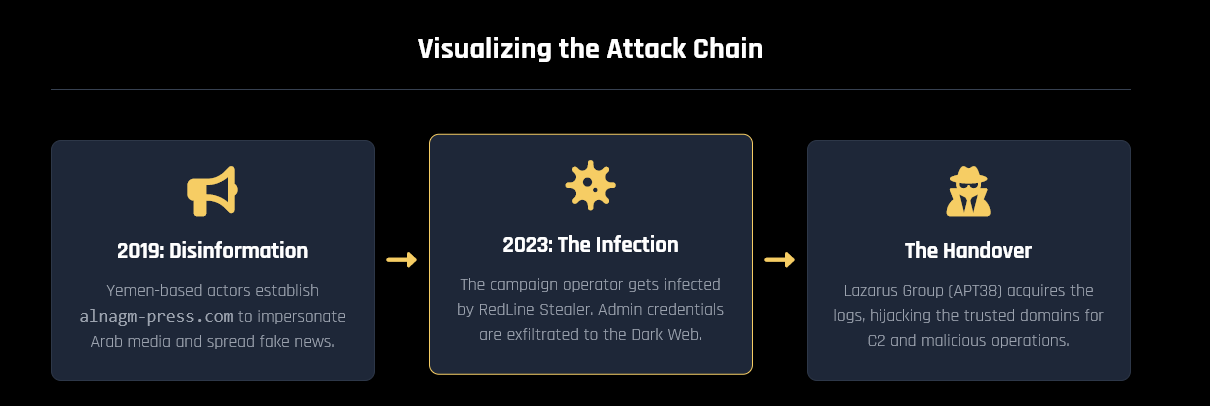
This article reveals how a Yemen-based disinformation campaign was linked to North Korea’s Lazarus Group through a single infected computer in 2020. The compromise enabled the threat actors to hijack trusted news domains for cyber-espionage and malicious campaigns. #LazarusGroup #RedLineStealer
Keypoints
- A Yemen disinformation network created fake news outlets to spread pro-Houthi narratives in 2019.
- The same computer in Yemen was infected with RedLine Stealer, exfiltrating administrative credentials.
- Lazarus Group hijacked these credentials to control trusted news domains for malicious activities.
- Existing, aged domains like alnagm-press.com were exploited by Lazarus for covert operations.
- The case exemplifies how Infostealers can enable nation-state APT operations through opportunistic infrastructure hijacking.