Socket’s Threat Research Team identified an ongoing malicious campaign involving 60 npm packages across three accounts, each embedding a script that collects and exfiltrates detailed network and host information to a Discord webhook. The campaign targets Windows, macOS, and Linux systems, leveraging sandbox evasion to focus on active developer and CI environments, posing a strategic risk for future supply chain attacks. #npm #supplychaincompromise #DiscordWebhook
Keypoints
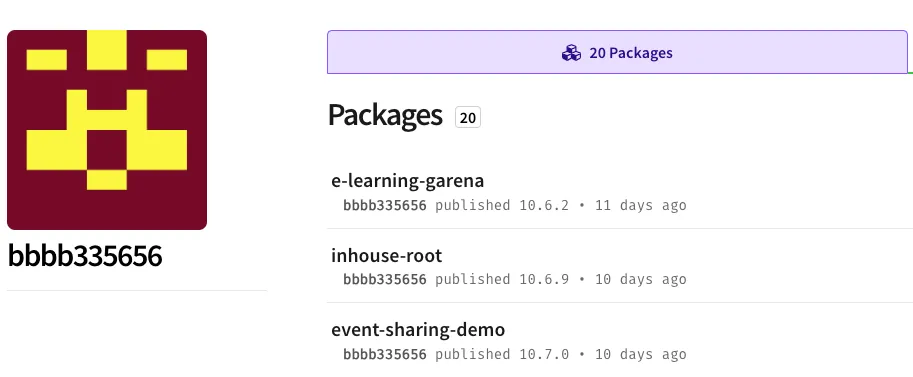
- 60 npm packages under three accounts (bbbb335656, cdsfdfafd1232436437, sdsds656565) contain identical install-time scripts performing host and network reconnaissance.
- The malicious script gathers hostnames, internal and external IPs, DNS server lists, usernames, and directory paths, then exfiltrates data to a Discord webhook.
- Sandbox evasion techniques detect common cloud environments and research VMs to avoid execution on non-target systems.
- Over 3,000 combined downloads have occurred since the campaign began eleven days ago, showing active and ongoing operation.
- Data collected can link private developer networks to external infrastructure, enabling high-value targeting for future intrusions and supply chain attacks.
- All malicious packages remain live on npm, with removal efforts underway but not yet completed.
- Defenders are advised to use dependency-scanning tools to detect post-install hooks, hardcoded URLs, and suspicious package behavior to mitigate risk.
MITRE Techniques
- [T1195.002] Supply Chain Compromise – Compromise of software supply chain via malicious npm packages embedding reconnaissance scripts.
- [T1059.007] Command and Scripting Interpreter: JavaScript – Use of JavaScript scripts executed at install time to collect system data.
- [T1567.004] Exfiltration Over Web Service: Exfiltration Over Webhook – Data exfiltrated to a Discord webhook controlled by the threat actor.
- [T1590] Gather Victim Network Information – Collection of network and host information such as IP addresses, DNS, and hostnames.
- [T1590.002] Gather Victim Network Information: DNS – Retrieval of DNS server configurations.
- [T1590.005] Gather Victim Network Information: IP Addresses – Collection of internal and external IP addresses.
- [T1497] Virtualization/Sandbox Evasion – Checks to bypass execution in cloud or sandbox environments to avoid detection.
Indicators of Compromise
- [Malicious Packages] npm accounts bbbb335656, cdsfdfafd1232436437, and sdsds656565 each published 20 malicious packages such as seatable, datamart, and seamless-sppmy with identical payloads.
- [Registration Emails] Used for the malicious npm accounts: npm9960+1@gmail[.]com, npm9960+2@gmail[.]com, npm9960+3@gmail[.]com.
- [Exfiltration Endpoint] Discord webhook URL hxxps://discord[.]com/api/webhooks/1330015051482005555/5fll497pcjzKBiY3boa9YRh-r5Lr69vRyqccawXuWEhorIlhwOYzp23JWm-iSXuPfQ used for data exfiltration.
Read more: https://socket.dev/blog/60-malicious-npm-packages-leak-network-and-host-data