Stan Ghouls (aka Bloody Wolf) ran a targeted campaign primarily against organizations in Uzbekistan (and collateral victims in Russia, Kazakhstan, Turkey, Serbia, and Belarus) using spear-phishing PDFs that link to a Java-based loader which installs NetSupport remote management components. Investigators found roughly 50 victims in Uzbekistan, multiple new domains and a JAR/loader MD5 tied to the campaign, and discovered Mirai IoT binaries on a domain related to the threat infrastructure. #StanGhouls #NetSupport
Keypoints
- Stan Ghouls (aka Bloody Wolf) has targeted manufacturing, finance, and IT organizations in Uzbekistan and neighboring countries since at least 2023, with ~50 victims identified in the latest campaign.
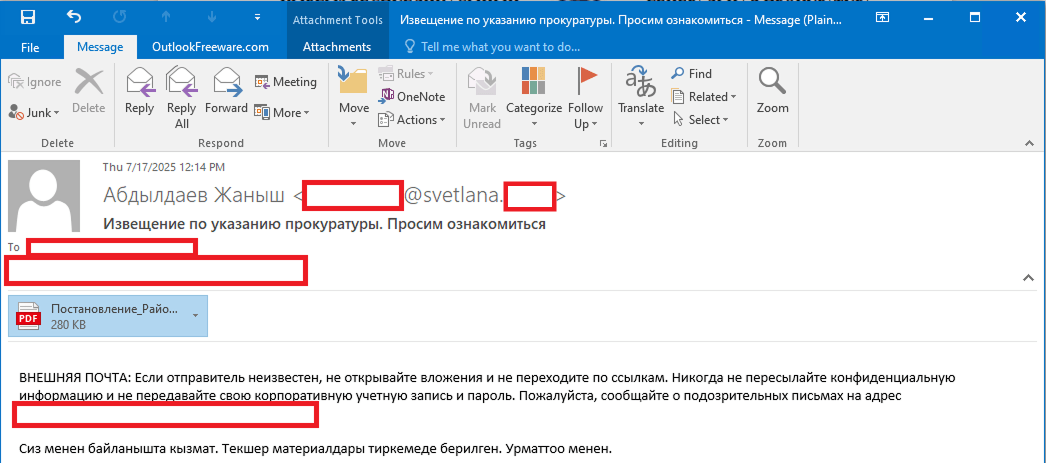
- Initial access is achieved via spear-phishing emails containing malicious PDF decoys written in local languages (Uzbek, Kyrgyz), which instruct victims to run a Java-based loader.
- The Java loader displays fake errors, enforces an installation-attempt limit, iterates through attacker-controlled domains, downloads a NetSupport RAT package, and creates a run.bat to execute it.
- NetSupport components are explicitly fetched (e.g., client32.exe, many DLLs) and persistence is achieved via a Startup folder autorun script, a registry Run key, and a scheduled task.
- Telemetry tied a domain (hgame33[.]com) to Mirai IoT binaries (multiple architecture variants), suggesting either Stan Ghouls expanded into IoT malware or shared infrastructure with other actors.
- Attribution to Stan Ghouls is supported by Java loader code overlap, identical decoy documents across campaigns, and a distinctive preference for Java-based loaders and localized decoys; defenders should monitor infrastructure churn (new domains) and the listed IOCs.
MITRE Techniques
- [T1566.001 ] Spearphishing Attachment – Phishing emails contain malicious PDF attachments used as the initial entry vector; quote: ‘You will receive a court notice. Application for retrial. The case is under review by the district court.’
- [T1204.002 ] User Execution: Malicious File – The decoy PDF tricks victims into running or downloading a Java-based loader by claiming the materials require the Java Runtime Environment; quote: ‘the “case materials” (which are actually the malicious loader) can only be opened using the Java Runtime Environment.’
- [T1105 ] Ingress Tool Transfer – The loader downloads NetSupport components from attacker-controlled domains and saves them to the victim machine; quote: ‘The loader fetches the following files, which make up the components of the NetSupport RAT: PCICHEK.DLL, client32.exe, advpack.dll, …’
- [T1547.001 ] Boot or Logon Autostart Execution: Registry Run Keys and Startup Folder – The loader ensures persistence by creating a Startup folder autorun script and adding the launch script to HKCU Run; quote: ‘It creates an autorun script named SoliqUZ_Run.bat and drops it into the Startup folder’
- [T1053.005 ] Scheduled Task/Job – The loader creates a scheduled task to launch the NetSupport run.bat on logon; quote: ‘schtasks Create /TN “[malicious_task_name]” /TR “[path_to_run.bat]” /SC ONLOGON /RL LIMITED /F /RU “[%USERNAME%]”‘
- [T1219 ] Remote Access Software – The attackers misuse legitimate NetSupport remote management software to maintain control over infected machines; quote: ‘they switched strategies, opting to misuse legitimate software, NetSupport, to maintain control over infected machines.’
- [T1071.001 ] Application Layer Protocol: Web Protocols – NetSupport configuration and C2 use web/HTTPS endpoints (gateway on port 443); quote: ‘GatewayAddress=hgame33[.]com:443’
Indicators of Compromise
- [File hash ] decoy and loader examples – 7556e2f5a8f7d7531f28508f718cb83d (E-SUD_705306256_ljro_varaqasi.pdf decoy, MD5), 95db93454ec1d581311c832122d21b20 (malicious JAR loader, MD5), and other loader/decoy hashes.
- [Domain ] malicious distribution and C2 hosting – mysoliq-uz[.]com (hosts malicious JAR download link), hgame33[.]com (hosting NetSupport files and Mirai binaries), my-xb[.]com, and 20+ additional domains observed tied to Stan Ghouls infrastructure.
- [File name ] NetSupport components and persistence artifacts – client32.exe, run.bat, SoliqUZ_Run.bat (Startup script), PCICHEK.DLL, and other NetSupport files; and Mirai binaries such as morte.x86, morte.arm (multiple architecture variants) observed on hgame33[.]com.
- [URL ] weaponization and payload download links – hxxps://mysoliq-uz[.]com/api/v2/documents/…/statistical-statements/ (links to malicious JAR), hxxps://my-xb[.]com/api/v2/… (same JAR), and hxxp://www.hgame33[.]com/00101010101001/morte.x86 (Mirai binary).
Read more: https://securelist.com/stan-ghouls-in-uzbekistan/118738/