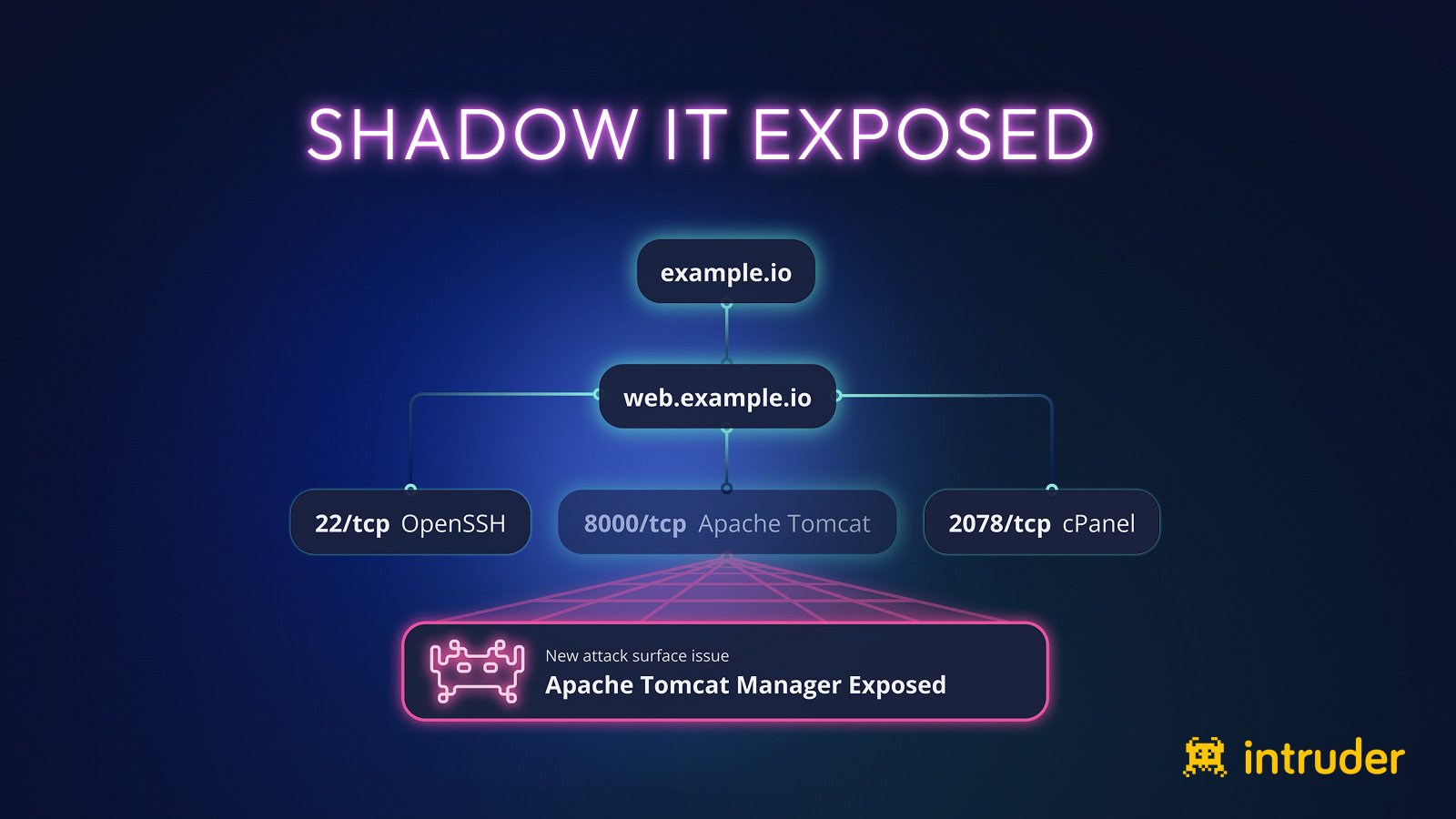
Shadow IT poses significant security risks by exposing sensitive data through unmanaged assets like backups, open Git repositories, and unsecured admin panels. Intruder’s automated tools help detect and fix these vulnerabilities rapidly, preventing potential breaches. #ShadowIT #SubdomainEnumeration
Keypoints
- Shadow IT includes systems that security teams are unaware of, posing security risks.
- Subdomain enumeration using Certificate Transparency logs helps uncover exposed assets quickly.
- Common exposures include unsecured backups, public Git repositories, and unprotected admin panels.
- Many vulnerabilities are simple for scanners to detect but often remain hidden from management programs.
- Continuous discovery and scanning of assets are essential to managing attack surface risks effectively.