfuscating rules (“deleting emails…suggesting an attempt to hide phishing emails”).
- [T1562.001 ] Disable or Modify Tools – Specific impairment of visibility by altering mailbox content/rules to avoid detection (“creation of inbox rules with obfuscated names” and deletion of sent items).
- [T1556 ] Modify Authentication Process – Credential access techniques to bypass or modify authentication (“MFA satisfied via token claims, further indicating session hijacking”).
- [T1556.004 ] MFA Bypass – Sub-technique used where MFA was satisfied via token claims consistent with session hijacking (“MFA satisfied via token claims”).
- [T1087 ] Account Discovery – Discovery through account and security info updates observed (“User registered security info” and account recovery modifications).
- [T1531 ] Account Access Removal – Impact via attempts to modify or remove account recovery/access controls (“attempts to modify account recovery settings” and password/security info changes from rare IPs).
Indicators of Compromise
- [IP ] VPS and rare login IPs associated with attacks – 38.240.42.160 (Hyonix AS931), 103.75.11.134 (Host Universal / Proton VPN).
- [IP ] Additional suspicious login IPs – 38.255.57.212 (Hyonix used during MFA), 91.223.3.147 (Mevspace Poland used in multiple logins).
- [IPv6 ] VPS login IPv6 example – 2a02:748:4000:18:0:1:170b:2524 (Hivelocity VPS used in logins and MFA activity).
- [File name ] Potential malicious binary observed – SplashtopStreamer.exe written to a domain controller (possible remote access usage).
- [Domain ] Suspicious domain activity – DNS requests and domain fluxing observed (suspicious domain used prior to email compromise; multiple rotating IP resolutions).
- [Other ] Network/provider context – AS931 (Hyonix), AS7922 (COMCAST-7922) and AS54290 (HOSTWINDS) referenced for rare login attribution.