Threat actors extensively abused tax-themed lures in early 2026, using phishing and impersonation to deliver remote monitoring and management (RMM) tools, information stealers, and credential-harvesting pages across global targets. Newly tracked actors like TA4922 and TA2730 leveraged realistic social engineering (including real phone numbers and organization impersonation) and diverse delivery methods to gain remote access and harvest credentials. #TA4922 #TA2730
Keypoints
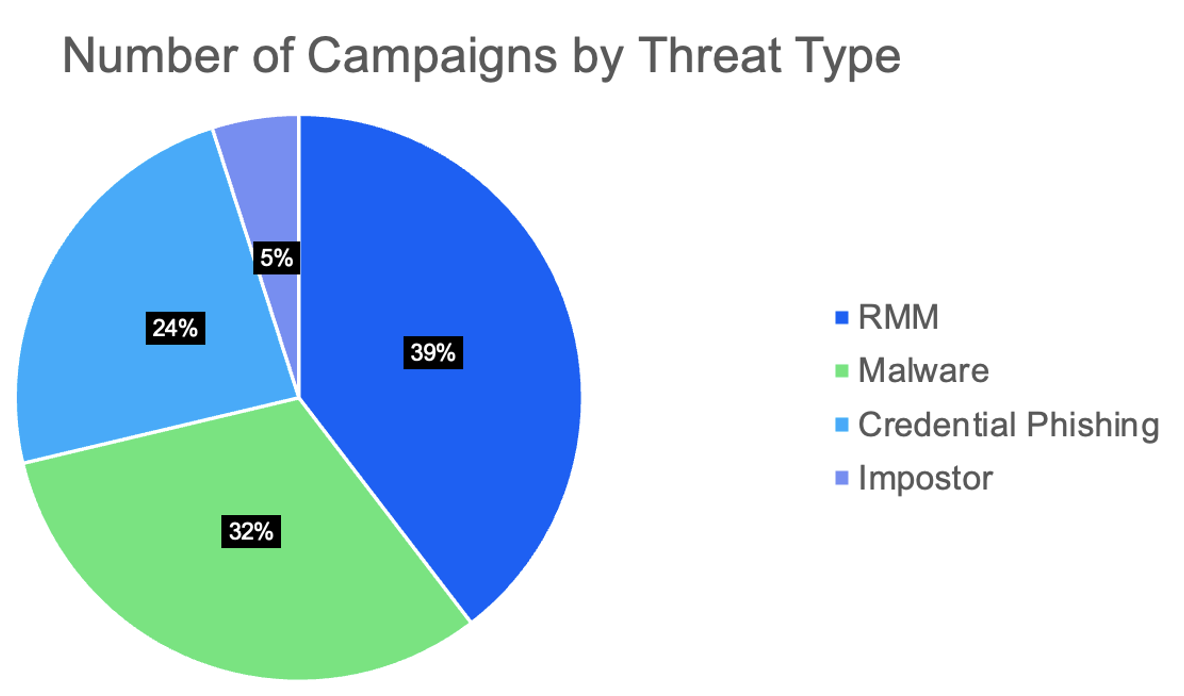
- Over a hundred tax-themed campaigns observed in 2026 delivered malware, RMM payloads, fraud, and credential-phishing lures, predominantly targeting the United States but also Canada, Australia, Switzerland, Japan, and others.
- RMM tools (Datto, N‑Able, RemotePC, Zoho Assist, ScreenConnect) were the most common payloads, abused because they are legitimate enterprise software that can evade detection if allow-listing is not enforced.
- TA4922 (likely East Asia–based) delivers Winos4.0/ValleyRAT ecosystem components, information stealers and fraud efforts, frequently impersonates tax authorities, and requests phone numbers to move communications out-of-band.
- TA2730 focuses on credential harvesting for investment accounts, often using W-8BEN lures and counterfeit authentication pages to capture credentials across multiple countries (e.g., Switzerland, Canada, Japan).
- BEC actors used W-2/W-9 and executive impersonation lures to request employee tax forms, aiming to collect sensitive personal and financial data for identity theft and follow-on fraud.
- Proofpoint telemetry contains numerous IOCs including sender and reply-to email addresses, payload URLs (Bitbucket and other hosted URLs), phishing landing domains, SHA256 hashes, and C2 infrastructure (IP:port).
MITRE Techniques
- [T1566.002 ] Spearphishing Link – Phishing emails used links to deliver executables or landing pages (“‘Messages contained a hyperlinked button purporting to be a “Transcript Viewer” that was actually a Bitbucket URL leading to an executable file'”).
- [T1566 ] Phishing – Broad phishing/impersonation lures were used to harvest credentials and prompt follow-on actions (“‘Emails contain URLs leading to counterfeit investment account authentication pages designed to harvest user credentials.'”).
- [T1204.002 ] User Execution: Malicious File – Payloads required user execution to install RMM or stealers (“‘which, if executed, installed N-able RMM.'”).
- [T1105 ] Ingress Tool Transfer – Adversaries hosted and fetched tooling/executables from external URLs (e.g., Bitbucket, upsystems) to deliver payloads (“‘Bitbucket URL leading to an executable file which, if executed, installed N-able RMM.'”).
- [T1219 ] Remote Access Software – Legitimate RMM products were abused to gain remote access and persistence (“‘Proofpoint has observed tax-themed campaigns deliver RMMs including Datto, N-Able, RemotePC, Zoho Assist, and ScreenConnect'”).
- [T1071.001 ] Application Layer Protocol: Web Protocols – Malware used web protocols for command-and-control communications (C2 observed on ‘121[.]127[.]232[.]253:8443’).
- [T1589 ] Gather Victim Identity Information – Impersonation and inclusion of real organization contact details increased believability and aided targeting (“‘Notably, the actor included a real phone number belonging to the IRS to further the social engineering and believability of the email.'”).
Indicators of Compromise
- [Email addresses ] TA4922 sender and reply-to addresses – Aubrey162243her@hotmail[.]com, YObutler.jonasd8nC29@yahoo[.]com, and many additional TA4922 sender emails.
- [Domains ] TA2730 phishing landing domains – bksgcefzqyb[.]com, whghfpytehu[.]com, and several other phishing domains (e.g., akcjdrya[.]com, buwxkiy[.]com).
- [URLs / Payload URLs ] Delivery hosts and executables – hxxps[:]//bitbucket[.]org/pmlasobjekightailsians/rgww/downloads/amzn-s3-EfinTranscriptViewer.cm10_14_4_.EXE, hxxps://www[.]upsystems[.]one/Alex[.]exe.
- [File names ] Executable payload names observed – Alex.exe, amzn-s3-EfinTranscriptViewer.cm10_14_4_.EXE.
- [File hashes ] Malware SHA256 hashes – d338a7f85737cac1a7b4b5a1cca94e33d0aa8260548667c6733225d4c20cb848, 844202972ff19afa760447fc87963de0fbbc0ebc69d50164f03ecf5d4e67952f.
- [IP address:Port ] C2 infrastructure – 121[.]127[.]232[.]253:8443 (TA4922 information stealer C2).
Read more: https://www.proofpoint.com/us/blog/threat-insight/security-brief-tax-scams-aim-steal-funds-taxpayers