Intellexa’s Predator spyware can suppress iOS recording indicators to secretly stream camera and microphone feeds from infected devices. Jamf’s analysis shows Predator hooks SpringBoard’s sensor update path (HiddenDot::setupHook) to nullify SBSensorActivityDataProvider and prevent the green/orange dots from appearing, while using ARM64 pattern matching and PAC redirection to enable camera access. #Predator #Intellexa
Tag: PRIVACY

Multiple critical vulnerabilities (CVE-2026-25715, CVE-2026-24455, CVE-2026-26049, CVE-2026-26048) in the Jinan USR IOT PUSR USR-W610 (…

A missing-authentication vulnerability (CVE-2026-24790) in Welker OdorEyes EcoSystem Pulse Bypass System with XL4 Controller could allow unauthorized actions that result in over- or under-odorization events. CISA rates this issue CVSS v3 8.2 and recommends isolating control networks, minimizing internet exposure, using updated VPNs and firewalls, and following ICS defense-in-depth guidance to…
ESET researchers analyzed PromptSpy, an Android malware that uses a VNC module and Accessibility Services to capture screens, steal unlock credentials, and enable remote control of compromised devices. The malware uniquely leverages Google’s Gemini generative AI at runtime—sending UI element XML to Gemini and following its JSON instructions for taps and…
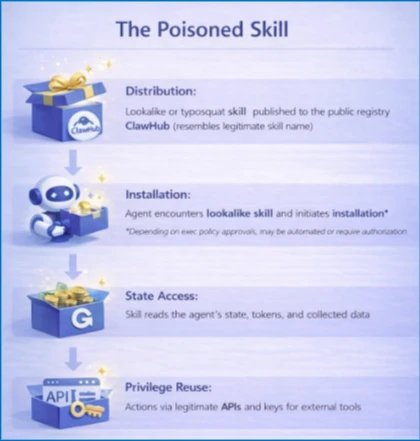
Self-hosted agent runtimes like OpenClaw significantly widen the execution boundary by ingesting untrusted text, downloading and executing external skills, and acting with the credentials of the host, creating risks of credential exposure, persistent memory manipulation, and host compromise. Organizations should treat OpenClaw as untrusted code execution and, if evaluated, run it only in isolated environments with dedicated non-privileged credentials, continuous monitoring, and a rebuild plan. #OpenClaw #Moltbook
![Cybersecurity News | Daily Recap [18 Feb 2026] Cybersecurity News | Daily Recap [18 Feb 2026]](https://www.hendryadrian.com/tweet/image/DailyRecap.png)
Daily Recap, the latest cyber threats cover exploited zero-days like Dell RecoverPoint CVE-2026-22769 used by UNC6201 to deploy GRIMBOLT/SLAYSTYLE with Ghost NICs, and a spectrum of high-impact flaws, supply-chain breaches, and targeted espionage campaigns. The recap also notes active exploitation of TeamT5 CVE-2024-7694, Ivanti EPMM backdoors bypassing patches, Keenadu firmware backdoors, CrescentHarvest espionage, and AI/Cloud risks including Copilot as C2 and Grok deepfakes, plus notable data leaks and enforcement actions. #UNC6201 #GRIMBOLT #SLAYSTYLE #DellRecoverPoint #TeamT5 #IvantiEPMM #Keenadu #CRESCENTHARVEST #Copilot #Grok #Eurail #Cellebrite #DavaIndia #Notepad++ #Chrysalis #PaloAltoNetworks #Koi #VulnCheck

Texas Attorney General Ken Paxton sued TP-Link, alleging the company deceptively marketed secure networking devices while allowing Chinese state-sponsored actors to exploit firmware vulnerabilities. The complaint cites Check Point Research linking Camaro Dragon campaigns to TP-Link flaws and frames the case as part of a broader move to treat security claims…

Ireland’s Data Protection Commission has opened a formal GDPR investigation into X over its Grok AI allegedly generating non-consensual sexual images of real people, including children. The inquiry joins parallel probes by the ICO, the European Commission, California’s attorney general, Ofcom, and French prosecutors and could result in significant EU‑wide fines and criminal measures. #Grok #X

DavaIndia’s Next.js-based platform had an exposed admin subdomain that allowed unauthenticated access to super-admin APIs, which a security researcher exploited to create a super-admin account. The vulnerability exposed customer orders, personal data, inventory and drug-control functions, was reported on August 20, 2025, fixed within a month, and confirmed closed with CERT-In…

Ireland’s Data Protection Commission has opened a large-scale GDPR investigation into Elon Musk’s X Internet Unlimited Company over its Grok AI generating nonconsensual sexually explicit deepfake images, including images reportedly involving children. The probe — running alongside separate EU and UK inquiries under the Digital Services Act — could result in…

A January breach of Eurail’s customer database has escalated into a large-scale identity theft crisis after attackers began offering millions of travelers’ sensitive records for sale on criminal marketplaces and publishing a sample on Telegram. The compromised information—names, passport numbers, ID numbers, IBANs, health data and contact details—puts DiscoverEU participants at…

Google released the first Android 17 beta with a range of privacy, security, and developer-focused improvements across performance, media, camera, and connectivity. Major security changes include deprecation of the usesCleartextTraffic attribute (blocking cleartext by default without a network security config), a public SPI for HPKE hybrid cryptography, certificate transparency enabled by…

