TeamPCP published trojanized Telnyx Python SDK releases (4.87.1 and 4.87.2) to PyPI that execute on import and employ split-file injection, runtime Base64 decoding, and WAV-based steganography to fetch credential‑stealing payloads. The campaign adds Windows persistence (dropped msbuild.exe in user Startup folders) and defenders should downgrade to Telnyx 4.87.0 and treat any system that imported the affected versions as compromised. #TeamPCP #Telnyx
Keypoints
- Two malicious Telnyx SDK releases (4.87.1 and 4.87.2) were published to PyPI and activate immediately when the package is imported (code injected into telnyx/_client.py).
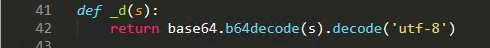
- Malicious code is split across three distant locations in _client.py (a Base64 decode wrapper _d(), a large Base64 string for Linux/macOS, and a Windows path appended at file end) to evade visual inspection.
- The harvester is not embedded in source; instead the package downloads WAV audio files from a C2 server and extracts XOR‑encrypted payloads hidden in audio frames (Base64 decode -> first 8 bytes XOR key -> rotating XOR decrypt).
- Windows-specific behavior downloads hangup.wav from 83.142.209.203:8080, extracts a PE, installs it as msbuild.exe in the user Startup folder for persistence, and uses a hidden msbuild.exe.lock anti-replay mechanism.
- Linux/macOS path launches the Base64 payload as a detached background process that downloads ringtone.wav, extracts the harvester, and exfiltrates results via the actor’s tpcp.tar.gz pipeline (AES-256-CBC + RSA-4096 OAEP → HTTP POST with X-Filename: tpcp.tar.gz).
- Defensive recommendations: treat systems that imported 4.87.1/4.87.2 as compromised, downgrade to Telnyx 4.87.0, pin PyPI dependencies by hash, and hunt for WAV downloads from non-media IPs, unexpected msbuild.exe in Startup, X-Filename: tpcp.tar.gz POSTs, and hidden .lock file activity.
MITRE Techniques
Indicators of Compromise
- [IP Address ] C2 server and payload hosting – 83.142.209.203:8080 (WAV files/hangup.wav and ringtone.wav)
- [PyPI package versions ] trojanized releases – Telnyx 4.87.1, Telnyx 4.87.2
- [File path / filename ] injected module and startup binary – telnyx/_client.py (injected code), msbuild.exe (dropped to Startup) and msbuild.exe.lock (hidden lock file)
- [File names ] stego payload and exfil archive – hangup.wav, ringtone.wav, and tpcp.tar.gz (exfiltrated archive indicated by X-Filename: tpcp.tar.gz header)
- [Domains / URLs ] related infrastructure examples (legacy/related campaign) – models.litellm.cloud (LiteLLM exfil), checkmarx.zone/raw (observed in prior activity)
Read more: https://www.trendmicro.com/en_us/research/26/c/teampcp-telnyx-attack-marks-a-shift-in-tactics.html