From Sept–Dec 2024 JPCERT/CC observed incidents using CrossC2 (a C/C++-based Cross-platform Cobalt Strike Beacon/builder) together with tools like PsExec, Plink, SystemBC, and a custom Nim loader dubbed ReadNimeLoader to deploy Cobalt Strike Beacons across multiple countries. The campaign shows overlaps with BlackBasta-related infrastructure and techniques, and JPCERT/CC published a CrossC2 config parser to aid analysis. #CrossC2 #ReadNimeLoader
Keypoints
- JPCERT/CC confirmed incidents where CrossC2 was used to create Cobalt Strike Beacons for Linux/macOS, with attacks observed Sept–Dec 2024.
- Attackers used CrossC2 plus tools such as PsExec, Plink, SystemBC (ELF), GetNPUsers, and Cobalt Strike to target AD and perform lateral movement.
- ReadNimeLoader (Nim, distributed as jli.dll via DLL sideloading of java.exe) acted as a loader: decrypting readme.txt (OdinLdr or Beacon), decoding and executing Beacon in memory.
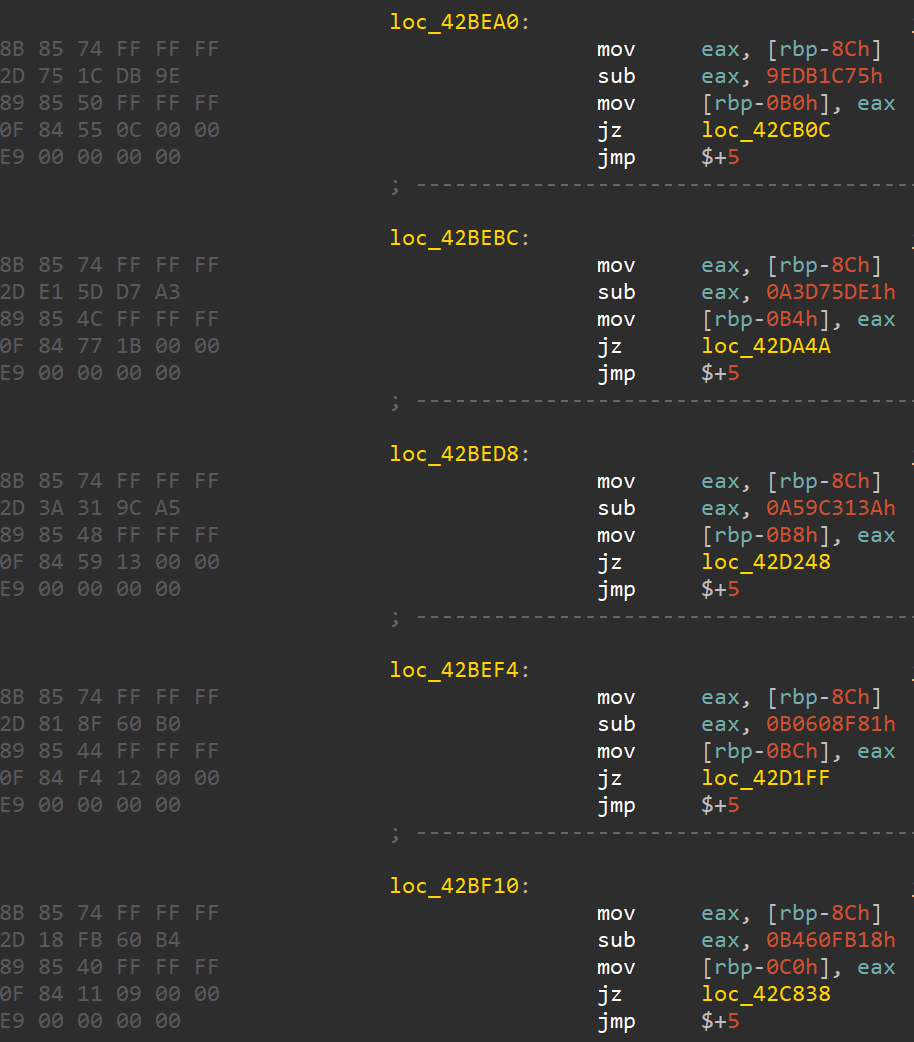
- ReadNimeLoader and CrossC2 include multiple anti-analysis measures (string XOR, junk code, debug detection, timing checks, encrypted configs/AES), complicating analysis.