Eurail B.V. confirmed that customer data stolen in a breach earlier this year is being offered for sale on the dark web and a sample of the data was published on Telegram. The company is investigating which records and how many customers were affected, has notified data protection authorities under the GDPR, and advises customers to change Rail Planner passwords, reset reused credentials, and monitor bank accounts. #Eurail #Telegram #GDPR #RailPlanner #DiscoverEU
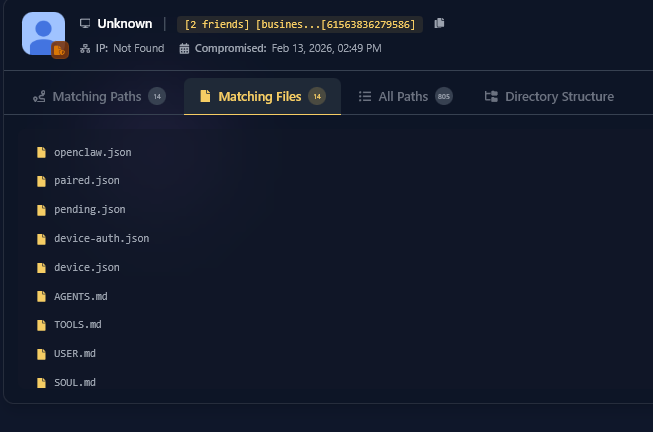
Hudson Rock detected a live ClawdBot infection that exfiltrated an OpenClaw user’s workspace and configuration, demonstrating a shift from stealing browser credentials to harvesting AI agent identities. The attacker obtained openclaw.json, device.json (including a private key), and soul.md/memory files, enabling impersonation, unauthorized access, and a comprehensive view of the victim’s personal context. #ClawdBot #OpenClaw #HudsonRock
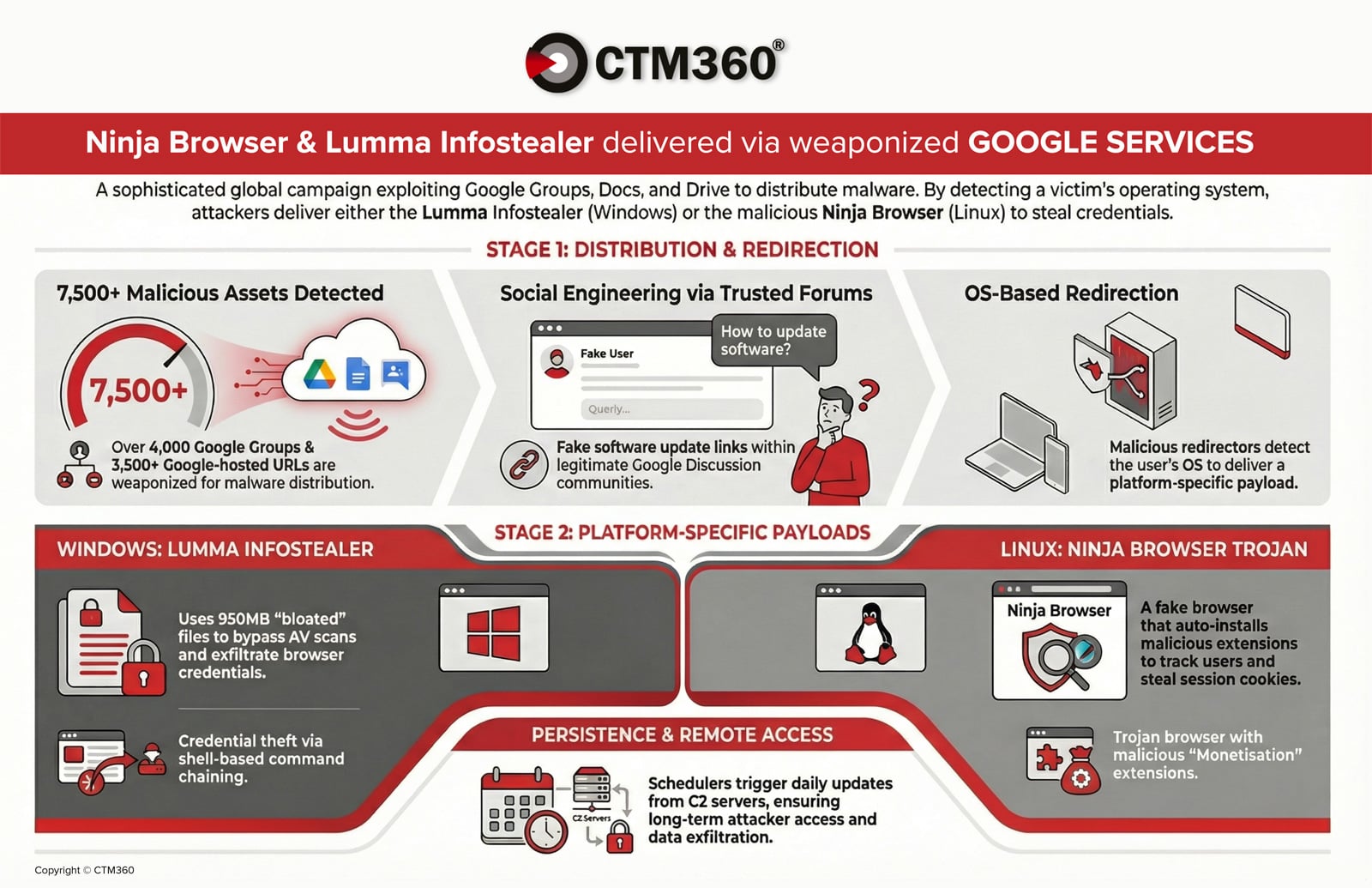
CTM360 reports an active global campaign abusing over 4,000 malicious Google Groups and 3,500 Google-hosted URLs to distribute credential‑stealing malware and establish persistent access on compromised devices. Windows users are targeted with an oversized, password‑protected archive delivering the Lumma infostealer, while Linux users are redirected to a trojanized Chromium “Ninja Browser” that silently installs malicious extensions and persistence mechanisms. #LummaStealer #NinjaBrowser
