Cybercriminals are increasingly abusing legitimate Inno Setup installers by embedding malicious payloads using Pascal scripting to evade detection and deliver information-stealing malware such as RedLine Stealer. This campaign employs sophisticated evasion techniques including debugger checks, sandbox avoidance, DLL sideloading, and command obfuscation to persist on infected systems and steal sensitive data. #InnoSetup #HijackLoader #RedLineStealer
Keypoints
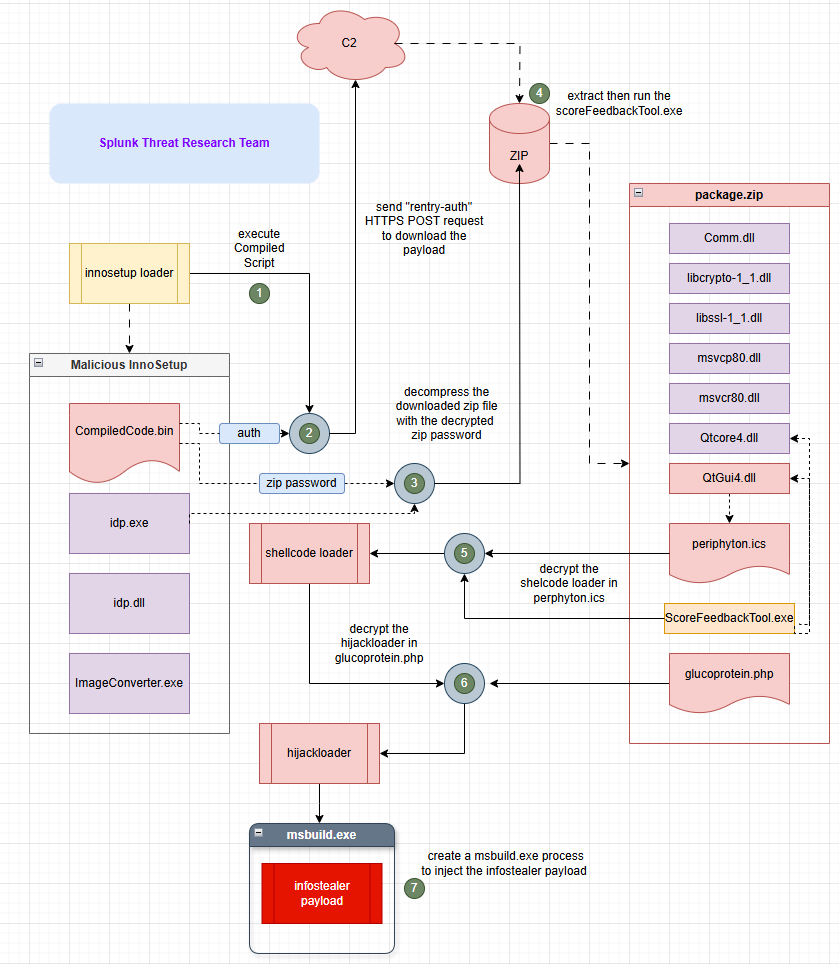
- Inno Setup installers are leveraged by threat actors to disguise and deliver malware via embedded Pascal scripts.
- The malicious loader uses debugger and sandbox evasion techniques to avoid detection, including process checks and filename pattern verification.
- The infection chain involves downloading a compressed payload extracted with a renamed 7za.exe, and establishing persistence via hidden scheduled tasks.
- HijackLoader is used as a modular loader to decrypt and execute the final payload, RedLine Stealer, through DLL sideloading and process injection.
- RedLine Stealer employs advanced obfuscation methods such as constant unfolding and disables browser security features to facilitate credential and cryptocurrency wallet theft.
- The campaign abuses web services like TinyURL and rentry[.]org with access tokens to conceal malicious payload delivery URLs.
- Splunk provides multiple analytic detections to identify each stage of this threat, from loader activity to final payload execution.
MITRE Techniques
- [T1622] Debugger Evasion – The malicious Pascal script uses XOR encryption and WMI queries to detect and terminate if malware analysis tools are present (“Select * From Win32_Process where Name=”).
- [T1497] Sandbox Evasion – Checks file name patterns and system info via WMI to avoid triggering in sandbox environments.
- [T1071.001] Web Protocols – Uses TinyURL shortened links and authenticated requests with custom headers (rentry-auth) to retrieve next-stage payloads.
- [T1027.015] Compression – Employs renamed 7za.exe (idp.exe) to extract encrypted and password-protected payload archives.
- [T1053] Scheduled Task/Job – Creates hidden scheduled tasks that execute the malware on system reboot for persistence.
- [T1574.001] Hijack Execution Flow: DLL Sideloading – Loads trojanized DLLs (QtGuid4.dll) via legitimate executables to decrypt and execute shellcode.
- [T1027] Obfuscated Files or Information – Conceals modular loader components inside manipulated PNG-like files using XOR decryption and compression.
- [T1127.001] MSBuild – Injects decrypted final payload into MSBuild.exe process to obscure execution.
- [T1027.010] Command Obfuscation – Uses constant unfolding obfuscation to dynamically build parameters and evade static detection.
- [T1497] Browser Sandbox Evasion – Launches Chrome with –no-sandbox and –user-data-dir flags to evade browser security sandboxing.
- [T1562.001] Disable or Modify Tools – Runs Internet Explorer with -extoff flag to disable extensions and security addons during malicious activity.
- [T1047] Windows Management Instrumentation – Uses WMI queries to gather detailed system info for profiling and evasion.
- [T1555.003] Credentials from Web Browsers – Targets browser stored credentials and cryptocurrency wallet extensions to steal data.
Indicators of Compromise
- [File Hashes] Malicious Inno Setup Loader – 0d5311014c66423261d1069fda108dab33673bd68d697e22adb096db05d851b70, 0ee63776197a80de42e164314cea55453aa24d8eabca0b481f778eba7215c1601, and 2 more hashes.
- [File Names] Loader components and persistence files – idp.dll, idp.exe (renamed 7za.exe), ImageConverter.exe (decoy), taskshostw.exe (hidden executable for scheduled task), QtGuid4.dll (trojanized DLL), periphyton.ics (encrypted shellcode), glucoprotein.php (encrypted HijackLoader).
- [Domains/URLs] Payload download locations – TinyURL shortened link to rentry[.]org with authentication header, hxxp[:]//aptechludhiana[.]com/temp/package[.]zip as next-stage payload archive.
- [Scheduled Task] Hidden scheduled task named WhatsAppSyncTaskMachineCore – registered using schtasks.exe with XML task file “lang.”
- [Browser User Data Paths] Targets include Chromium-based browsers data directories such as %USERPROFILE%AppDataLocalGoogleChromeUser Data and multiple other browser profiles.
Read more: https://www.splunk.com/en_us/blog/security/inno-setup-malware-redline-stealer-campaign.html