A new Android banking Trojan named “Customer Help Service.apk” targets Indian banking users by stealing sensitive data and redirecting calls through a hardcoded number. The malware employs unique features such as call forwarding manipulation and comprehensive data collection, including SMS, calls, and OTPs, to facilitate financial fraud. #SpyBanker #CustomerHelpService #IndianBanks
Keypoints
- The malware, named “Customer Help Service.apk,” targets Indian banking users and is distributed potentially via WhatsApp.
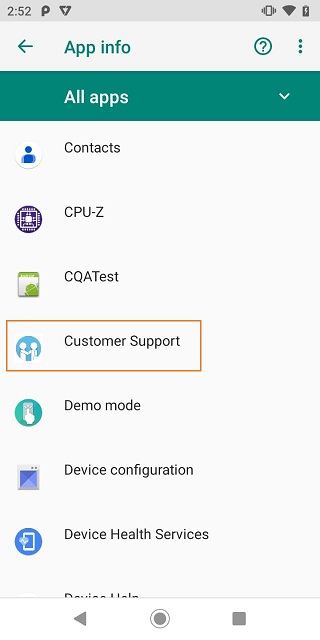
- The app bypasses normal visibility by not appearing in the app drawer and runs in the background using registered broadcast receivers for SMS and device boot events.
- It manipulates call forwarding by setting a hardcoded number controlled by attackers to intercept unattended calls.
- The malware collects detailed SIM information, SMS messages (including OTPs), call logs, and emails, storing data in Firebase Database.
- It features a unique single layout that dynamically changes based on the selected bank from a dropdown, targeting numerous Indian banks.
- The malware uses permissions to evade battery optimization, listen to notifications, and read/send SMS and calls covertly.
- Users are advised to download apps only from the Play Store, review permissions regularly, and report financial fraud through the Indian government’s initiative.
MITRE Techniques
- [T1404] User Execution – The malware coerces installation via WhatsApp by unclear methods, possibly vishing or phishing (‘victim has been unknowingly coerced into installing via WhatsApp’).
- [T1543.003] Create or Modify System Process: Windows Service – Registers a service called “CallForwardingService” to modify the call forwarding number (‘registering a service called “CallForwardingService” and redirects the user’s calls’).
- [T1056.001] Input Capture: Keylogging – Collects SMS and OTPs using notification listeners (‘collects all the SMS received, the OTPs received via SMS, Calls, Emails via notification listeners’).
- [T1621] Multi-Factor Authentication Interception – Intercepts OTPs and banking information for financial fraud (‘collects victims’ sensitive banking information and OTPs affecting the victims’ financial stability’).
- [T1036.005] Masquerading: Match Legitimate Name or Location – The malware hides from app drawer by not registering launcher intent (‘does not hold any space in the app drawer list’).
- [T1592] Gather Victim Network Information – Collects SIM details to enable further attacks (‘collects the SIM details of the user’).
Indicators of Compromise
- [APK Name] The malicious APK identified – Customer Help Service.apk
- [File Hash] SHA-1 hash of the malware APK – E40FC8b4ed62ebe096b80edb6a8c8dfa
- [Detection Name] Antivirus detection alias – Trojan ( 001140e1 )
Read more: https://labs.k7computing.com/index.php/android-spybanker-rerouting-calls-to-attackers/