DTEX has updated its Insider Threat Advisory highlighting evolved tactics used by DPRK IT workers to infiltrate organizations globally and evade detection, particularly through behavioral and technological indicators. These activities impact corporate insider threat detection, remote access infrastructure, and recruitment systems worldwide. #DPRK #InsiderThreat #RemoteAccess
Keypoints
- The DPRK RevGen Initiative involves skilled DPRK IT workers securing employment under false identities to fund weapons and missile programs, with expanding operations beyond the U.S. into Europe and other regions.
- New behavioral indicators include anomalous creation of multiple online identities, unusual banking and crypto site access, and use of multiple remote access tools and anti-screen locking utilities to mask activity.
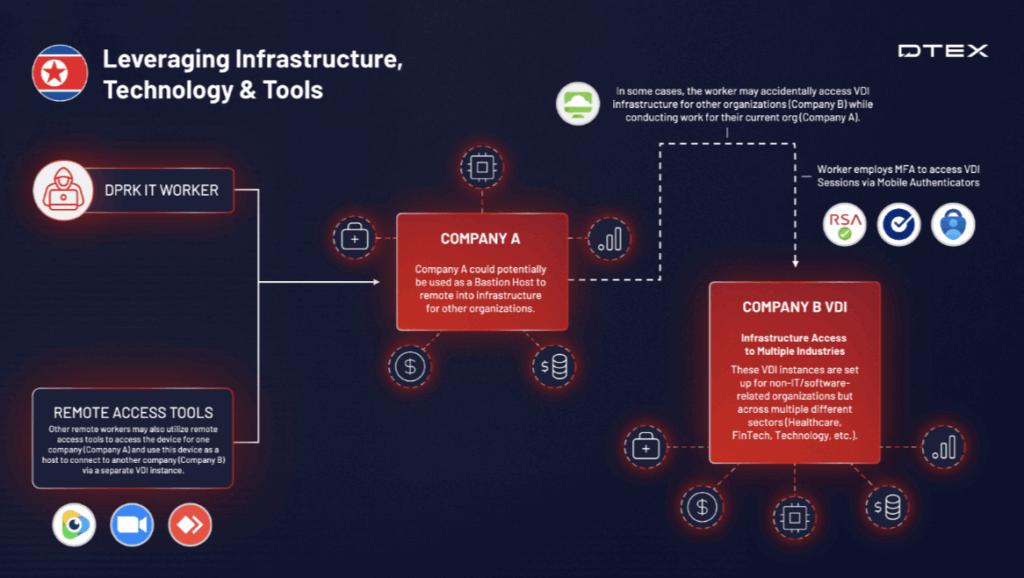
- Operational tactics include circumventing zero-trust network access tools, lateral movement between companies using VDI, and malicious use of live video streaming software to obfuscate multiple users on video calls.
- Text files containing passwords and authentication data are commonly stored on desktops to facilitate handover between DPRK workers managing multiple jobs.
- Performance and behavioral anomalies like lack of collaboration, high-volume odd-hour system access, and excessive working hours are key non-technical indicators tied to DPRK operatives.
- Recommended defenses include strict remote access policies, enhanced vetting and background checks, insider threat monitoring tools, and ongoing threat intelligence integration with national security agencies.
- Technical IOCs such as suspicious email addresses linked to DPRK IT workers and specific IP-based KVM devices (e.g., TinyPilot) have been identified for investigative use.
MITRE Techniques
- [T1562.001] Disable or Modify System Firewall – Observed circumvention of zero-trust network access tools (SASE) like Zscaler and Netskope to enable unfettered remote access (‘Secure Access Service Edge tools have been observed being disabled to create a more permissive environment’).
- [T1076] Remote Desktop Protocol – Use of multiple legitimate remote access and video conferencing tools including Zoom and WebEx to maintain persistent access and avoid detection (‘video conferencing applications… leveraged as remote access tools through screen sharing and control capabilities’).
- [T1087.001] Account Discovery: Local Account – Anomalous creation and access of multiple online identities for recruitment and operational purposes (‘using multiple email, banking, crypto, freelance, or other online aliases other than the individual’s name’).
- [T1021.001] Remote Services: Remote Desktop Protocol – Lateral movement using VDI platforms such as VMware Horizon and Citrix XenDesktop between organizations was reported (‘using privileged access from one organization to break into and access another’).
- [T1566] Phishing – While not explicitly detailed, recruitment via fraudulent credentials and home country broker fronting interviews imply targeted social engineering techniques integrated into the campaign.
Indicators of Compromise
- [Email Addresses] DPRK IT worker associated email IOCs – multiple confirmed suspicious corporate and personal email addresses used for infiltration and recruitment, notable for detection in HR and recruitment platforms.
- [Device Identifiers] KVM Over IP Devices – TinyPilot USB device identifiers used to facilitate undetected remote control access across infected endpoints.
- [Network Indicators] IP addresses with anomalous geolocation patterns – including access from Belarussian or Russian linked Gmail accounts and unusual UDP communications with known malicious hostnames.
- [File Names] Text files containing passwords – commonly found on desktops or common folders used to share credentials among DPRK workers.
Read more: https://www.dtexsystems.com/resources/i3-threat-advisory-inside-the-dprk/