Despite Microsoft’s enhanced security measures blocking macros in Office files downloaded from the internet, macros remain an effective tool for attackers due to widespread use of outdated Office versions and human error. CERT-AGID recently identified a targeted email campaign spreading Formbook malware through spoofed documents linked to a major Italian energy company. #Formbook #CERTAGID #MicrosoftOffice
Keypoints
- Microsoft implemented default macro blocking for Office files via Mark of the Web, but macros still pose a threat.
- Macros remain effective, especially due to the large use of outdated or unpatched MS Office versions and user mistakes.
- CERT-AGID identified a recent targeted email campaign spreading Formbook malware to prospective clients of an Italian energy company.
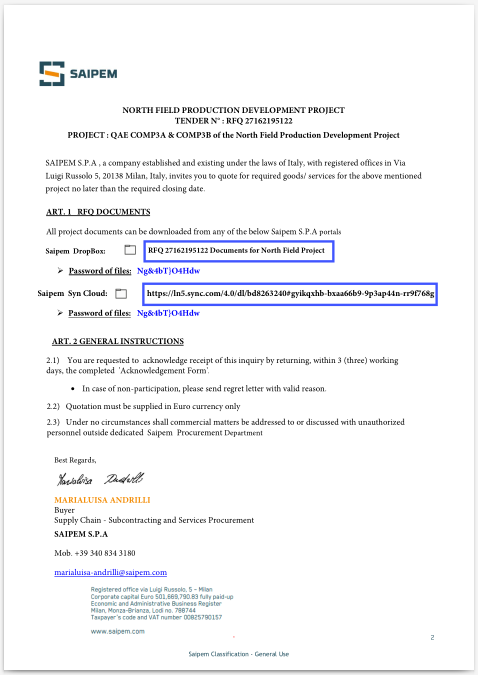
- The attack starts with a PDF containing the company’s logo and links to password-protected project documents hosted on file-sharing platforms.
- After downloading and extracting password-protected ZIP archives, users find Office documents, some with malicious macros.
- These macros lead to a staged infection chain downloading components from recently registered fake domains and compromised legitimate Italian domains.
- The campaign exploits realistic business contexts to lower user defenses rather than relying on complex technical methods.
MITRE Techniques
- [T1204] User Execution – The campaign relies on user opening documents containing malicious macros, exploiting human error (“…execution of malicious content from macros embedded in DOC and XLSB files…”).
- [T1105] Ingress Tool Transfer – Downloading malicious components from recently registered fraudulent domains and compromised legitimate domains (“…download and execution of malicious components from newly registered and compromised domains…”).
Indicators of Compromise
- [File Types] Malicious Office documents with macros – DOC and XLSB files inside password-protected ZIP archives.
- [Domains] Recently registered fraudulent domains and compromised legitimate Italian domains – used to host malware components.
- [Attachment] PDF file containing company logo and links to password-protected project documents hosted on file-sharing platforms.