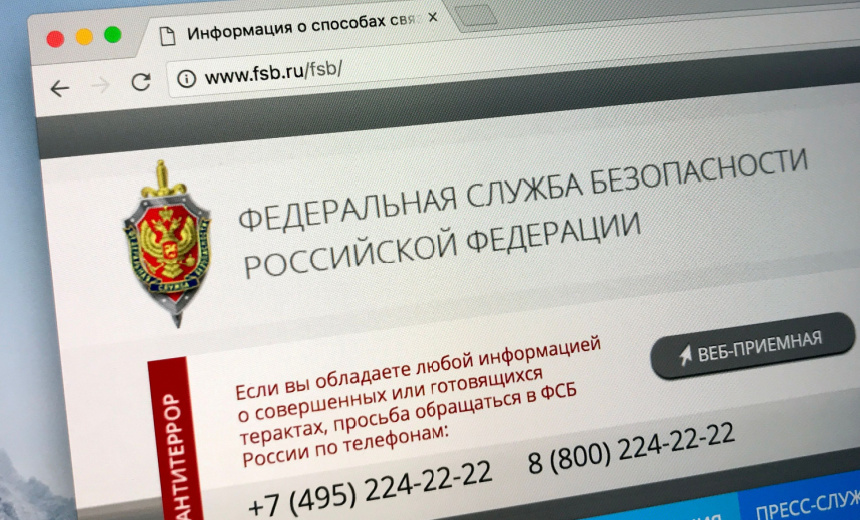
Russian cyber espionage group Coldriver, linked to the FSB, is utilizing a new malware called “Lostkeys” to target Western officials, NGOs, and journalists through sophisticated, multi-stage attacks. This campaign marks an evolution from credential theft to full system infiltration, with indicators of ongoing activity since late 2023.
Affected: Western government officials, NGOs, journalists, think tanks, individuals with ties to Ukraine.
Affected: Western government officials, NGOs, journalists, think tanks, individuals with ties to Ukraine.
Keypoints
- The Coldriver threat group, associated with Russian FSB, is deploying “Lostkeys,” a sophisticated malware for espionage targeting Western entities.
- Losskeys employs a multi-stage infection chain, including social engineering techniques like fake Captcha pages and PowerShell payloads.
- The malware is designed for data exfiltration, system information gathering, and evasion of sandbox environments.
- Targets primarily include Western officials, NGOs, journalists, think tanks, and individuals involved with Ukraine.
- Activities suggest ongoing operations since December 2023, with detection in early 2024 indicating persistent threat activity.
- Coldriver previously used similar malware strains like Spica, demonstrating advancements in attack capabilities with Lostkeys.
- Global intelligence agencies including the UK, US, and Europe have issued warnings and sanctions against Coldriver members associated with these cyber operations.
Read More: https://www.bankinfosecurity.com/russian-fsb-hackers-deploy-new-lostkeys-malware-a-28367