This article discusses a critical security vulnerability in Google Apps Script that allows OAuth tokens to be silently exfiltrated and exploited within the same script project. Attackers can manipulate user data and send unauthorized emails using these tokens. Despite the potential for significant abuse, Google has deemed the issue not severe enough to warrant a fix. Affected: Google Apps Script, Google Drive, Gmail, individual developers, small teams
Keypoints :
- OAuth tokens can be exfiltrated within Google Apps Script projects, leading to potential abuse.
- Attackers can access and modify Google Drive files using stolen OAuth tokens.
- Exfiltrated tokens can enable unauthorized email sending from compromised Gmail accounts.
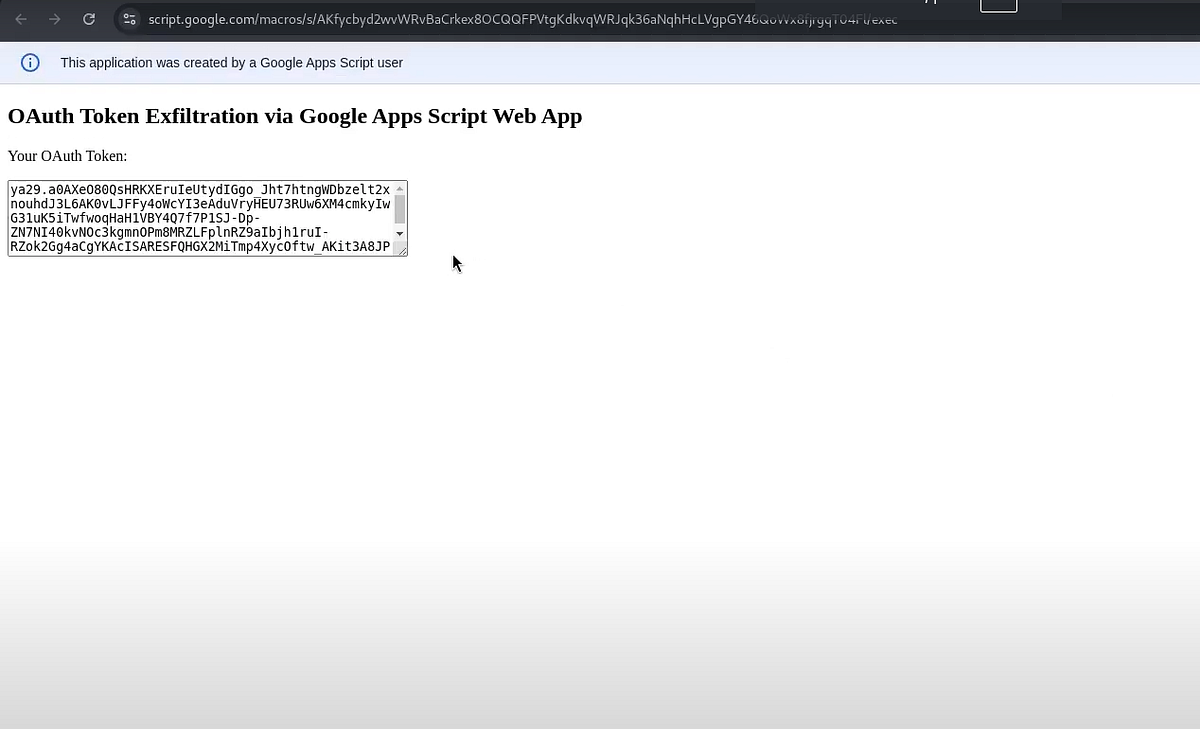
- The attack involves a malicious editor deploying a Web App to capture OAuth tokens.
- Google’s Trust & Safety Team has refused to fix the issue citing a lack of severity.
- The proposed mitigations, such as audit logs and limiting fetch domains, are insufficient for real-time protection.
- The vulnerability highlights a significant gap in security for shared scripts and documents.
- The discussion with Google Security Team revealed a struggle between platform convenience and real-world abuse risks.
- Contact details are provided for further inquiries about the security issue.