Intellexa’s Predator spyware can suppress iOS recording indicators to secretly stream camera and microphone feeds from infected devices. Jamf’s analysis shows Predator hooks SpringBoard’s sensor update path (HiddenDot::setupHook) to nullify SBSensorActivityDataProvider and prevent the green/orange dots from appearing, while using ARM64 pattern matching and PAC redirection to enable camera access. #Predator #Intellexa
Tag: APPLE
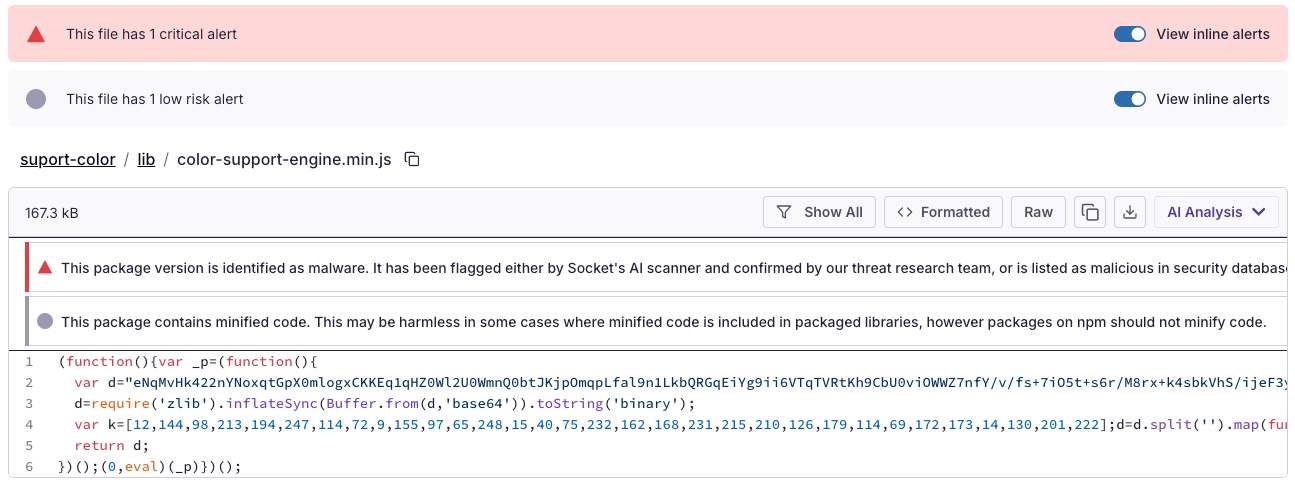
Socket’s Threat Research Team discovered a Shai-Hulud-like supply chain worm campaign tracked as SANDWORM_MODE that spread through at least 19 typosquatting npm packages and a malicious GitHub Action, harvesting developer and CI secrets, exfiltrating via HTTPS/GitHub API/DNS, and persisting via git hooks and MCP server injection targeting AI coding assistants. npm, GitHub, and Cloudflare removed related infrastructure, but defenders must treat the identified packages and injected workflows as active compromise risks and rotate/revoke affected tokens, audit global git templates, and inspect AI assistant configs for rogue MCP servers. #SANDWORM_MODE #suport-color

AhnLab’s January 2026 report summarizes automated collection and analysis of Infostealer samples distributed via SEO-poisoned crack/keygen pages, forum and corporate site posts, and highlights differences in Windows and macOS distribution and obfuscation techniques. Notable findings include ACRStealer’s shift to ECDH + ChaCha20-Poly1305 for C2 encryption and rapid macOS sample churn with…

Security researchers uncovered a mass-distributed macOS loader delivered via cracked music plugin DMGs that deploys multistage payloads including Odyssey and MacSyncStealer and an additional Mach-O loader. The campaign leverages social engineering (including ClickFix-style browser prompts), obfuscated shell scripts, and PPI/affiliate tracking to retrieve and execute secondary payloads from domains such as mac[.]fleebottom-33[.]xyz and robincompany[.]xyz. #MacSyncStealer #Odyssey

Kaspersky discovered a sophisticated Android backdoor named Keenadu embedded in device firmware that can silently harvest data and remotely control infected tablets. The backdoor is injected via libandroid_runtime.so into the Zygote process, uses a client-server AKServer/AKClient architecture to load malicious modules, and has been observed in Alldocube firmware and other undisclosed…

Ireland’s Data Protection Commission has opened a large-scale GDPR investigation into Elon Musk’s X Internet Unlimited Company over its Grok AI generating nonconsensual sexually explicit deepfake images, including images reportedly involving children. The probe — running alongside separate EU and UK inquiries under the Digital Services Act — could result in…

Microsoft disclosed a new ClickFix variant that tricks users into running nslookup via the Windows Run dialog and cmd.exe to perform DNS-based staging and fetch a second-stage payload. The chain downloads a ZIP from azwsappdev[.]com that leads to a Python script, VBScript and ModeloRAT persistence, while related campaigns use CastleLoader, Lumma…

North Korean threat actor UNC1069 used AI-generated deepfakes and sophisticated custom malware to target a FinTech company in the cryptocurrency sector. Mandiant’s investigation revealed a Telegram account hijack, a spoofed Calendly/Zoom call that lured the victim into a ClickFix routine, and deployment of seven malware families including SILENCELIFT, DEEPBREATH, and CHROMEPUSH….

