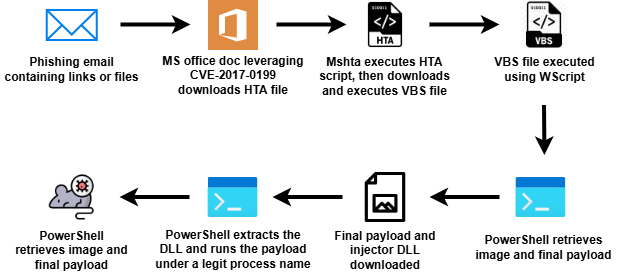
Steganography is being exploited to embed malicious code within innocent-looking image files, often launched through phishing campaigns that leverage vulnerable Microsoft Office documents. Initial infection results in the execution of remote scripts that ultimately deploy trojanized scripts, exemplified by the use of Prnport.vbs. Such methods have led to the delivery of malware like AsyncRAT, highlighting the innovative strategies attackers employ. Affected: Microsoft Office, Windows, Cybersecurity, IT Security
Keypoints :
- Steganography is used to conceal malicious code in image files.
- Initial infections often start with phishing emails leading to malicious Office documents.
- CVE-2017–0199 is exploited to enable remote code execution.
- Trojanized Prnport.vbs is a tool repurposed to deliver malicious payloads.
- Malicious PowerShell scripts are executed to download and execute further malware.
- AsyncRAT is used as a final payload, leveraging techniques like Process Hollowing.
- Indicators of Compromise (IoCs) include specific hashes, URLs, and file names used in the attack.
MITRE Techniques :
- Process Hollowing (T1055.012): Malicious code is injected into a legitimate process (MSBuild) to execute the payload.
- Remote Scripting (T1028): PowerShell commands are utilized to download and run additional scripts and payloads.
Indicator of Compromise :
- [SHA256] Trojanized Prnport.vbs: 1105ae14ccb41fedcf556e4c575e34e505e9a571f2021ba89a75fbe5fa12e3c0
- [URL] AsyncRAT Delivery: hxxps[://]watchonlinehotvideos[.]site/001[.]txt
- [SHA256] AsyncRAT Binary: 448ae5b8890c17a2efe49856531efd62796db52d2ff0ecbb4678334aea2bf776
- [IP] AsyncRAT C2 Address: 148[.]113[.]214[.]176
- [SHA256] Injector Hidden in Image: 0FF5DD1787ACC886A586282858112C6F73B48C31093080D2D8A6E66F018CE8C7