Validin provides extensive HTTP/S response data that enables threat analysts to discover related malicious domains and infrastructure by pivoting on features like favicon hashes, HTTP redirects, and HTML content. The platform helps identify phishing campaigns, malicious browser extension C2 domains, and fake app download sites through detailed feature correlation and exploration. #Validin #ClickFix #MaliciousExtensions #PhishingDomains
Keypoints
- Validin processes approximately 10,000 virtual and IP host HTTP/S response measurements per second, offering broad visibility into domain and IP response features.
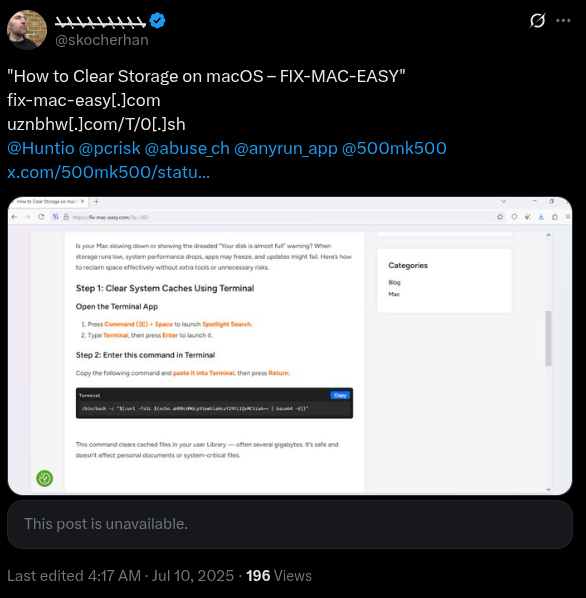
- Favicon hash pivoting identified previously unreported domains and IPs related to the MacOS ClickFix phishing campaign.
- HTTP redirect headers helped discover related domains configured to redirect to a common tracking domain, indicating coordinated malicious infrastructure.
- HTTP body hash pivoting uncovered nearly 300 domains linked to malicious Chrome and Edge browser extension command and control servers.
- HTML title tag pivots revealed multiple domains involved in distributing fake applications related to a remote access tool lure.
- Many flagged domains share similar HTTP response fingerprints and were registered recently on the same registrar, suggesting common threat actor management.
- Validin’s feature pivoting capabilities enable proactive, comprehensive intelligence gathering for blocking and detecting emerging phishing and malware threats.
MITRE Techniques
- [T1190] Exploit Public-Facing Application – Attackers used phishing domains with similar HTTP response features to exploit users by masquerading as legitimate MacOS repair services (“…pivoting on the favicon hash 5412dda9e4ae4f6a20278c12a620ac4c…”).
- [T1071] Application Layer Protocol – Malicious browser extensions communicated with command and control domains using HTTP requests identified through HTTP body hash pivoting (“…click.videocontrolls[.]com…HOST-BODY_SHA1 pivot…”).
- [T1598] Phishing – The campaign employed fake event invitations that prompt downloads of malicious remote access tools, detected via HTML title tag analysis (“…fake eventbrite invitation that prompts a download of the Altera remote access tool…”).
- [T1090] Proxy – HTTP redirection was used by phishing domains to mask final payload delivery domains (“…lure domain redirects to mlpro-trckr[.]com before finally redirecting to mystery-box-rush[.]click…”).
Indicators of Compromise
- [Domains] Phishing and malicious infrastructure – fixitanywhere[.]com, captainacefrahm[.]com, admitclick[.]net, quickfindsrc[.]com, superiorurl[.]net, and dozens more related domains.
- [IP Addresses] Related to malicious favicon pivoting – 194.164.64[.]52, 151.106.96[.]4.
- [File Hashes] HTTP response fingerprints suggesting common management – dd0130ee69ca5997b23f, dd0175e9ae26da26f66e, dd01ae950b600d5bd3e6.
- [HTML Body SHA1] Identical HTTP response bodies used as pivots – 539b0037602495bc1c16c2fb85a32913f14ae12f.
Read more: https://www.validin.com/blog/http_feature_pivoting/