Apple released security updates to patch a zero-day arbitrary code execution vulnerability in dyld tracked as CVE-2026-20700 that was exploited in an “extremely sophisticated” targeted attack against specific individuals. The flaw, discovered by Google’s Threat Analysis Group, affects iPhone, iPad, Mac, tvOS, watchOS, and visionOS devices and was fixed in iOS…

CISA added four vulnerabilities to its Known Exploited Vulnerabilities Catalog—CVE-2024-43468, CVE-2025-15556, CVE-2025-40536, and CVE-2026-20700—based on evidence of active exploitation. FCEB agencies must remediate KEV-listed CVEs under BOD 22-01, and CISA urges all organizations to prioritize timely remediation to reduce exposure. #MicrosoftConfigurationManager #SolarWindsWebHelpDesk…

Datadog observed an active campaign using fake GitHub repositories and ClickFix landing pages to social-engineer victims into pasting commands that install macOS infostealers and (in some builds) Windows components. The actor iterates on MacSync and a persistent SHub Stealer v2.0—adding credential validation, broad file and wallet collection, dynamic anti-analysis, and a LaunchAgent-based beacon for remote command execution. #SHub #MacSync
Threat actors are abusing public Claude artifacts and malicious Google Ads in ClickFix campaigns to trick macOS users into pasting shell commands that install the MacSync infostealer. Researchers from Moonlock Lab and AdGuard observed multiple variants and thousands of views, with the same C2 infrastructure linking the activity to a single actor. #MacSync #Claude
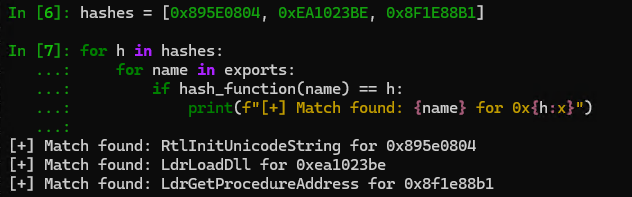
OysterLoader (aka Broomstick / CleanUp) is a multi-stage C++ loader distributed via fake signed MSI installers that delivers payloads (notably Rhysida ransomware and commodity stealer Vidar) using staged shellcode, custom LZMA, and steganographically hidden DLLs. Its operators use extensive obfuscation (API-hammering, dynamic API hashing, custom Base64 alphabets and RC4), robust HTTP-based C2 with fallback servers, scheduled-task persistence, and anti-analysis checks. #OysterLoader #Rhysida
![Threat Research | Weekly Recap [08 Feb 2026] Threat Research | Weekly Recap [08 Feb 2026]](https://www.hendryadrian.com/tweet/image/WeeklyRecap.png)
Cybersecurity Threat Research ‘Weekly’ Recap: the report surveys supply-chain compromises, ransomware/defense evasion, infostealers, targeted espionage, cloud and identity threats, phishing, vulnerabilities and detection, labs automation and resilience guidance. It highlights notable campaigns and families such as the Notepad++ supply-chain attack, GlassWorm on Open VSX, dYdX npm/PyPI abuse, DYNOWIPER in Polish energy, Black Basta kernel-driver evasion, SonicWall SSLVPN intrusion, APT28 and Shadow Campaigns, Amaranth-Dragon, Transparent Tribe, Stan Ghouls, Prometei, ShinyHunters, NGOSS and ZHGUI breaches, plus attempts at web-infra abuse (Quest KACE, NGINX hijacking, CrashFix/ClickFix) and AI-assisted cloud intrusion via Amazon Bedrock. #NotepadPlusPlus #GlassWorm #OpenVSX #dYdX #DYNOWIPER #BlackBasta #SonicWall #APT28 #ShadowCampaigns #AmaranthDragon #TransparentTribe #StanGhouls #Prometei #ShinyHunters #NGOSS #ZHGUI #QuestKACE #CrashFix #ClickFix #GOAD #NGINX #Baota #AmazonBedrock #DetectionsAsCode

A routine business call turned into a macOS compromise after North Korean state-sponsored hackers lured a cryptocurrency-sector professional from messaging apps into a Microsoft Teams meeting and tricked them into running terminal commands under the pretense of fixing audio. Daylight Security links the campaign to BlueNoroff’s GhostCall operation, which installs a…
