Validin has extended its YARA-X integration to run YARA rules continuously on live host response data, enabling timestamped, contextual detections across a dataset of over 850 million daily host responses. New features include a YARA playground, rule versioning, Projects for collaborative investigations, and demonstrated detections of ClickFix-related HTML and JavaScript injections. #ClickFix #IUAM
Keypoints
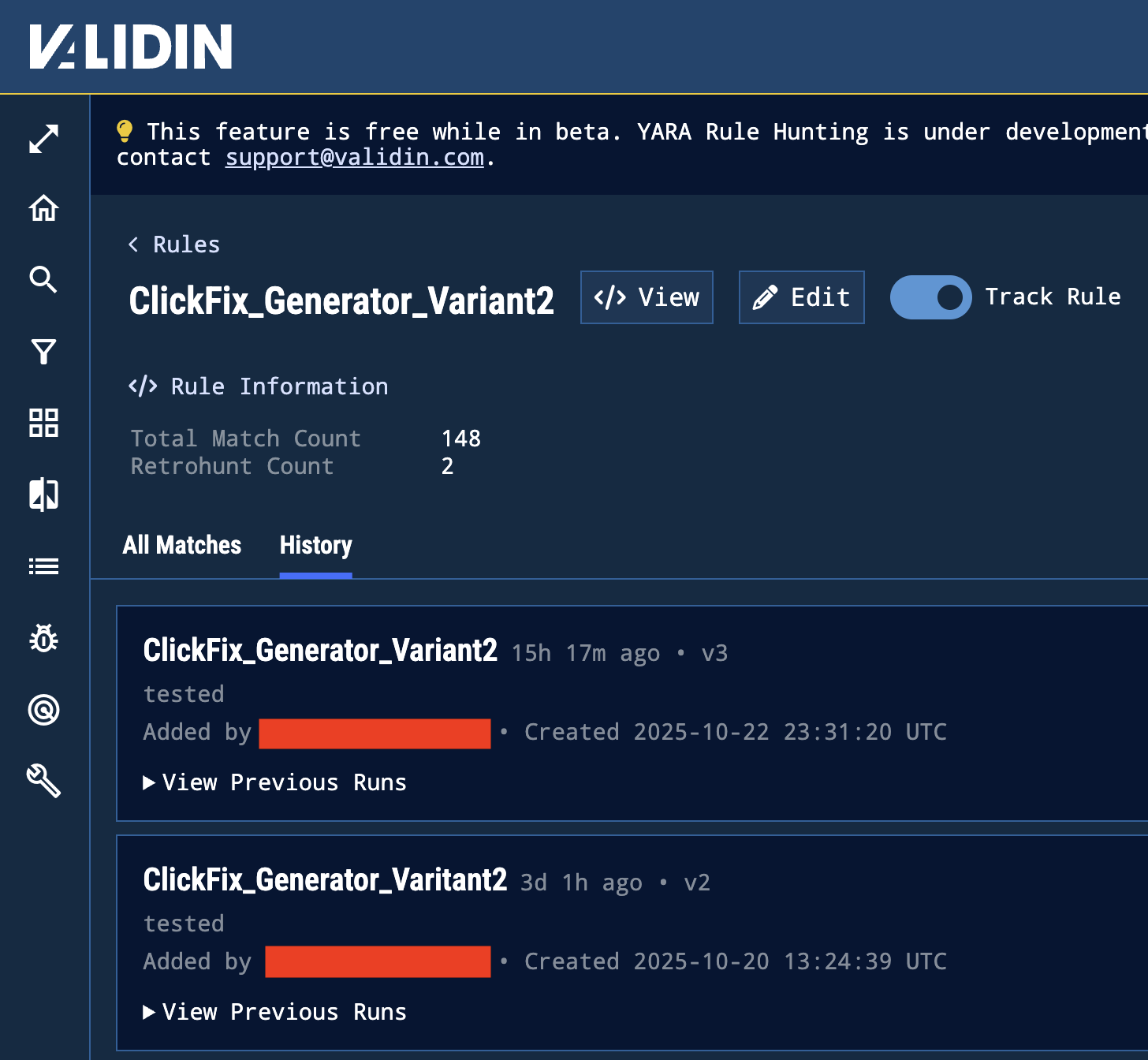
- Validin’s YARA engine now executes continuously on live host response data, converting retrospective hunts into real-time detection.
- Integration with YARA-X enables internet-scale processing of over 850 million host responses daily and maintains deep contextual metadata for matches.
- Rule versioning and a YARA playground let analysts edit, test, and maintain multiple syntax variants with separate run histories for auditability.
- Projects provide a collaborative workspace that unites indicators, alerts, live scans, and YARA rules for streamlined investigations.
- Continuous execution timestamps each match and enriches it with response context, enabling near-realtime infrastructure tracking and triage.
- Case study: ClickFix (IUAM) detections—575 matches for HTML template indicators in 1 day and 2,213 matches for obfuscated JavaScript over 3 days.
- Overall outcomes include faster triage, improved detection efficiency with historical context, minimized propagation risk, and support for trend analysis.
MITRE Techniques
- [T1059] Command and Scripting Interpreter – YARA rules detected JavaScript payloads injected into HTML that capture credentials (“…searching for the CMD+R command that was present in the ClickFix instructions…”).
- [T1204] User Execution – Detection of cloned verification/authentication templates used by ClickFix that rely on user interaction with malicious pages (“…domains hosting cloned verification or authentication templates…”).
- [T1110] Brute Force (credential access related behavior) – Identified pages and scripts designed to capture credentials via injected JavaScript (“…JavaScript payloads that capture credentials…”).
- [T1609] Collection from Web Pages – Extraction and inspection of virtual host responses and HTML to verify malicious content (“…Analysts can review the matching HTML response and response summary directly within a slide-out view.”).
- [T1087] Account Discovery (infrastructure tracking) – Timestamped, continuous matches enable tracking of evolving attacker infrastructure across domains and hosts (“…showing how the ClickFix infrastructure evolves in near real time.”).
Indicators of Compromise
- [Domain ] ClickFix infrastructure detection – examples include multiple domains hosting cloned verification/authentication templates (575 matches over 1 day).
- [File/Script Patterns ] Obfuscated JavaScript payloads – encoded scripts inside benign landing pages (2,213 matches over 3 days).
- [Rule Matches/Timestamps ] Contextual host response matches – timestamped YARA matches with slide-out HTML and certificate details (examples: CMD+R indicator match, obfuscated JS match).
- [Dataset Metrics ] Scale/context indicators – processing context such as “over 850 million host responses daily” and counts like “575 matches” and “2,213 matches”.
Read more: https://www.validin.com/blog/yara_continuous_updates/