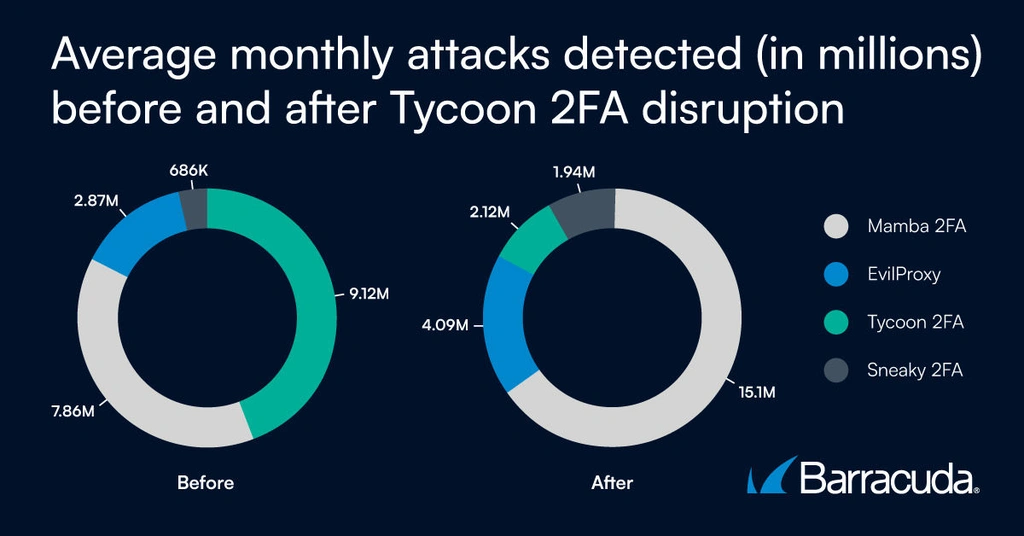
After law enforcement disrupted Tycoon 2FA by seizing 330 domains, threat actors migrated to other phishing-as-a-service platforms and began reusing Tycoon’s tools, Barracuda Networks reports. Although Tycoon lost its market-leading position to Mamba 2FA and EvilProxy, attacks leveraging the major phishing kits rose from roughly 20 million to over 23 million, highlighting ecosystem resilience and increased toolset sharing. #Tycoon2FA #Mamba2FA #EvilProxy #BarracudaNetworks
Keypoints
- Tycoon 2FA, active since at least 2023, enabled phishing campaigns that bypass two-factor authentication and compromise accounts.
- Before the disruption, Tycoon accounted for 62% of phishing attempts seen by Microsoft and held an 89% PhaaS market share according to Barracuda.
- The seizure of 330 Tycoon domains in March did not stop operations, as affiliates cloned code and independently hosted variants.
- Threat actors migrated to Mamba 2FA, EvilProxy, and Sneaky 2FA, and overall attacks from the top phishing kits increased from ~20 million to over 23 million.
- PhaaS toolsets are increasingly reused and modified like open-source projects, making takedowns less effective and requiring broader defensive strategies.
Read More: https://www.securityweek.com/tycoon-2fa-loses-phishing-kit-crown-amid-surge-in-attacks/