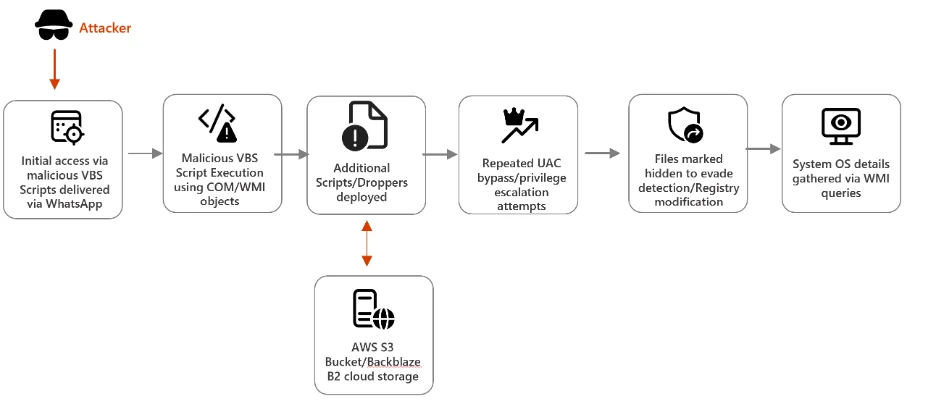
Microsoft Defender Security Research details a campaign in which malicious VBS scripts delivered via WhatsApp download additional VBS payloads and MSI installers from cloud storage, leveraging renamed system utilities and UAC bypass attempts to evade detection and escalate privileges. The report provides Microsoft Defender detections, hunting queries, mitigation recommendations (EDR in block mode, network and web protection, tamper protection, attack surface reduction rules), and IOCs including SHA-256 hashes, cloud storage URLs, and C2 domains. #TrojanVBS_ObfuseKPP #Neescil_top
Keypoints
- Initial access was achieved by delivering malicious VBS scripts to users via WhatsApp, which then executed and fetched additional payloads from cloud storage.
- Attackers used renamed legitimate utilities (e.g., curl, bitsadmin.exe) and VBS execution (wscript.exe) to evade detection and run malicious scripts on endpoints.
- Next-stage payloads (VBS droppers and MSI installers) were hosted on cloud storage services including Amazon S3, Backblaze B2, and Tencent Cloud.
- Privilege escalation attempts included reading Windows UAC settings and trying to run cmd.exe with elevated privileges to modify the registry (UAC bypass).
- Microsoft Defender provides detections for the VBS trojans and suspicious behavior, hunting queries, recommended mitigations (EDR block mode, network/web protection, tamper protection), and threat analytics integration.
- Customers can use Microsoft Sentinel TI Mapping analytics and Microsoft Security Copilot integrations to map IOCs, investigate, and respond to incidents.
- Provided IOCs include multiple SHA-256 hashes for initial scripts, next-stage droppers, and MSI installers, plus cloud storage URLs and command-and-control domains for detection and hunting.
MITRE Techniques
- [T1204 ] User Execution – Attackers delivered VBS scripts via WhatsApp that relied on user execution to gain initial access (‘Users downloaded malicious VBS scripts delivered via WhatsApp.’)
- [T1059.005 ] Command and Scripting Interpreter: Visual Basic – Malicious VBS scripts were executed on endpoints using wscript.exe to run the payloads (‘Malicious VBS scripts were executed on the endpoint.’)
- [T1036 ] Masquerading – Legitimate system utilities were renamed to evade detection and mask malicious activity (‘Legitimate system utilities (e.g., curl, bitsadmin.exe) were renamed to evade detection.’)
- [T1548.002 ] Abuse Elevation Control Mechanism: Bypass UAC – Attempts were made to read Windows UAC settings and run cmd.exe with elevated privileges to execute registry modification commands (‘Attempt to read Windows UAC settings, to run cmd.exe with elevated privileges to execute registry modification commands’)
- [T1105 ] Ingress Tool Transfer – Additional VBS payloads and MSI installers were downloaded from cloud storage services such as Amazon S3, Backblaze, and Tencent Cloud (‘Malicious Script dropped from cloud storage’, ‘Installer dropped from cloud storage’)
- [T1071 ] Application Layer Protocol – Malicious outbound network communication and command-and-control used HTTP(s) to communicate with C2 domains referenced in the report (‘Command and control domain’)
- [T1218 ] Signed Binary Proxy Execution / Living off the Land Binaries and Scripts (LOLBAS) – The report recommends attack surface reduction rules to harden environments against LOLBAS techniques that proxy or misuse legitimate signed binaries to execute malicious actions (‘attack surface reduction rules to harden an environment against LOLBAS techniques used by threat actors’)
Indicators of Compromise
- [SHA-256 ] Initial VBS scripts delivered via WhatsApp – a773bf0d400986f9bcd001c84f2e1a0b614c14d9088f3ba23ddc0c75539dc9e0, 22b82421363026940a565d4ffbb7ce4e7798cdc5f53dda9d3229eb8ef3e0289a
- [SHA-256 ] Next-stage VBS payloads/dropper dropped from cloud storage – 91ec2ede66c7b4e6d4c8a25ffad4670d5fd7ff1a2d266528548950df2a8a927a, 1735fcb8989c99bc8b9741f2a7dbf9ab42b7855e8e9a395c21f11450c35ebb0c, and 9 more hashes
- [SHA-256 ] MSI installers (final payload) dropped from cloud storage – dc3b2db1608239387a36f6e19bba6816a39c93b6aa7329340343a2ab42ccd32d, and 2 more hashes
- [URL ] Cloud storage payload hosting – hxxps[:]//bafauac.s3.ap-southeast-1.amazonaws[.]com, hxxps[:]//f005.backblazeb2.com/file/bsbbmks, and 3 more cloud storage URLs
- [Domain ] Command-and-control infrastructure – Neescil[.]top, velthora[.]top
- [Process filename / command ] Execution artifacts and suspicious process names – wscript.exe (VBS execution), renamed curl/bitsadmin binaries observed in initiation and network activity (e.g., InitiatingProcessVersionInfoOriginalFileName contains “curl.exe”)