Huntress identified a ransomware-precursor intrusion after ingesting SonicWall telemetry that showed successful SonicWall SSLVPN authentication from malicious external IPs, followed by aggressive network reconnaissance and deployment of an EDR-killing payload. The attackers used a wordlist-encoded kernel driver (dropped as C:ProgramDataOEMFirmwareOemHwUpd.sys and leveraging EnPortv.sys) signed with an old revoked certificate to load a driver, terminate security processes, and persist as a Windows kernel service while Huntress correlated SIEM and EDR telemetry to contain the incident. #SonicWallSSLVPN #Huntress #OemHwUpd.sys #EnPortv.sys #BYOVD
Keypoints
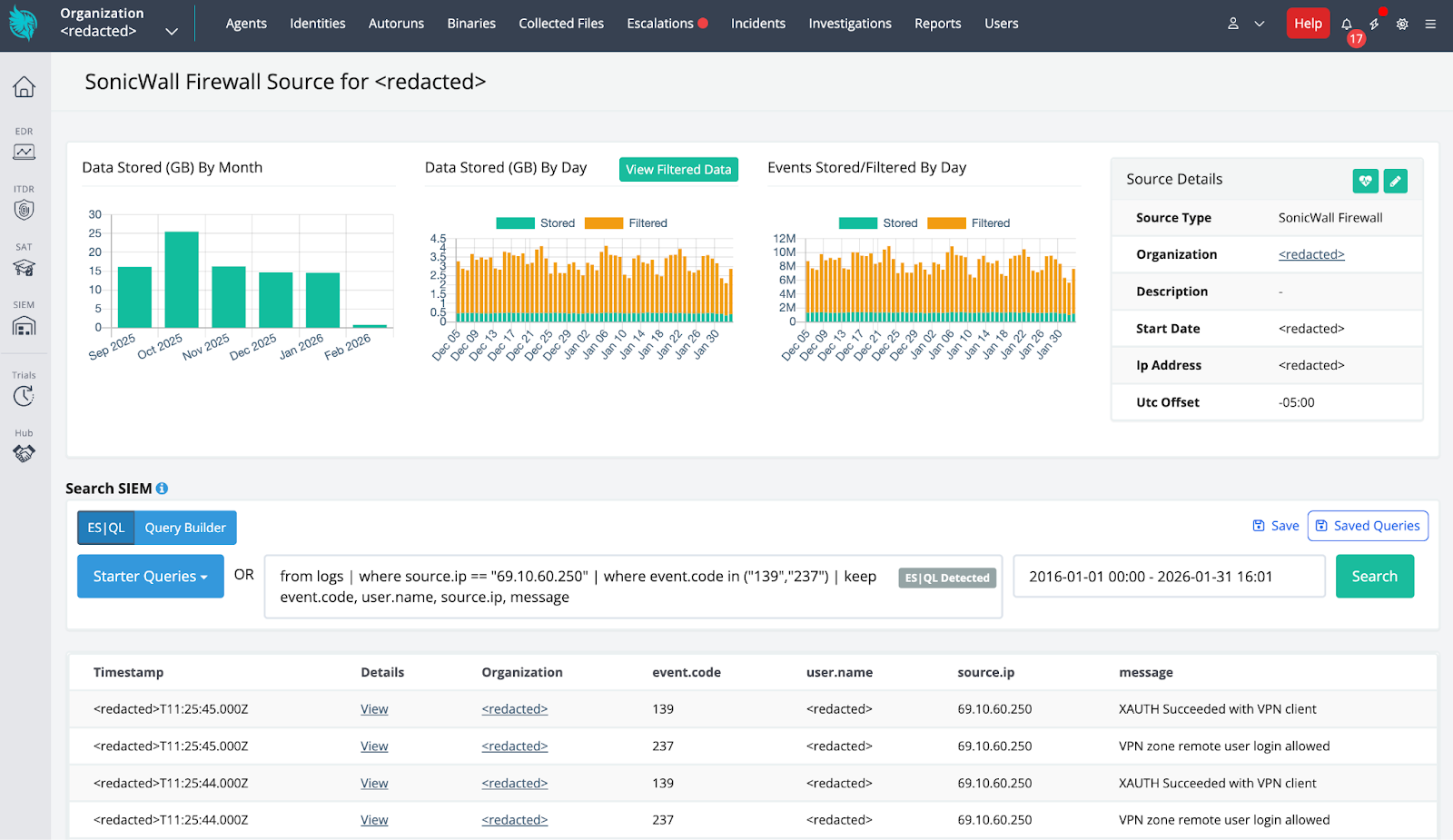
- Initial access occurred via compromised SonicWall SSLVPN credentials; authentication logs show a denied portal attempt from 193.160.216[.]221 followed one minute later by a successful VPN client authentication from 69.10.60[.]250.
