A joint advisory attributes an ongoing Russian GRU cyber campaign to Unit 26165 (tracked as APT28/Fancy Bear), targeting Western logistics and technology companies that support aid to Ukraine through spearphishing, CVE exploitation, and deployment of malware such as HEADLACE and MASEPIE. Agencies warn the campaign is persistent and expanding across air, sea, and rail supply chains, urging organizations to enforce MFA, patch known vulnerabilities, monitor for lateral movement, secure internet-facing systems and connected cameras, and review partner relationships to reduce exposure. #APT28 #HEADLACE
Keypoints
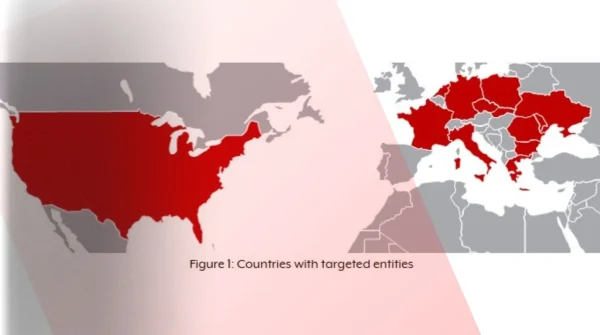
- Russian GRU Unit 26165 (APT28) is targeting logistics and tech firms supporting aid to Ukraine.
- Attackers rely on spearphishing, credential guessing, brute force, and multi-stage redirects to gain access.
- Known CVEs exploited include CVE-2023-23397 (Outlook), Roundcube vulnerabilities, and CVE-2023-38831 (WinRAR), with malware like HEADLACE and MASEPIE used post-exploitation.
- Post-compromise activity includes reconnaissance, RDP and lateral movement, email permission manipulation, and data exfiltration focused on shipment and transport details.
- Agencies advise enforcing MFA, patching systems, monitoring for unusual logins and lateral movement, securing IP cameras, and auditing supplier relationships.
Read More: https://thecyberexpress.com/russian-gru-cyber-campaign-targets-logistics/