Cybercriminals are targeting ScreenConnect cloud administrators with sophisticated phishing emails designed to steal login credentials and MFA tokens. This campaign is linked to ransomware operations, emphasizing the importance of enhanced security measures for high-privilege accounts. #ScreenConnect #ConnectWise #EvilGinx #QilinRansomware #MFA
Keypoints
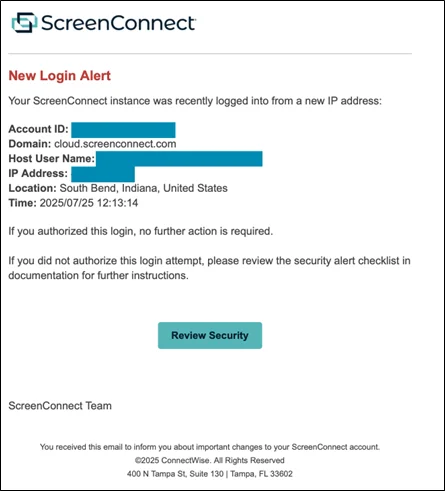
- Hackers are sending spear-phishing emails to IT professionals with elevated ScreenConnect privileges.
- The attackers use the EvilGinx framework to create convincing fake login pages that can intercept credentials and session cookies.
- This campaign appears connected to Qilin ransomware, using stolen credentials for initial access to deploy malware.
- Managed service providers are prime targets, as their access can compromise multiple client organizations.
- Organizations should implement stricter access controls, multi-factor authentication, and activity monitoring to prevent breaches.