- Huntress Managed SIEM ingestion of SonicWall telemetry was critical to detecting the intrusion and building a precise timeline, enabling rapid quarantine and remediation guidance.
- After access, the threat actor performed aggressive network reconnaissance: ICMP ping sweeps, NetBIOS name requests, SMB-targeted probes, and SYN flood behavior exceeding 370 SYNs/second.
- The deployed EDR-killer is a 64-bit Windows binary that decodes an embedded kernel driver via a 256-word dictionary (wordlist-based substitution), writes it to disk as OemHwUpd.sys, timestomps it, and registers it as a kernel service.
- The attacker leveraged a legitimately signed, but long-expired/revoked, EnCase forensic driver (EnPortv.sys) to gain kernel-mode IOCTL capabilities and terminate security processes from kernel space (KillProc via IOCTL 0x223078).
- Persistence was achieved by registering the driver as a kernel service (Service Name: OemHwUpd, Display Name: OEM Hardware HAL Service) so the driver survives reboots.
- Defenses failed due to lack of MFA on remote access, the driver-signing verification gap (no CRL checking for kernel driver signatures), and the wordlist encoding which evaded typical string/entropy detection; notably, the Huntress agent was not targeted by the kill list.
MITRE Techniques
- [T1078 ] Valid Accounts – Compromised VPN credentials used to authenticate to SonicWall SSLVPN and gain access. (‘successfully authenticated to the SonicWall SSLVPN from a malicious external IP address in February 2026.’)
- [T1046 ] Network Service Discovery – Threat actor performed network reconnaissance via ICMP ping sweeps, NetBIOS probes and SMB-targeted activity. (‘SonicWall IPS alerts captured ICMP ping sweeps, NetBIOS name request probes, and SMB-targeted activity, including SYN flood behavior at rates exceeding 370 SYNs/second.’)
- [T1027 ] Obfuscated Files or Information – Malware conceals a kernel driver using a wordlist-based substitution cipher that encodes bytes as English words to evade static/entropy detection. (‘wordlist-based substitution cipher that transforms each byte of the driver into an English word.’)
- [T1036 ] Masquerading – The EDR-killer binary and driver masquerade as legitimate OEM/firmware update components to blend with system software. (‘masquerades as a legitimate firmware update utility.’)
- [T1543 ] Create or Modify System Process (Windows Service) – The binary registers the decoded kernel driver as a Windows kernel service for persistence (OemHwUpd/OEM Hardware HAL Service). (‘registering it as a Windows kernel service’ and service details: Service Name: OemHwUpd; Display Name: OEM Hardware HAL Service.)
- [T1070.006 ] Timestomping – The malware copies timestamps from ntdll.dll to the dropped driver to hide file creation/modification times. (‘copying timestamps from the legitimate ntdll.dll to make the malicious driver blend in with system files.’)
- [T1562.001 ] Impair Defenses: Disable/Modify Tools – The usermode component sends PIDs to the kernel driver which calls ZwTerminateProcess to kill EDR/security processes from kernel mode. (‘the function performs… sends target PIDs via DeviceIoControl… the driver… calls ZwTerminateProcess.’)
Indicators of Compromise
- [File Path ] Dropped malicious kernel driver – C:ProgramDataOEMFirmwareOemHwUpd.sys
- [Service Name ] Persistence and service registration – OemHwUpd (Service Display Name: OEM Hardware HAL Service)
- [File Name ] Executable names used by attackers – svchost.exe (malicious EDR killer masquerade), EnPortv.sys / OemHwUpd.sys (kernel driver)
- [IPv4 Address ] Malicious VPN/authentication endpoints – 69.10.60[.]250, 193.160.216[.]221
- [File Hash ] Malicious binary hashes – 3111f4d7d4fac55103453c4c8adb742def007b96b7c8ed265347df97137fbee0 (EnCase driver / OemHwUpd.sys), 6a6aaeed4a6bbe82a08d197f5d40c2592a461175f181e0440e0ff45d5fb60939 (EDR killer binary svchost.exe)
Read more: https://www.huntress.com/blog/encase-byovd-edr-killer