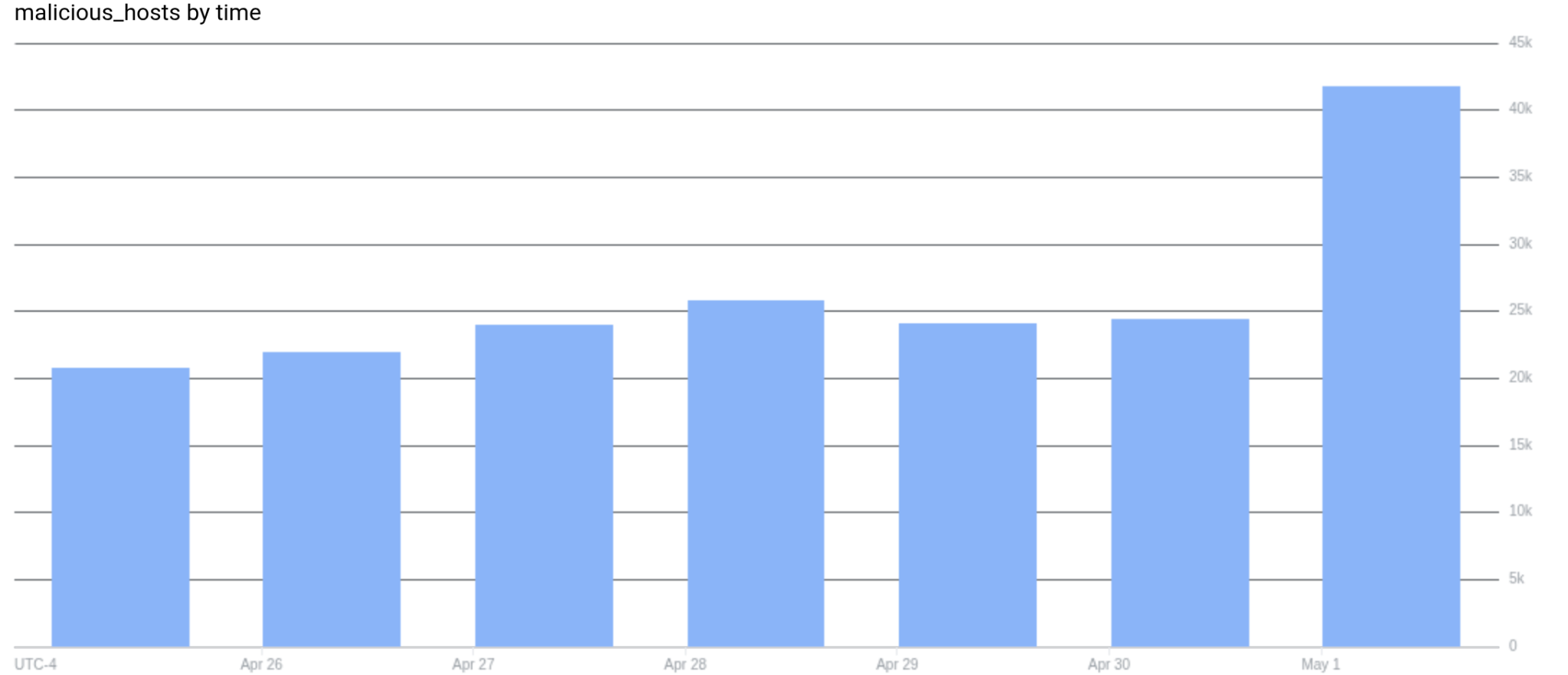
A critical pre-authentication bypass, CVE-2026-41940, was disclosed in cPanel/WHM and coincided with a sharp spike in hosts classified as malicious. Analysis indicates two active campaigns—post-compromise Mirai deployments and a large-scale file-encrypting campaign appending “.sorry” to files—heavily targeting cPanel systems. #CVE-2026-41940 #cPanel
Keypoints
- CVE-2026-41940 is a critical pre-authentication bypass affecting cPanel/WHM login flows.
- On May 1, roughly 80% of newly malicious hosts were running cPanel/WHM, driving the spike.
- At least two attack paths are present: Mirai variant deployments and ransomware that appends “.sorry”.
- Thousands of cPanel hosts publicly expose directories with files renamed using the “.sorry” extension.
- Malicious activity is concentrated in VPS and cloud provider ASNs such as DigitalOcean, Contabo, and OVH.