- OdinLdr decrypts and periodically re-encrypts Cobalt Strike Beacon in heap (marker “OdinLdr1337”); some samples run Beacon directly, others via OdinLdr.
- Appendices include C2 servers, malware SHA256 hashes, and Cobalt Strike configuration examples; JPCERT/CC published a CrossC2 config parser on GitHub.
- Attribution: overlaps with BlackBasta (shared C2 domain, filenames jli.dll/readme.txt, use of SystemBC and AS-REP techniques) noted but not definitive.
MITRE Techniques
- [T1055 ] Process Injection – ReadNimeLoader/OdinLdr decode and execute Cobalt Strike Beacon in memory via shellcode loader (OdinLdr) and re-encrypts beacon in heap (“…decrypts the internally encoded Cobalt Strike Beacon and runs it in memory…”).
- [T1218 ] Signed Binary Proxy Execution (Sideloading) – DLL sideloading of jli.dll by legitimate java.exe to load ReadNimeLoader (“…initiated by a legitimate java.exe file… This java.exe loads jli.dll through DLL sideloading.”).
- [T1547.001 ] Create or Modify System Process: Windows Service – Task Scheduler used to register a job to execute java.exe for persistence (“…executed from a Task Scheduler job registered by the attacker.”).
- [T1071.001 ] Application Layer Protocol: Web Protocols – Cobalt Strike Beacon configured for HTTPS beaconing to specified C2 servers (“BeaconType – HTTPS … C2Server – 64.95.10[.]209,…”).
- [T1105 ] Ingress Tool Transfer – Use of CrossC2 builder (public GitHub) and transfer of tools/binaries (CrossC2, ReadNimeLoader, OdinLdr, SystemBC) to target (“…builder is publicly available on GitHub… ReadNimeLoader, OdinLdr, SystemBC…”).
- [T1086 ] PowerShell (ProcSpawn alternative) – Use of legitimate system binaries to spawn process paths (spawnto powercfg.exe specified) for executing payloads (“Spawnto_x86 – %windir%syswow64powercfg.exe”).
- [T1110 ] Brute Force / Credential Access (AS-REP Roasting) – Use of GetNPUsers to perform AS-REP Roasting when attacking Active Directory (“…GetNPUsers, often leveraged in AS-REP Roasting attacks…”).
- [T1036 ] Masquerading – Use of legitimate filenames and locations (java.exe, jli.dll, readme.txt, placement under C:$recycle.bin) to blend payloads (“…All related files… were located under “C:$recycle.bin”…”).
Indicators of Compromise
- [IP ] C2 servers used for HTTPS beaconing – 64.95.10[.]209:443, 64.52.80[.]62:443 (and other C2s listed in Appendix D such as 162.33.179[.]247:8443).
- [Domain ] Malicious domains resolved/used – api.glazeceramics[.]com:443, doc.docu-duplicator[.]com:53 (and doc2/doc3 variants).
- [File Hash – ReadNimeLoader ] ReadNimeLoader (jli.dll) SHA256 examples – 56b941f6dcb769ae6d6995412559012abab830f05d5d8acf2648f7fa48c20833, dfe79b9c57cfb9fc10597b43af1c0a798991b6ceeec2af9b1e0ed46e6a8661c8 (and other jli.dll hashes listed).
- [File Hash – Cobalt Strike payloads ] readme.txt (encoded Beacon) SHA256 examples – 6246fb5c8b714707ac49ade53e6fe5017d96442db393b1c0ba964698ae24245d, acdf2a87ed03f2c6fe1d9899e8a74e8b56f7b77bb8aed5adf2cc374ee5465168.
- [File Names ] Loader/executable filenames observed – jli.dll (ReadNimeLoader), java.exe (legitimate binary used for sideloading), readme.txt (encrypted payload) — all placed under C:$recycle.bin on affected hosts.
Read more: https://blogs.jpcert.or.jp/en/2025/08/crossc2.html