The MITRE Corporation’s April 2025 update introduced seven new threat groups along with associated IoCs, revealing new insights through expanded data analysis by WhoisXML API. The analysis uncovered numerous additional domains, IPs, and email-connected domains linked to these groups, enhancing threat detection capabilities. #APT42 #BlackByte #RedEcho #SeaTurtle #Storm1811 #VelvetAnt
Keypoints
- MITRE released seven new threat groups in April 2025, listing extensive domain and IP IoCs for APT42, BlackByte, RedEcho, Salt Typhoon, Sea Turtle, Storm-1811, and Velvet Ant.
- WhoisXML API expanded the IoC lists, identifying additional malicious domains, IP addresses, and email-connected domains related to these groups.
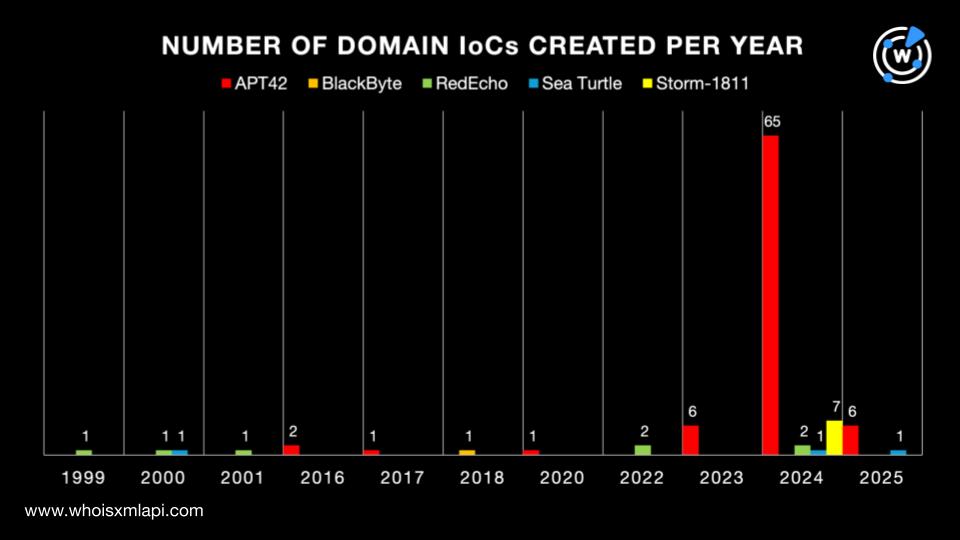
- Domain WHOIS analysis showed varying creation dates and registrar distributions across the groups with Namecheap and Vitalwerks among leading registrars.
- Geolocation of IP IoCs revealed concentrations in countries like Germany, Netherlands, China, and the U.S., with various ISPs administering these IPs.
- Historical DNS data demonstrated thousands of domain-to-IP and IP-to-domain resolutions, confirming long-term activity and infrastructure usage by these groups.
- Analysis of network flow data identified command-and-control servers and victim interactions tied to specific IP addresses linked to the threat actors.
- Additional findings include 638 email-connected domains, six of which are malicious, expanding threat intelligence and detection capabilities for defense teams.
MITRE Techniques
- [No specific MITRE ATT&CK techniques were mentioned or detailed in this article.]
Indicators of Compromise
- [Domain] 189 identified IoCs with varying creation dates and registrar distribution, examples include acconut-signin[.]com (APT42), alteksecurity[.]org (BlackByte), astudycarsceu[.]net (RedEcho)
- [IP Address] 109 identified IoCs geolocated across multiple countries, examples include 207[.]38[.]70[.]29 (APT42), 185[.]93[.]6[.]31 (BlackByte), 101[.]78[.]177[.]227 (RedEcho)
- [Email-connected Domains] 638 additional domains discovered via public email addresses, six confirmed malicious such as account-logins[.]com and mailer-daemon[.]net
- [Autonomous System Numbers] AS data linked to C&C servers including ASN 61272 (unknown ISP) and ASN 1299 (Arelion)
Read more: https://circleid.com/posts/new-mitre-attck-groups-for-2025-a-dns-deep-dive